
NEC XON has created a Know Your Customer (KYC) solution to help mobile network operators and financial services businesses comply with legislation while cutting the costs, time, and resources usually associated with issuing SIM and bank cards.
Doing so helps them improve customer service and provide their value-added services on top of the physical product that much faster.

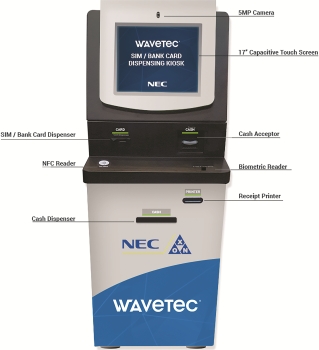
“The solution can be customised to accommodate relevant legislation and also helps update, maintain and serve the needs of identity systems such as national identification, immigration, social services and others,” says Grahame Saunders, business head of Biometrics at NEC XON. “The physical device that can then be used for SIM and issuing bank cards is a self-service kiosk the size of an ATM and integrates with the business systems these organisations use.”
He says the system quickly moves the customer’s subscribers or clients through the regulated process of collecting their personal details together with their biometrics. The process also creates an updated central repository of subscriber information. Various workflows can then reuse the data as allowable, applicable and commercially viable.
It then issues the SIM or bank card automatically, like a vending machine, and transmits the necessary data to back-end systems to activate the SIM or bank card.
“The physical device, like those of our customers, becomes a gateway to value-adding services,” says Saunders. “This solution also provides a central data repository to audit active users, the capability to audit for legislation, enables offline registrations, provides a centralised database of blacklisted users and can be used to blacklist devices, users and SIMs. It can be deployed almost anywhere it’s needed for indefinite periods, provides convenient services to travellers to a country where legislation allows and can automatically deactivate SIMs when visitors leave, and can deduplicate data.”
NEC XON partnered with Wavetec for its KYC solution. Wavetec is a multinational IT company that designs and manufactures enterprise queue management, information displays and self-service kiosk solutions for mobile network operators and banks.
Saunders says his engineers developed the integration APIs on standardised SOA technologies to facilitate integration into customer business systems, which future-proofs the solution and supports the customer’s business flexibility.
Out-of-the-box functionality captures fingerprint, iris and facial biometric data using NEC’s software platform. Low-cost smartphone-type technology using Windows and Android technology, rather than bespoke biometric solutions, provides the physical interface and connects via a number of alternatives to back-end systems.
| Tel: | +27 11 237 4500 |
| Email: | [email protected] |
| www: | www.nec.xon.co.za |
| Articles: | More information and articles about NEC XON |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.