
With Internet Service Providers (ISPs) worldwide facing a serious challenge from malicious, organised networks of computers — or botnets – a new anti-botnet solution has been launched.
Botnets operate within a network, using a service provider’s infrastructure to distribute massive quantities of spam. Botnets are responsible for the distribution of up to 90% of the world’s spam and strike at a service provider’s core business assets: IP addresses, bandwidth and service reputation.
Despite ongoing closures of Botnets worldwide, spam continues to flow at an ever-increasing rate throughout the world. This activity is easily transportable and the potential profits mean that Botnets will continue to be a significant reality in the world of organised crime. As global broadband penetration rates increase and mobile/smartphone technologies become more accessible, ISPs and telcos face the increasingly complex challenge of providing reliable, efficient internet services.
In response, PineApp, a network security solution provider has released a carrier-grade solution able to scan and block unwanted or malicious outbound e-mail traffic. Easy to deploy, the PineApp Outbound Spam Guard (OSG) functions as a transparent proxy that communicates to the ISP— in real time and with granular level statistics — details of the IP addresses within their networks that are infected and being controlled by botnets. The company claims it can stop 99% of spam messages.
“By harnessing the power of PineApp’s OSG, an ISP can reduce blacklisted IPs, improve IP reputation and reduce unwanted consumption of bandwidth,” says Hilton Loewenstein of SeKure-IT, southern African distributors of PineApp solutions. “The OSG has already been deployed in ISP networks across Africa and Asia, with beyond-expectation success. A recent installation at an ISP in Thailand with over 1,2 million IP addresses is just one of the latest success stories illustrating how the OSG is addressing the Botnet scourge.
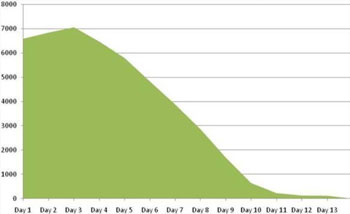
“This ISP was suffering from a major infestation that was leading to thousands of blacklisted IP addresses. Within 14 days of implementation, the OSG blocked up to 97% of all outbound e-mails – meaning that 97% of the ISP’s e-mail traffic was spam. Even more importantly, during that 14-day implementation period, the number of blacklisted IP’s was reduced to an almost insignificant amount. The OSG quickly and effectively secured the ISP’s infrastructure and customer e-mail-related complaints plummeted in just two weeks,” says Loewenstein.
The graph below shows the actual number of blacklisted IP’s reduced within 14 days of implementation.
“The PineApp OSG technology has been developed to address the requirements of the world’s largest ISPs and is capable of processing more than 40 million e-mail sessions per hour. Without compromising service continuity or quality, the OSG successfully blocks 99%, or more, of all unwanted outgoing e-mail messages,” concludes Loewenstein.
For more information, contact Hilton Loewenstein at SeKure-IT, on +27 (0)11 609 9495.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.