
What would your life (or even a day) be like without all the amenities we take for granted? Our nation’s cities and critical infrastructure are almost totally reliant on the Internet.

A doomsday scenario could begin with waking up to no electricity and water. You attempt to contact the office, but all telecoms are down. Thank heavens you can get to the office you surmise, but alas not. Petrol stations are closed, all banking systems are offline, highways are snarled with out of gas or hacked vehicles. Supermarkets are being invaded and looted as panic sets in. Emergency services collapse with medical facilities in particular being forced to turn away patients.
As the days and weeks pass, money begins to lose its value and people begin to return to trading in gold and other precious commodities. The black-market booms and simple items such as batteries, LP gas, solar panels, bottled water, etc. suddenly begin to be much sought-after items.
Impossible you may say. However, unless we all play our part to protect our infrastructure, the above is a very real scenario.
Just ask Ukrainians who received a small dose of state sponsored attacks from 2015 onwards. Virtually every sector of their nation’s critical infrastructure has been targeted, namely energy, media, military, finance and political system.

Safeguarding the nation’s critical infrastructure
The health, safety, security, economic well-being of citizens, effective functioning of government and perhaps even the survival of the industrialised world relies heavily upon interconnected critical systems. A country may experience widespread disruption, or even experience loss of human life if these systems become inoperable.
The reliability, stability and protection of interconnecting information infrastructures have become key to the operation of a nation’s critical systems. National Critical Information Infrastructures (CII) include information infrastructures, which support essential components vital to a national economy.
They usually comprise of a number of different infrastructures, interconnections and critical information flows between them. Traditionally closed Operational Technology (OT) systems are now being given IP addresses. Terms such as Industry 4.0, artificial intelligence, autonomous vehicles and Internet of Things (IoT) are now opening up all sectors to cyberspace. This allows cyber threats to make their way out of traditional back-office systems and into critical infrastructures such as power generation, transportation and other automation systems. Like all developing countries, South Africa has an increasing number of interconnected electronic systems.
Not only a challenge for government
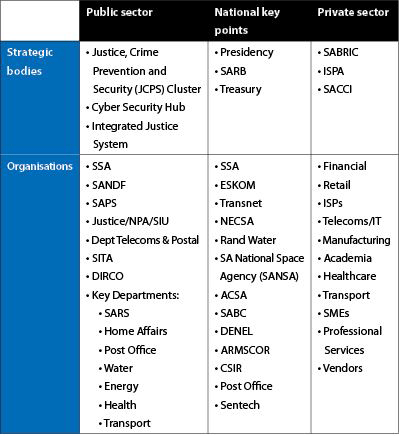
Due to mounting pressure from both external and internal threats, South African organisations responsible for critical infrastructure need to have a consistent and iterative risk-based approach towards identifying, assessing and managing cybersecurity risk. This needs to become a priority, regardless of the organisation’s size, threat exposure or cybersecurity sophistication. Table 1 highlights key critical infrastructure stakeholders across the public and private sectors in SA.
An approach for securing our critical infrastructure
Although South African organisations have made great strides in information security in general, additional measures are needed to protect our national CII.
1. Prevent
Utilise a Threat Intelligence approach to predict the most likely attacks, targets and methods. Prevent or deter attacks so that no loss is experienced. Develop organisational understanding in order to manage cybersecurity risk to systems, assets, data and capabilities. Develop and implement the appropriate safeguards to ensure delivery of critical infrastructure services.
2. Detect
Develop a capable threat detection capability: trained staff, appropriate monitoring processes and implement technology to identify vulnerabilities or the occurrence of a cybersecurity event.
3. Respond
Utilise an effective incident management framework and establish a business-aligned incident response team. Develop incident procedures, ‘battle guides’ and run simulation exercises to allow a rapid response to incidents.
4. Recover
Develop and implement the appropriate activities to maintain plans for resilience. Restore any capabilities or services that were impaired by a cybersecurity event.
Valuable lessons learned
Critical Information Infrastructure Protection (CIIP) is the shared responsibility of both the public and private sector.
• The most effective way to secure a business is to use a combination of layered cyber and physical information in addition to human security measures.
• Measures should be proportionate to the expected threat and risk profile of your organisation, as well as the specific industry and location of operations.
• It is not possible to protect all assets at all times. Prioritise the key areas to protect first.
• Security is more cost effective when incorporated into longer-term planning.
For more information contact Wolfpack Information Risk, +27 11 794 7322, info@wolfpackrisk.com, www.wolfpackrisk.com
| Tel: | +27 11 794 7322 |
| Email: | info@wolfpackrisk.com |
| www: | www.wolfpackrisk.com |
| Articles: | More information and articles about Wolfpack Information Risk |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.