

Open Workspaces creates environments for working, meeting and innovating. The company has locations all over South Africa, allowing members access Open environments in different cities as they require. As a co-working space, Open needed to be able to control access to meeting rooms, conference rooms and auditoriums using a system that is easy to use, scalable and offers multi-site functionality.
When looking at an access control system that would meet its requirements, the business found that traditional access control solutions were too expensive as Open wanted to control every door in real time. In addition, as a premier location, aesthetics were important and many access control readers, whether biometric or tag based, are large and clunky. Open required seamless access control to match its design aesthetic. The company also found that traditional access control systems required dedicated hardware, skilled operators, clunky software updates.
The directors of Open then found SALTO KS and after a rigorous due diligence decided this was the solution to their access control problem. Open Workspace’s Mark Seftel says the benefits SALTO offered were varied, and include the following:
• Low cost per unit/door compared to traditional access control.
• Easy to manage and see who’s using what room at what time. An intuitive online web-platform makes using the system easy.
• Aesthetically pleasing. Access control is integrated into the actual door lock. No bulky or ugly add-ons are needed.
• No cabling needed to the lock. Existing doors can be activated by replacing the existing lock with an electronic lock.
• Door locks are battery powered, typically lasting 30 000 operations. The door locks will operate during a power failure and are non-dependent on individual battery backups or UPS power.
• Open members can use one tag for multiple sites.
• Open team members can monitor user access and door status from anywhere, even on their mobile devices.
Accessing Sandton
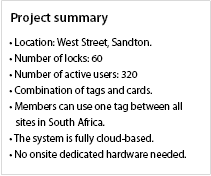
Open Sandton, which has about 60 doors to manage, chose the new XS4 escutcheon for their doors. The BLE (low-power Bluetooth) version was specified to future-proof Open for when the BLE functionality is available on SALTO KS. Each meeting room door has its own SALTO KS XS4 Escutcheon and intelligent mortice lock. The mortise lock is able to send an alert when a door had been left open, has an inbuilt panic function and an anti-pick latch.
PoE SALTO KS IQs (hubs) were deployed. These IQs are powered by PoE switches strategically placed on each floor. PoE IQs saved money for Open because they did not have to provide a power point to each IQ.
The IQs used at Open in Sandton were connected to the cloud via Ethernet. However, for future projects, an IQ with an integrated GSM SIM card will be used. The SIM connects to available cellular networks in the absence of an Internet connection. This is a benefit because if the Internet goes down on-site, the SALTO KS system will still be online.
The commissioning and installation was handled by SALTO partner, Concept Store. To make sure there was minimal disruption to the location, progress was measured door by door. Once a door was online, it was tested and signed off by the client. Because no local servers are required it is quite easy to do a sign-off per door instead of completing the entire site and only then do sign-off (once the server is up and running), which is the norm for access control installations in South Africa.
For more information contact SALTO Systems, +27 11 543 8489, info.za@saltosystems.com, www.saltosystems.com

© Technews Publishing (Pty) Ltd. | All Rights Reserved.