
Eco Time Technology recently launched the Visitor Management System (VMS), designed in South Africa by CapeSoft. VMS is a paperless system to control and manage visitors to your business premises. It does away with visitors having to sign registers or visitor sign-in books. Visitors can now sign in digitally via a touchscreen at your reception, or if a more mobile option is needed, an iPad or any other tablet can be used. If you require visitors to carry identification, VMS can print a customisable badge with the visitor’s photo and your company logo.
VMS maintains a database of all the visitors registered on the system. Visitors can be classified as a new visitor or returning visitor. The visitor’s experience is fully customisable, depending on your business requirements. Some of the customisable options are contact details, company name, reason for the visit, vehicle registration, sign in for a group, equipment declaration (including serial numbers) and many more.
VMS uses photos for easy and quick navigation and identification. All the necessary information for a returning visitor will be stored in the database which means they can be processed quicker. This also means you can track how many times this visitor has been to your premises over a certain period.
Some of the key features of VMS:
• Central visitor application to track visitors.
• Customisable user interface to match your company profile.
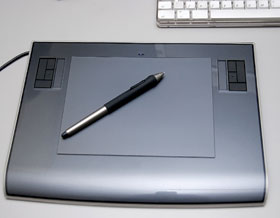
• Supports touch screens and/or tablets.
• Single visitor and/or group registrations.
• Optional integration with CS Time, Eco Time Technology’s time and attendance and access control software.
• Access rights in CS Time to restrict visitors to certain areas.
• Automatic e-mail notification to person being visited that visitor has arrived.
• Photo capture capability.
• Print visitor labels. Labels can be customised.
• Auto e-mail notification if visitor has not left your premises by the captured departure time.
• Visitors currently on site report.
• Visitor hardware declaration i.e. laptops, tablets including capture of serial numbers.
• Visitors visit history.
If you are a Eco Time client that utilises the latest version of its time and attendance and integrated access control system, the visitor management system can be coupled to this and visitors may then be restricted to certain areas. Visitors can only be authorised by security or reception.
VMS was recently implemented successfully at Peninsula Beverages in the Western Cape. Peninsula Beverages use touchscreen, wall-mounted PCs (kiosks) where new visitors can register or previous visitors can sign in. The registration process is quick (less than 2 minutes) with very little intervention required from security.
For more information contact Eco Time Technology, +27 (0)21 531 6699, [email protected]

© Technews Publishing (Pty) Ltd. | All Rights Reserved.