
After the announcement that iPhone jailbreaking has become legal in US, a malware-spreading campaign targeting the 'iPhone unlocking' fans goes to confirm that cybercriminals never lack imagination.
Owners of iPhones are one step closer to taking total control of their widgets, after US pronounced legal the practice of 'jailbreaking', on Monday, 26 July 2010.
This means that anyone can jailbreak or unlock any cellphone without fear of legal consequences. Still, iPhone unlocking fans should pay attention to the software they download for this operation, because cybercriminals never sleep.
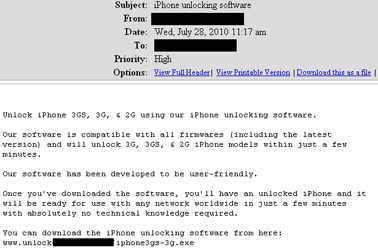
And this is how the story goes: you receive an e-mail in which you find out that you might get a new application for iPhone jailbreaking. All you have to do is click a link that will take you to the web page on which the desired software awaits you.
As you go further into this labyrinth and click the link, an exe file attempts to download onto your computer. But once saved and run, the executable opens up the way for a nice Trojan.
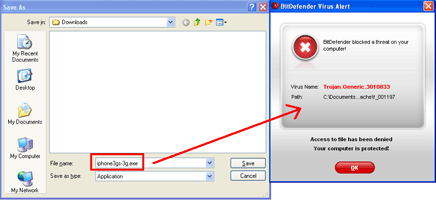
Identified by BitDefender as Trojan.Generic.3010833, this piece of malware is a keylogger that transmits everything the user writes on the computer to a specific e-mail address, in this particular case to directory[REMOVED]@hotmail.com.
This allows the malware creators to intercept the victim’s visited sites, usernames, passwords, bank accounts information, such as pin number, bank account numbers, passwords, etc.
In order to stay safe, never open suspicious links or attachments without scanning them first. Install and update a complete antimalware software solution.
For more information contact Alina Anton, senior PR and marketing coordinator, EMEA & APAC Business Unit, BitDefender, +40 212 063 470, [email protected], www.bitdefender.com

© Technews Publishing (Pty) Ltd. | All Rights Reserved.