
Econz Wireless announced that photo and signature capture have been added to the new release of Eservice GPS.
Photo capture allows field staff to capture numerous job photos (up to 99 per job) while working on various jobs throughout the day. Field staff will also have the ability to label/add descriptions to these images as they are captured, allowing management staff to know what the images are and how they apply to the job at hand and adding a further management tool that not only tracks staff and jobs completed, but any situation at the customer site.
“We have also already seen customers use this feature in many ways unique to their business; images of staff onsite at start time, pre-work images, issues occurred on a job, samples on shelf, fool proof gauge readings, and other uses for the customer’s needs,” says Harry Lane, VP global channel sales, Econz Wireless.
Signature capture provides management with confirmation the individual was onsite, work has been completed, materials received, or approval of services provided. This new feature to Eservice GPS will allow the field worker to capture this much needed signature quickly and efficiently within a single application and even allow them to label the signature per job.
In addition to these new items being added, Eservice GPS continues to offer customers all of the following features:
• Automatic GPS & timestamps allow you to monitor and measure job acceptance time, travel time, working time, downtime and administrative time per job.
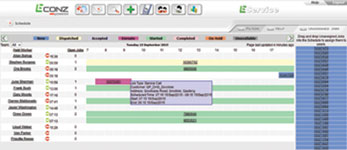
• Unlimited admin – web-based backend portal with overview, schedule, reports and other screens allows management access from any mobile device or computer that can navigate to the solutions login page.
• Access to real-time job dispatch, time stamps, job details and location data as it happens instead of waiting for information to trickle back in from the field staff.
• Various required job status updates from field staff mobile application for accurate details with up to 29 unique reports of the data collected which can all be exported to Excel/CSV format.
• The field worker has the ability to add optional/required notes, parts used, services provided and many more important job details.
• Collection of GPS breadcrumb trail mark every 60 seconds with time, date and speed, enabling management to check the status of their employees in virtual real time.
• Job times and details are stored for 6 months on customers web-based account portal.
• Integration options though certified partner into over 100 accounting and payroll systems – these systems include VIP, Pastel, PayDay, SAGE, etc.
• 100% native handset based application with store and forward technology.
For more information contact Econz Wireless, +27 (0)10 500 9637, sales@econz.co.za, www.econz.co.za

© Technews Publishing (Pty) Ltd. | All Rights Reserved.