
It is common knowledge that the typical archaic visitor book just does not fit the bill as far as reliable visitor and contractor data gathering is concerned. Exid has locally developed and manufactured a solution that obviates the inaccuracies inherent to visitor books.
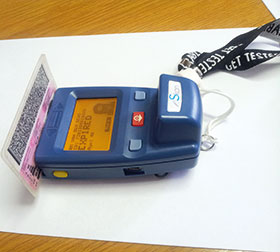
The eSkan barcode scanner is a robust and cost-effective alternative that allows security officers to quickly and easily validate the owner of the driver’s licence card and link them to the vehicle in which they have entered business parks and residential estates. Not only does this provide enhanced security of premises, but furthermore the superior reporting features allow the end user to determine trends in terms of traffic flow to specific areas as well as identify busy time periods, thereby allowing measures to be implemented that decrease bottlenecks.
Exid’s Shaun van Tonder says that the company has worked closely with Access Track, a company that specialises in capturing and managing visitor and contractor data, to develop a customised solution that collects accurate information directly from barcoded driver’s licence cards and vehicle registration discs.
The customised software developed by Exid is used in Access Track’s workflow solution which allows users to set up steps that the security guards need to follow when using the eSkan reader.
Once data is captured by the reader, cloud-based servers at Access Track are used to interrogate a number of interfaces to check criminal and community policing databases. This allows Access Track to quickly notify security providers of potential suspect vehicles while providing visibility of such sightings to law enforcement agencies. Van Tonder points out that since implementation of the system, reaction by security providers based on such sightings has resulted in the successful arrest of suspects.
Deployed at a number of business and residential estates, this access control solution is able to gather information on people and vehicles entering and exiting premises in real time.
Van Tonder explains that the eSkan may be used to automatically check that the vehicle used by a specific driver when entering the premises is the same vehicle in which the driver exits the property. By linking the vehicle to the driver at the outset, an alarm will automatically be activated should a driver try to exit the property in an unlinked vehicle. While different protocols are used on different sites, in general the guard is then prompted to disallow the exit of the driver and further action can then be taken, thereby dissuading criminality.
eSkan lets end users pinpoint exactly where on the premises a visitor is going and allows the setting up of a log specifically for contractor management. This forces all contractors to provide a valid identification for entry into the premises. The system also allows end users to blacklist people and vehicles, further enhancing the scope of the integrated criminal databases.
Applications where eSkan is proving popular include:
• Traffic fine management at car and trailer rental operations;
• Asset control;
• Logistics companies, where one can scan drivers on exit and re-entry and provide information on the times the driver left the facilities and then returned; and
• OHS, whereby one can determine in real time exactly how many visitors and contractors are on site, thus allowing one to quickly see if anybody is missing at a muster point, should an emergency occur.
Because the eSkan hardware is designed and manufactured locally, it is able to cope with the demanding conditions found in South Africa. Furthermore, a large technical support facility, extended warranties and the availability of parts and consumables, means that customers receive a fast turnaround on any technical queries and issues they may have.
“Aftermarket support is one of our big differentiators, coupled with the reliability, longevity and user friendliness of the eSkan unit. Installation is expedited with ease by the end user and licence fees are included in the purchase price, so no further costs are incurred. A rental option is available on request for those end users preferring not to purchase outright. While we have developed a number of standard backend solutions, we are also able to customise solutions that fit the end user’s specific requirements,” says Van Tonder.
For more information, contact Exid, +27 (0)12 548 0940, shaun@exid.co.za, www.exid.co.za

© Technews Publishing (Pty) Ltd. | All Rights Reserved.