

This article is a shortened overview representing the views and experience of Dolf Scheepers on copper theft on South African mines.
The provision of security services on mines in South Africa is complex in a country consistently portraying complexity, intolerance and political rivalry in various sectors. South Africa is a world-leader in mining. The country is famous for its abundance of mineral resources, accounting for a significant proportion of world production and reserves, and South African mining companies are key players in the global industry.
The mining sector spans the full spectrum of the five major mineral categories – namely precious metals and minerals, energy minerals, non-ferrous metals and minerals, ferrous minerals, and industrial minerals. Obviously they require key security role players supporting them as well.
The private security industry, as a leading supplier of services to mining, is a world class industry experienced in the challenges of the mining and other industries. In what is estimated as a R40 billion industry, world-class practices developed in line with mining houses – especially high-risk refineries, smelters, plants and diamond sorting houses. The size of protection services in mining is not known, but industry specialists estimate the monthly spend on security to be around R180 million (including in-house) with the possible deployment of up to 23 000 security officers on about 290 mines – an unconfirmed and challenging future research task.
Crime: an ongoing problem causing a major irritation
Crime in mining operations is mainly characterised by theft of product in refinery to final product stages, hi-jacking style product in-transit theft, explosives theft, copper bearing commodity theft such as cable theft, diesel, material theft from stores, tools and equipment and various smaller but valuable item theft. In many instances is the value of loss far less than the implementation of new and stringent security measures and mining houses often opt to accept a risk rather than to manage the risk through improved security measures. Another category of crime is white collar crime or the so called ‘silent crime’ in procurement processes prevalent in many mining operations.
In this article we focus on cable theft, which in South Africa is estimated to cost the economy more than R16 million per month (stats based on Telkom, Transnet, Eskom and inner city centre cable losses) according to the South African Chamber of Commerce and Industry’s (SACCI) stats which presume to exclude theft from mines.
“The consistently high price of copper makes it a valuable commodity for illicit business,” says John Cross, chairman of the Copper Producers’ Association. What drives the price up is massive demand from China and India, whose urbanising economies are major consumers of copper.
Copper is also widely available, poorly secured and easy to steal due to the extensive and distanced power networks of mines. It is also easy to sell despite what seem to be controlled processes. There are thousands of scrap dealers or ‘bucket shops’ willing to trade in illicit copper. SA also exports about 350 000 tons of copper scrap each month.
SACCI noted that factors contributing to the difficulty in combating non-ferrous metal theft include:
* Weak export control measures and weak inspection measures of containers.
* Other factors are the rising longer-term price of copper and increasing demand both domestically and internationally, which make theft a lucrative illegal business.
* The involvement of organised groups and syndicates and the absence of appropriate regulation to control processing, sale, import and export of non-ferrous metals are also issues.
Copper cable theft by criminally-minded community members who are mostly collaborators to syndicates, is growing whilst internal theft by criminally minded mining staff and contractors remains to be the order of the day. Desperation to succeed in cable theft attempts is highlighted by the violent armed incidents linked to attacks on security officers.
On the night of 2 October 2011 for example, four heavily armed criminals (not even hiding their identity with balaclavas) entered a coal mining site in Mpumalanga, tied up the two security officers and stole as much copper as they wished. Open and unprotected and even abandoned cable is lucrative to the would-be criminal who would execute these operations predominantly at night in groups of up to 15 criminals, cutting lengths of cable in excess of 100 metres at a time.
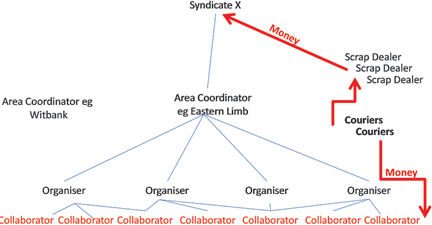
Criminal modus operandi in especially the Eastern Limb of the Bushveld Complex (the Lydenburg, Burgersfort, Steelpoort Areas in Mpumalanga and Limpopo Provinces) can be summarised as follows:
* It is the ill-informed, opportunistic small-scale criminal operating ‘on his own’ that would steal copper or brass on a small scale and sell at local scrap dealers for financial survival. It is the person that would lay his hands on cable at the mine or smelting plant in small quantities of 10–20 kg (if that much) and sell at irregular intervals as and when obtained. The removal is either on the body (wrapped around), in a sling bag covering the back of the body or with weak security in a carry bag knowing not to be searched. The wearing of jackets or coats in summer is always an indication of copper or brass hidden on the body.
* Well-organised syndicates have a web of operators traditionally recruited from unemployed local communities, stealing cable from various mines selling the stolen cable in areas of more than 150 km from the point of theft.
* Access to cable at mines is fairly easy as it is a commodity not always properly safeguarded, especially abandoned unused cable.
Traditional guarding has to make way for special copper cable theft prevention measures, although proper risk management sometimes guides mining houses to accept and tolerate the risk rather than to invest in increased and costly security measures.
Poor controls at, and collaboration by, scrap dealers, an ineffective justice system allowing cable thieves to get away with admission of guilt penalties and difficulty of claiming proof of cable ownership adds to the poor state of affairs and growing cable theft incidents. If cable is not secured, dug in or reinforced with concrete or guarded, then it is stolen.
Intelligence gathering and analysis on cable theft syndicates is the order of the day despite a requirement to have stringent discipline in the storage and control over scrap copper as well as the protection of cable in high risk areas on mines. The challenges in the cable theft intelligence cycle are:
* The infiltration of the syndicate leaders who are traditionally deployed far and remote from mining areas and probably in city centres – they are never found near mining areas.
* The arrested criminals (collaborators) on mining operational levels are traditionally remote from the rest of the syndicate and thorough interrogation for purposes of gathering syndicate crime intelligence traditionally very difficult – they hardly ever know something about the syndicate.
* Secrecy on the courier, scrap dealer and syndicate leader levels are good because they are remote from the traditional mining areas.
Currently 90% of arrested cable theft thieves get away with the crimes due to the justice system and would probably get involved in cable theft again as it has become an income stream. It will continue to be problematic until such time that:
* The justice system accepts other charges such as sabotage and trespassing to replace charges for cable theft.
* The Second Hand Goods Act regulates the businesses of dealers in second hand goods in order to combat the trade in stolen goods.
* Copper is declared a precious metal.
* Mines introduce a copper safeguarding culture which is not only focused on the manned guarding company to protect copper, but the integration of mine operating and security procedures, physical security, electronic security and manned security has to be harmonised – alarms, beams, cameras are the order of the day
* High risk areas are protected with technology and or cable is secured in for example reinforced concrete conduits.
Overcoming turbulent times
A structured, well designed and planned security service based on operational principles is a requirement. Security managers will, based on proper risk assessments, design operational concepts supported by various products and services that would meet their unique protection requirements.
A Mining Security Design fitting in with a properly structured Group Security Policy could entail many or even most of the elements, as presented in the model designed by the mining security specialists in Thorburn Security Solutions.
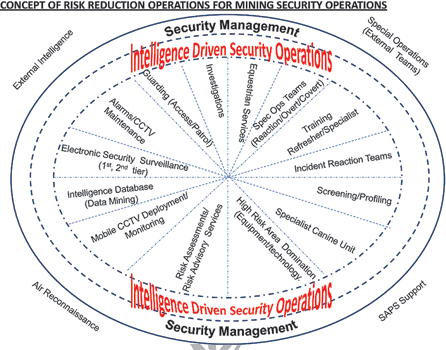
Intelligence Driven Security Operations, as highlighted in the Model for Mining Security, is an essential part of the modern mining security operation and stretches wider than the mining areas. Intelligence has become a commodity and a necessity which is to be structured separately from investigations departments. The purpose of intelligence is not to determine ‘who committed the crime,’ but is to have the foreknowledge of ‘where, when, in what strength and with what means stability at the mine will be influenced’ – also known as the Mining Security Intelligence Problem.
Intelligence is a science entailing a structured collection plan based on the expected risk, the collation of data in formats that would ease the analysis of the information to enable the security manager to make future predictions and plan operations accordingly – nowadays highly specialised data collation and link analysis systems, such as the Online Intelligence systems exists and is used by the major mining security companies. The days are past that intelligence is an investigations function – yes it is an investigations function to gather reactive crime information, but it is the tool used by the security manager to design, budget and predict future protection operations covering the direct mining area, the adjacent area influencing mining security as well as the more remote area of interest to mining operations.
Unfortunately these mining security initiatives are expensive and sponsored from profits whilst mining houses are becoming more price sensitive. It is sad to see that security companies are entering in a price war to raise top line revenue to increase market share which is to the detriment of the service providers being honest about service delivery. In the long run, mining houses will see the effect and a stagnation of the industry will occur over a period of time.
This is a shortened version of a paper by Dolf Scheepers on mining security and asset protection in South Africa. The full document can be found at www.thorburn.co.za/files/Mining_Security_and_Asset_Protection_in_South_Africa.pdf

© Technews Publishing (Pty) Ltd. | All Rights Reserved.