
During 2014, the FBI investigated 1402 complaints of ransomware attacks (a virus that holds systems hostage until victims pay for a key to regain access) costing those targeted more than $23 Million. In 2015 FBI agents investigated 2453 complaints costing targets over $24 Million.
A recent cybersecurity article highlights that over 79% of South African internet users who have lost money at the hands of cyber criminals have only got some, or none, of their stolen funds back.
‘Cybersecurity’ refers to preventative methods used to protect information from being stolen, compromised or attacked. It requires an understanding of potential information threats, such as viruses and other malicious code. Cybersecurity strategies include identity management, risk management and incident management.
In South Africa a National Cyber Security Policy was finally approved by cabinet in March 2012. This defined a cybercrime as ‘an illegal act, the commission of which involves the use of information and communications technologies’. An updated definition was approved through the Electronic Communications and Transactions Amendment Bill of 2012 in October of that year. ‘Cyber-crime’ means ‘any criminal or other offence that is facilitated by or involves the use of electronic communications or information systems, including any device or the Internet or any one or more of them.’
According to Eyewitness News, cybercrimes cost the SA Economy R35 billion in 2015.
A cyber protection programme
Tyco Security Products launched its Cyber Protection Programme in 2016. This was after years of providing critical solutions for the US government and other large multinational customers, holding several industry firsts, including FISMA-ready access control and video solutions (Federal Information Security Management Act).
The six-part programme is designed to assist distributors and integrators with a better understanding of cybersecurity and the steps taken to combat current risks both from a hardware and software point of view.
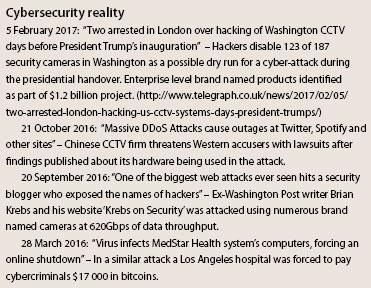
The days of worrying only about admitting/denying access and recording video are long behind us. There is now the concern about cybersecurity and cyber attacks as there is about threats against physical properties because the two are inextricably linked. The need for security manufacturers, distributors and integrators to be cyber-savvy is more important than ever before. However, why is it that some manufacturers/distributors seem to believe that the problem lies with the integrator/installer and ignore the realities that we have mentioned above; what questions are really being asked in this area?
The details of the Tyco Cyber Protection Programme are listed in the November 2016 edition of Hi-Tech Security Solutions magazine and are available at <a href=http://securitysa.com/*tyco1 target=”_blank”> securitysa.com/*tyco1</a>. Products include Illustra cameras, exacqVision, American Dynamics including VideoEdge and Victor, Kantech, CEM and Software House.
A camera-specific view
Adding IP cameras to a network requires their own security application as per any network device. A key element of the Tyco Security Products Cyber Protection Programme is ‘inclusive protection’ – ensuring that every device has been designed with the features and capabilities it needs to be allowed on the network.
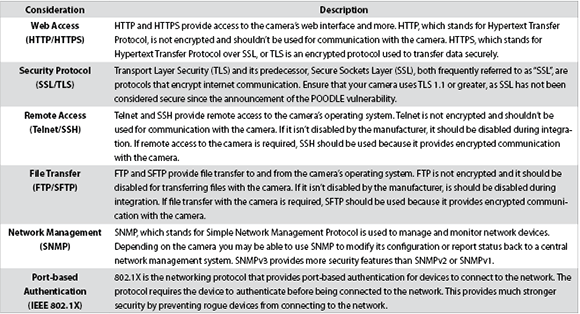
When evaluating any new video surveillance camera, we suggest that you not only consider the features you need, but also the cybersecurity considerations because most IP cameras use a web interface for setup and control of the camera, these are listed for simplicity as:
• Protocols.
• Logging and backup.
• Access and session security.
1. Communication Protection – refer to table 1 – Protocols
Communication is an obviously critical capability for surveillance cameras. You need to ensure that the camera has the necessary and appropriate protocols to meet your networks’ security requirements.
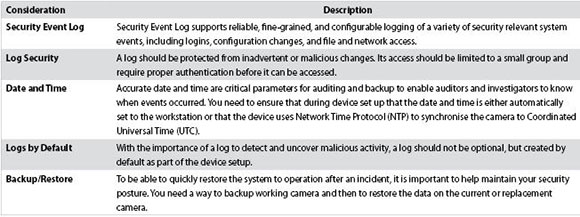
2. Logging and backup – refer to table 2
Log monitoring is a detective control that can be used to identify when vulnerabilities have been exploited. It records details of activity on the camera and can be used to detect incidents. Backup is a corrective control that is used to ensure that data can be restored if it is lost or corrupted. Used together, these controls help you to detect and recover from a vulnerability that has been exploited.
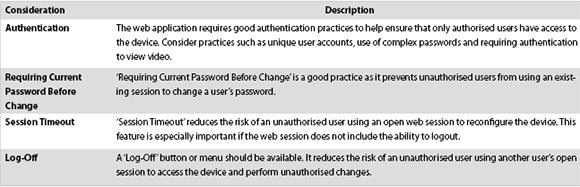
3. Access and session security – refer to table 3
It is important that the camera uses good, secure web application practices to reduce the risk of being a source of device vulnerability.
Conclusion
Vision Catcher is a Tyco Security Products specialist providing Illustra cameras, exacqVision and Kantech access control security solutions. We provide technical support and a range of services applicable to cybersecurity within our field of expertise. Please contact Niall for further information at +27 (0)11 463 9797, info@visioncatcher.co.za, www.visioncatcher.co.za
For further information on Tyco cybersecurity go to https://www.tycosecurityproducts.com/cyberprotection/cyberprotection.aspx
| Email: | julian.seiderer@jci.com |
| www: | www.johnsoncontrols.com/security |
| Articles: | More information and articles about Johnson Controls - (Tyco Security Products) |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.