
In the current economic climate, there is clearly a need to strictly control costs and minimise exposure to risk. To achieve these two pressing objectives, many local organisations are leveraging the capabilities of biometric-based solutions to prevent the repetitive losses that are a direct consequence of unauthorised access and associated activity.
Mark Eardley of SuperVision Biometric Systems says the theory and practice of secure access management is evolving and is being extended to more corporate activities. “Accurate identification of people has become a cornerstone of todays most cost-effective and competent security systems. There is a growing realisation that rigorous identity control is a requirement that extends throughout the workplace, from managing entry to buildings and monitoring attendance, all the way through to controlling who can do what within IT systems.
“Increasingly, identity is being used as a business tool to reduce risk. An obvious example of this is the ways in which fingerprint technology has become a common feature within systems that manage hours worked and payroll – referred to as Time and Attendance (T&A) systems. Such systems are heavily reliant on their ability to identify the people whose attendance they manage.
“Traditionally, these systems have been highly vulnerable to identity-based abuse – typically through people sharing their access cards or PINs and buddy-clocking for one another.”
End attendance fraud, cut management costs
Mark Stoop, business unit manager within the Innovation Group at Business Connexion, says, “For many organisations, payroll is the largest operating cost and the hardest to control. A lack of reliability in clocking systems can impose a costly burden on payroll management in terms of reconciling hours worked and resolving remuneration disputes.

“Payment for time not worked is alarmingly common within systems where identification of employees is based on access cards, PINs, tokens and punch-cards, all of which are so easy to share – let alone be lost, forgotten or stolen.
“In complete contrast, fingerprint biometrics produce consistently fast and accurate identification. They deliver levels of T&A convenience and security that simply cannot be achieved by the traditional methods.”
Marius Coetzee, MD of Ideco Biometric Security Solutions, says that over the past 10 years there has been exceptional local growth in the use of the technology within workplace attendance systems. “We work closely with our certified partners to ensure that our products can provide highly accurate identification within their workforce management systems. Our commitment to this type of integration work means that all the leading systems can now operate on the foundation of fingerprint-based identification.”

Buddy, punch my clock
Whether it happens occasionally as a favour or regularly through bribes and intimidation, buddy clocking is the most widespread form of payroll fraud, according to Eardley.
Figures from Nucleus Research and the American Payroll Association suggest that buddy clocking in the US represents 2,2% of gross payroll and can be as high as 5%.
In South Africa, T&A solutions that incorporate fingerprint biometrics routinely eliminate much higher rates of buddy clocking than the percentages experienced in the States. Locally, leading providers of such solutions agree that fraudulent clocking typically amounts to between 8% to 12% of gross payroll.
Eardley says, “Buddy clocking is a major contributor to this figure, but attendance fraud may also include so-called ghost workers. Typically, this occurs when employees create multiple false identities for themselves and clock each of the ghosts.
“However it occurs, it is important to understand that this type of identity-based fraud damages the bottom line in two direct ways – delivering a double-whammy of losses. Firstly, payment is made for time not worked. Secondly, productivity is lost throughout all the unworked hours.
“With an attendance solution based on fingerprint identification, employees clock by scanning a finger when they arrive and leave the workplace. Nobody can clock for them, they cannot clock for anyone else and all the ghosts resign. End of problem. It is a clear and easily-understood illustration of how identity control delivers solid financial benefits.”
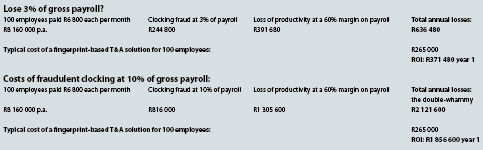
See table below.
Extending benefits to health and safety
The business case for fingerprint identification in attendance systems is a clear example of the technology’s proven ability to cut losses by accurately managing identity within business processes. Coetzee stresses that a critical issue in such systems is the accuracy of the identity data. “If that accuracy is compromised, for example, by people sharing their access cards, then the entire solution is compromised and cannot be considered reliable. It is the old data story of garbage in, garbage out.
“Nowadays, it is commonplace for fingerprint-based solutions to manage both access control and attendance on the same platform. This is significant because it shows how identity data can be used for multiple purposes – in this case to control physical access, to record attendance and to produce data for the payroll system.”
Stoop says that in partnership with Ideco the company has been implementing fingerprint-based physical security solutions in southern Africa for the past seven years. “For many years we have recognised the opportunities that are created by such accurate identity data in terms of improving efficiencies within secure business solutions. For example, in addition to managing access, attendance and payroll via fingerprint technology, we can also use the data to manage policies that govern the implementation of occupational Health & Safety regulations.
“Once again, identity has a major influence on ensuring compliance. In the workplace, we often need to know who is authorised and appropriately certified to perform specific tasks in certain areas.
“By using fingerprint-based identification we can export accurate identity data from the access system to the management systems responsible for ensuring that statutory health checks and occupational certifications are up to date. If they are not, we can create alert-messages within the access system and even escalate these to deny access to the people concerned.”
From calorie-intake to big machines
Tommy Laubscher, GM, customer support in the technical division of Protea Coin Group, has worked in advanced mining security for almost 20 years. He says, “One of the most significant advances in recent years has been the inclusion of fingerprint biometrics within secure systems. We are now leveraging the accuracy of identity data to deliver business benefits that go way beyond simply managing who is allowed through the main gates.”

To illustrate his point that biometric identity control systems are not solely concerned with conventional security, Laubscher gives the example of how such systems can monitor an environment such as a canteen. “We want to restrict access to the canteens and to ensure that the meals supplied are only served to duly authorised people on the mine. However, at the same time, we can accurately monitor calorie-intake from a health management perspective.
“These are not conventional security issues but they are very much based on the ability of biometrics to deliver highly accurate identification.”
Coetzee says, “We regard our integration services as an absolutely essential component of the technology we supply.”
This integration has allowed Protea Coin to confidently extend the advantages of fingerprint-based identification into new areas such as controlling the operation of the enormous mining trucks that are capable of carrying immense payloads of rock and earth.
“Traditionally, competency to operate big machines like these was simply based on trust. There would be various controls in place regarding how the conventional sets of keys were issued and stored securely,” says Laubscher. “But the underlying problem is that there are no guarantees that the correctly licensed and authorised driver started the vehicle and began driving it around the mine.”
Protea Coin developed an in-cab, driver identification solution that combines a Mifare card-reader and a fingerprint scanner in a single unit. Authorised operators’ fingerprints are stored in an algorithmic format on the Mifare card together with their driver’s licence code. This code is also programmed into the fingerprint scanner and corresponds to the type of vehicle being operated. The combined card and fingerprint reader is connected via a relay to the starting mechanism of the vehicle.
Laubscher says, “When the driver enters the cab, he places his Mifare card on our SACO Genius reader which extracts the licence and fingerprint data. He then scans his fingerprint on the integrated Morpho scanner which confirms his biometric identity. Once verified, he will be able to start the vehicle. The entire process of accurate identification only takes about three seconds.”
Opening minds to the realities of biometrics
Coetzee sees biometric technology as being at a point where its application is not limited to conventional security solutions. “It is not a technical issue about the competency of biometrics, it is about innovative applications and innovative thinking regarding how biometric identity can be used as a business tool.”
Stoop says that although Business Connexion has first-hand experience of the financial benefits his clients derive from fingerprint identification within physical security and workplace attendance, he recognises that organisations are increasingly exposed to security threats within their IT systems. “Corporate IT still relies on passwords, PINs and cards to control who can access their systems and operate within them. This creates the same obvious and elementary risks that we are countering with biometrics in physical security.”
He believes that the next major advance in biometric applications will be their integration into access and activity control within IT systems. “The motivation to introduce biometric controls into IT is really no different to what we have seen in physical security. The common goal is to prevent unauthorised access and the losses it causes. It strikes me that this is a particularly pressing need in IT given the level of losses being caused by corporate cybercrime.”
Once again, integration is critical to such an advance and Stoop and his team have worked extensively with Ideco to facilitate this. “We are now at the point where we can replace IT access cards, PINs and passwords with fingerprints. Not only can we control initial sign-on, we can govern access to applications, documents and Web forms. Through fingerprint-based authentication of the user, we can also authorise changes to data and control transactions. At the same time, we record all this activity and link it to the biometric identity of the user. This means that we build accurate audit trails that definitively show who did what within an IT system.”
| Tel: | +27 12 749 2300 |
| Email: | contact@ideco.co.za |
| www: | www.ideco.co.za |
| Articles: | More information and articles about Ideco Biometrics |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.