
NEC XON has shared that its NeoFace Watch facial recognition system was successfully used by the Zimbabwe Republic Police (ZRP) to identify and apprehend a Chinese syndicate attempting to enter the country using fraudulent travel documents.
The operation began when the ZRP received intelligence regarding Chinese nationals attempting to enter Zimbabwe using counterfeit travel documents. Leveraging NEC's NeoFace Watch system, ZRP's facial recognition team identified Lin Xinwei from a Qatar Airways manifesto. The Chinese national has been under surveillance since July 2023, when she attempted to board a flight to Qatar using a fake Japanese passport. Despite her attempts to evade detection, NeoFace Watch enabled law enforcement to verify her identity, and identify her documents as fraudulent.
Further collaboration between the ZRP, Qatar Airways, and the United Kingdom and Northern Ireland passport office authorities revealed that Lin Xinwei and four accomplices possessed fake Chinese passports and United Kingdom residence permits. Meticulous analysis based on intelligence provided by NeoFace Watch revealed sufficient evidence of criminal activities to warrant their arrest and charges under Zimbabwe’s Immigration Act. The successful apprehension of the syndicate highlights the importance of international collaboration in addressing transnational crime.
An NEC XON spokesperson noted, "The case exemplifies the groundbreaking capabilities of facial recognition technology in combating transnational crime. NeoFace Watch empowers law enforcement agencies to identify and apprehend suspects swiftly and accurately by seamlessly integrating with existing government systems and databases."
Statistics on the prevalence of fake passports globally underscore the significance of initiatives like NeoFace Watch in safeguarding national security. Passports comprise nearly 45% of all counterfeit documents – an increase of 6% on the 2021 figure. The potential risks posed by illegal entry, terrorism, human trafficking, and financial crimes necessitate proactive measures to combat such threats.
"The collaboration between NEC XON and the Zimbabwe Republic Police highlights the transformative impact of advanced facial recognition technology in law enforcement efforts. The successful apprehension of the syndicate underscores the effectiveness of the NeoFace Watch system in enhancing security and protecting national borders."
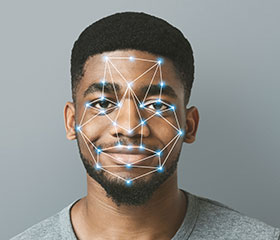
Real-time recognition
Facial Recognition systems can seamlessly interface with various government systems, including Immigration Visa applications, Civilian and Criminal ABIS, and Custom Management systems. NeoFace Watch gives law enforcement officials real-time access to CCTV footage at international airports and border posts, enabling swift identification of known perpetrators as passengers disembark from aeroplanes and proceed to immigration control areas.
At immigration counters, webcam and passport scanners facilitate rapid verification, matching the individual's passport photo with a live image within seconds. The live picture undergoes verification against multiple databases, including the immigration visa application database, ensuring the authenticity of both passport and visa application. Powered by NEC's unique algorithm, searches against a 12-million-person database take less than three seconds, with 99.8% accuracy. This solution offers unparalleled speed and precision in verifying individuals' identities, compared to traditional visual identification methods.
| Tel: | +27 11 237 4500 |
| Email: | info@nec.xon.co.za |
| www: | www.nec.africa |
| Articles: | More information and articles about NEC XON |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.