
What is ‘high’ security, and who should have it? Certain building types, such as data centres, utilities, healthcare and governmental offices, of course require an industrial-grade, high security, access control system.
Many more organisations - for example financial institutions, schools, retail stores and companies with sensitive documents, executive suites, multitenant space, warehouses or manufacturing - are finding it necessary and desirable to ensure their buildings are not just secure, but highly secure. Not only is it a practical matter, but it also offers employees piece of mind and tells the world 'this company takes security seriously'.
In choosing a security system vendor, look for a manufacturer that specialises in high security. Avoid the low-price lure of companies that offer low-end security or residential systems and be cautious of the conglomerates that make toasters in addition to security systems. Also, look for a manufacturer that utilises in-house development and a proprietary motherboard, rather than a vendor that purchases the identical OEM board shared by many other manufacturers.
A security system should offer, 'off-the-shelf', the features and flexibility to enable customers to meet the unique requirements of their facility, without forcing them to pay for expensive custom development. Buyers should demand the following high security features:
Reliability: you cannot have high security unless you have high reliability. Ask about the system's mean-time-between-failure rating, and ensure the system continually monitors its own status and condition from end to end.
Distributed processing and distributed features: your personnel database, access privilege settings, system features etc, should be resident in the access control panels, not just the computer. The security system should operate non-degraded even if the IT network or server communication is interrupted.
Threat levels and lock downs: when national or local threat levels change, you should be able to alter your system's behaviour and access paths with a single mouse click.
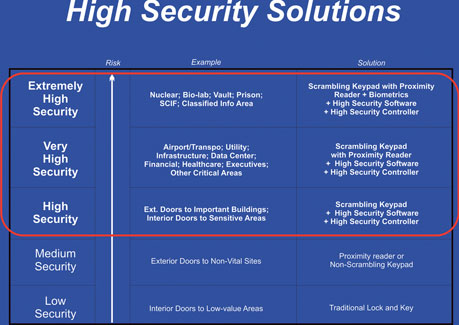
Advanced readers: utilise scrambling keypads or keypad-prox reader combination devices to deliver high security right at the door. For highest security areas, consider biometrics combined with a scrambling keypad.
Visitor management: know who is in your building. Scan their ID information into the security database, badge them, and then ensure they left the building.
Additional features: UL certifications (294, 1076AA), SCIF-approved, end-to-end encryption, duress, anti-passback, two-person rule, door interlock applications such as man traps, tagging, deadman timer, 2% line supervision to detect tampering, redundancy and interoperability with other systems are all features required for high security.
If your company-type is a perceived target or if you want to avoid incidents, comply with regulations, reduce liability and ensure the safety of your people and property, choose an access control system that offers the built-in features and reliability that ensure a highly secure organisation.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.