

Motivation
The University of the Witwatersrand (Wits), based in Johannesburg, is one of Africa's leading research and teaching institutions.
The university's old access control system was becoming slow and cumbersome to manage and was clearly in need of upgrading.
Giles Watermeyer, ICAM manager at Wits, comments, "The system had reached the end of its lifespan. Even though the system was incredibly powerful and flexible, we could not achieve the functionality that a university as large as Wits requires. With about 25 000 students and more than 5000 full- and part-time staff members, a dynamic, state-of-the-art system was required to serve the Wits community.
"One on the biggest drawbacks was the three- to four-day delay for an access change to take effect. This caused much frustration and confusion for security officers and users alike. Generating access reports could take as long as eight hours, which posed a huge problem for the investigation team as it was trying to resolve card faults.
Vendor support was no longer available for the system either. The university identified the need for a more advanced system to meet its needs and embarked on an extensive process of investigating alternative products and assessing the impact of implementing a new system. "The process took almost three years to complete as we followed a thorough process to ensure that we selected a product that met the various needs of the university," adds Watermeyer.
Rewards
Wits has very specific requirements of the system as it not only controls access but also manages the student meal programme as well as the campus 'Wits Bucks' programme for photocopying, printing and retail purchases. In addition, the system has to monitor certain alarm systems on the campus.
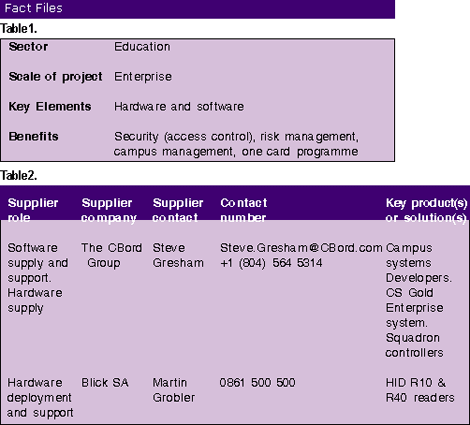
Wits drafted the specifications for the new solution after several meetings following a thorough analysis of the old system. Implementation was planned in consultation with three parties: Wits, CBord (the US developers of Wits' original solution) and Blick SA (security solutions providers).
The Wits project team was made up mostly of the group that is responsible for systems governance and included representatives from the major user groups of the system: libraries, catering services, security, finance and infrastructure.
Implementation
Consultants were used during the specification and tender process to ensure objectivity and compliance with procedures. Aside from that, the Wits team, which has the experience and knowledge of the inner workings of the needs and business processes of the University, drove the process. Thereafter, negotiations between the CBord Group and Blick SA were initiated and an implementation team was established
Success meters, defined by time lines and milestones for each task within the overall project, were developed. For example, the system was to be deployed over two weeks with only a three-day window of downtime. "In reality, there were only two hours of offline time for access systems and three days of downtime for financial systems, so this was a very successfully delivered task," comments Watermeyer.
Another deliverable that exceeded expectations was the conversion of the main access points. Grobler explains, "A timeline was approved that allowed a month of weekends to convert the four main gateways to the new system. This was achieved in three weeks without causing any significant disruption to the campus." During this period 67 readers and 40 controllers were upgraded.
Challenges
The selection and rollout of the new card technology was a major challenge to the project as Wits had to ensure that 50 000 cards were replaced before the first new reader could be deployed. As a result, the cards had to be rolled out from the beginning of the academic year. Custom applications were required to capture new data that the old system was not able to record.
Watermeyer comments, "The switchover was incredibly smooth with very few problems. Most IT deployments are plagued with the need to fix bugs before things start to work. In this case, the software was installed, the conversion was done and the biggest bug took a couple of hours to sort out."
Grobler adds, "The product selected is extremely configurable. The core system did not require any customisation but a fair amount of work was required to configure it to meet Wits' needs."

© Technews Publishing (Pty) Ltd. | All Rights Reserved.