
BitDefender v2011 has entered the BETA phase and it has been made public.
This is an opportunity for testers to get an exclusive preview of BitDefender's upcoming release, and to play an active role in helping BitDefender build better products. Among this year's prizes BitDefender gives away one Apple iPad and one Nintendo Wii.

What is new in BitDefender 2011:
New Redesigned and streamlined installation. You install and configure BitDefender 2011 in one step without having to reboot your PC. It detects viruses before installing BitDefender and cleans your computer to ensure optimal usage from install time.
New Search Advisor warns you about unsafe pages displayed in search results by checking each URL against the BitDefender online URL database.
New Firewall Troubleshoot Wizard guides users and solves most common problems related to Internet, printer or remote office (VPN) connectivity.
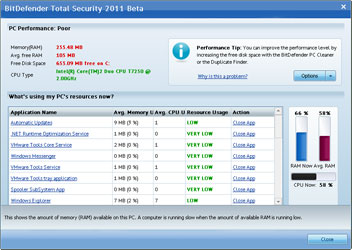
New Performance Optimiser shows which applications are slowing down the PC and suggests corrective actions. The Optimiser includes memory and CPU usage gauges that show the last 60 minutes activity for each application running on your PC.
New The protection level adapts to the processing power of your computer by adjusting settings to match the available memory and CPU type. This allows the user to be fully protected without slowing down the computer.
New Basic and intermediate users can customise the dashboard by adding shortcuts to their favorite sections or actions.

Improved Smart Schedule provides maximum performance with system load analysis so tasks like on-demand scanning are suspended, to free-up resources for other processes, such as a media player or games.
Improved Improved usability with typical (easy) vs custom tune-up options.
Improved Select the interface that best matches your security needs and knowledge. Basic, Intermediate, and Expert users can select the interface that best suits their needs. Most sections of the product have been redesigned to support basic and intermediate users.
The press release has been published on the BitDefender website, at this link: http://www.bitdefender.com/NW1603-world--BitDefender-2011-Beta-Just-Released.-Test-Now-and-Win.html
For more information contact Alina Anton, senior PR & marketing coordinator, EMEA & APAC Business Unit, BitDefender, +40 212 063 470, [email protected], www.bitdefender.com

© Technews Publishing (Pty) Ltd. | All Rights Reserved.