

Motivation
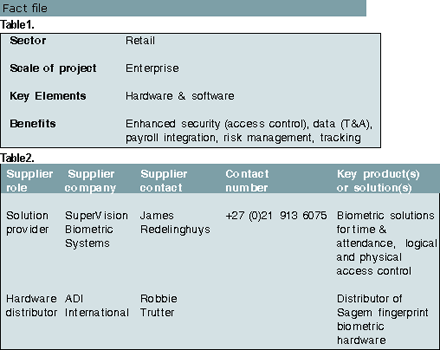
Midas Group, distributor of branded automotive parts, services and accessories in southern Africa, has its head office in Meadowdale, Johannesburg and regional distribution centres in Durban and Port Elizabeth. Through its four national franchise brands it has a network of 320 retail outlets, workshops and fitment centres across the region.
The company decided to review its time and attendance (T&A) and access control systems throughout the organisation primarily because it wanted a central database that could feed its T&A and access control data directly into the centrally-run payroll package, Accsys.
In some outlets, T&A data was captured through manual registers and then captured into spreadsheets, which were sent through to head office for approval. A mix of punch card and proximity card systems were in operation at other sites.
Ross Dyer, national operations manager at Midas comments, "Delays in collating this variety of data meant that the company had no accurate and up-to-date numbers for normal and overtime staff hours. Overtime data often arrived long after costs had been incurred, so we had no ability to take action before the event.
"The potential for card abuse in our access control systems using proximity readers was also identified as an unacceptable risk where millions of rands worth of branded automotive components were passing through the system every day."
Rewards
Midas' main requirement was to enhance access control procedures and ensure T&A data was electronically captured in a single format and sent through to head office regularly.
An internal project team was formed to define requirements. Ross Dyer led the team that included personnel from HR, operations and security.
Although biometric technology seemed an obvious choice, the diversity of Midas' operations ranging from distribution centres employing hundreds of staff to stores with fewer than 10 employees, raised questions as to the cost-effectiveness of this technology.
Another major concern was, according to Dyer, "Finding a process-driven solutions provider capable of providing a national installation service that conformed to a defined methodology."
After an initial specification document was drawn up, SuperVision Biometric Systems was asked to advise on the practicalities of Midas' solution and to create a deployment plan.
The SuperVision team, under the guidance of director James Redelinghuys, was able to demonstrate to Midas similar solutions it had provided to other retail sector clients.
Implementation
After further consultation, Midas accepted SuperVision's proposal to implement a fingerprint biometric solution using Sagem terminals to record T&A data for over 1000 members of staff working at 19 distribution centres and wholly-owned retail outlets in South Africa.
Redelinghuys explains that: "SuperVision proposed that the most cost-effective solution for Midas would be to add a variety of Sagem fingerprint biometric terminals into its existing T&A and access control systems."
Pure access control areas, including the server room and staff turnstiles at Midas' Meadowdale headquarters, were fitted with MA100 biometric readers. MA200 biometric terminals were installed at T&A points in the distribution centres and larger retail outlets.
In the smaller stores, where it was difficult to justify the expense of installing standalone biometric terminals, MSO1300 USB biometric readers were connected to existing PCs. These make use of SuperVision's web-authentication software.
"This solution allows staff to scan locally. The biometric template is then sent across the WAN to a central server where an authentication is made. A clocking log is centrally created and feedback is sent back down the WAN to the PC where the user scanned," explains Redelinghuys.
Challenges
The first stage of the implementation centred on communicating news of the project to staff. Dyer comments, "Change management is a critical part of any process and, if mishandled, often provides the greatest obstacle to the successful implementation of technology. SuperVision assisted Midas in communication with unions whose representatives were concerned about the security of providing fingerprint templates to company management."
During the planning phase it was agreed that the implementation should be staggered - starting with head office and then moving out to the remaining distribution centres and stores. This had the dual benefit of allowing the system to be tested in a controlled environment while sending a clear message to the decentralised stores that head office was taking the project seriously and expected them to do likewise.
| Tel: | +27 12 667 3232 |
| Email: | [email protected] |
| www: | www.fourierit.co.za |
| Articles: | More information and articles about Fourier IT Innovation |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.