

Anyone who has an ATM card will be familiar with the two-step authentication needed before you can withdraw cash – your bank card and a PIN code. This is known as multi-factor authentication (MFA) and is now common practice in a number of arenas, including acquiring access to facilities and into company IT systems. Does MFA really provide the levels of security we commonly believe it does, or are we still vulnerable?
The types of authentication include PIN codes, passwords, RFID cards, tokens and biometrics (fingerprint, vein, palm, ear, facial recognition and iris recognition). According to Deon van Rensburg from ViRDI Distribution, HID recently released an authentication tool that is similar to the security certificates one sees on online payment sites. These certificates are sent to a user’s phone and are automatically scanned to the reader using near field communication (NFC). Another tool that a number of access control manufacturers are currently investigating is Samsung’s iBeam technology which uses existing secure Bluetooth technology, so no new hardware or electronic development will be required.
Zane Greeff of Elvey says that although tags and PIN codes are the two most common items, because they belong to the same authentication factor (knowledge), they are considered single-factor authentication (SFA). He adds that it is because of their low cost, ease of implementation and familiarity that PIN codes that have remained the most common form of SFA, but tags and PIN codes are not very secure. Multiple challenge-response questions can provide more security, depending on how they are implemented, and standalone biometric verification methods can also provide more secure single-factor authentication.
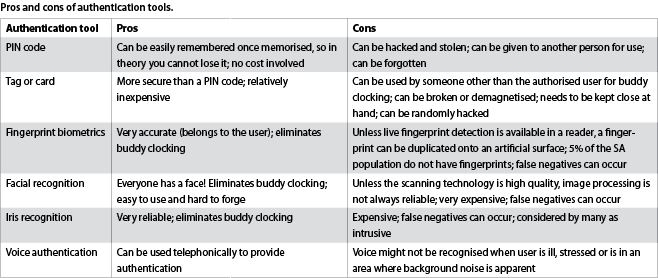
Alternatives with pros and cons
Brian Wynberger of Reditron says that the issue that arises with PIN codes is that they need to be random enough so that they cannot be easily guessed by a third party, but they also need to be simple enough to remember. Forgetting them often entails a waiting period while the system generates an alternative temporary password which will then allow the user to create a new password.
The problem with tokens or cards, he says, is that users need to be completely educated on their use and they can be easily lost or misplaced. Biometrics offer a more secure alternative, but if there are issues with scanner quality, false negatives or lack of user education on the use of the technology, delays in the flow through of pedestrian traffic will occur.
So is MFA really necessary? In spite of the pros and cons of each of the individual elements (see Table), the more elements that are introduced into the equation, the harder it will be for an intended intruder to gain access into an area. The number of factors used will be dependent on the identified risks and budgetary constraints. In higher risk areas, generally, there will be more factors in the MFA equation.
Best practice
Best practice in even the least risk prone areas is to have a lower level authentication together with one or more biometric authentication modes. Van Rensburg says that ViRDI adopts a multi-modal approach to authentication whereby fingerprint biometrics with live finger detection and vein readers connected to a facial recognition system. He recommends an RFID card used in conjunction with this multi-modal approach plus a PIN code. This he says provides 25 different options for customers.
Greeff says that an attacker may occasionally break an authentication factor in the physical world. A persistent search of the target premises, for example, might yield an employee card or an ID and password in an organisation’s trash, or carelessly discarded storage containing password databases. If additional factors are required for authentication, however, the attacker would face at least one more obstacle.
Wynberger says that single-factor authentication is archaic as new and more ingenious threats and vulnerabilities become prevalent. There is a 30% less probability of attack when one adds a password to an authentication process (say an RFID tag) and the threat is reduced down to 1% if one adds biometrics to the mix. Adding more factors will eventually reduce the risk to close to zero. Percentages mentioned above are merely for illustration purposes.
Speed of entry and exit also needs to be factored into the decision making process and this obviously needs to be balanced against adding additional time-consuming authentication processes to the equation.
Managing authentication
Managing MFA is another area that needs to be considered. Generally, most systems use proprietary software provided by the supplier, with enrolment taking place using a supplier database protocol. Monitoring and reporting can be undertaken through a third-party software supplier but this can cause issues because any reader updates may not be supported by this. Wynberger says that the systems need to be deeply integrated to ensure both the success of the MFA system as well as its longevity of use.
He feels that a building management system (BMS) may dilute the efficacy of an authentication device’s features due to the sheer size of the BMS. In general, he says, a BMS would merely consider what time a person clocks in and out, neglecting other important issues.
Greef says that one may find proprietary software and management in a secure environment that may or may not include building management modules like elevator access and level access, alarm arm and disarm functions. He adds that Impro caters for use of these factors to assist with building management in terms of time triggered events, for example, to arm an alarm at a specific time.
Choosing what factors/elements work for your specific environment and needs depends largely on whether the environment is a secure or high-secure area. Greeff says that Impro provides a selection of input and output modules that may be used to, for example, only provide the presented tag holder with access to a selected floor in a building that he/she has been pre-authorised to enter.
Francois Lottering of Reditron says that there is a diverse array of technologies available on the market which make MFA feasible and sustainable. The secret is choosing the right supplier and the right combination of technologies. He cites exciting products such as the Ievo range of biometric fingerprint readers that can read down to the fourth layer of skin, making them ideal for people who have damaged fingerprints on a dermal level or users wearing latex gloves. Another is the ViRDI AC7000 reader that considers facial recognition, fingerprints, RFID card and PIN in one package.
For more information contact:
Virdi Distribution, +27 (0)11 454 6006, deon@virditech.co.za, www.virditech.co.za
Reditron, 087 802 CCTV (2288), marketing@reditron.co.za, www.reditron.co.za
Elvey Security Technologies, +27 (0) 11 401 6700, info@elvey.co.za, www.elvey.co.za
| Tel: | +27 87 802 2288 |
| Email: | marketing@reditron.co.za |
| www: | www.reditron.co.za |
| Articles: | More information and articles about Reditron |
| Tel: | +27 11 401 6700 |
| Email: | info@elvey.co.za |
| www: | www.elvey.co.za |
| Articles: | More information and articles about Elvey Security Technologies |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.