
Sasol is a global chemicals and energy company launched in South Africa over 70 years ago, and is currently listed on the Johannesburg Stock Exchange in South Africa and the New York Stock Exchange in the United States. It employs over 30 000 people and operates in 27 countries.
To assist in running and managing this enormous enterprise with many business units, Sasol makes use of eight SAP systems. The company updated its SAP payment processes making use of bioLock from realtime. A software solution, bioLock secures access to SAP via biometric authentication. However, the system does more than simply control access, it can be configured to protect fields and functions in the SAP system, only allowing certain people to access certain functions.
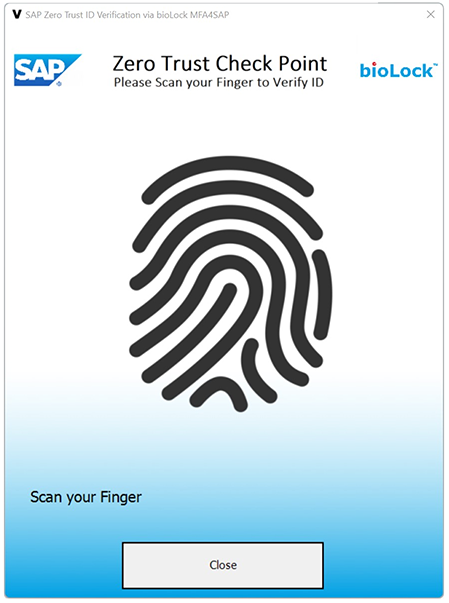
The latest bioLock MFA4SAP fraud prevention, compliance and accountability solution protects any function inside SAP with multiple authentication factors (MFA), including biometrics. Thomas Neudenberger, COO for realtime North America, says, “With zero trust, no actor can be trusted until they’re verified; bioLock allows you to set unlimited re-authentication checkpoints and use MFA technology, including biometrics, to ensure only specifically invited users get access to sensitive functions or data inside SAP.”
Sasol’s Enterprise Risk Management Framework
The Sasol Enterprise Risk Management (ERM) Framework sets the foundation for the businesses to effectively manage their risks in a standardised and systematic manner to prevent fraud. The goal of Sasol’s adoption of bioLock was to mitigate the risks associated with bank payment approvals and to enforce mandatory dual-approval rules built into the payment process. This necessitated the implementation of biometric authentication for the SAP Digital Signature approval process which, among other benefits, prevents people from circumventing GRC (governance, risk and compliance) roles by using a co-worker’s password, as well as preventing corruption and collusion.
“SAP GRC Software does a great job of defining bank payment amounts that authorised approvers must confirm, and now the GRC’s capabilities stop when the approver uses somebody else's password to approve the payment via SAP Digital Signature,” explains Lungile Mginqi, group CIO at Sasol and a board member of the Africa SAP User Group. “Adding bioLock as the second biometric factor gives Sasol the peace of mind to guarantee that only the intended SAP user, beyond any reasonable doubt, can confirm payment.”
The bioLock MFA process kicks in when an authorised user, having logged into the system initially with their username and password, wants to release a payment. The user is then required to confirm the SAP password sign-off with their fingerprint (the second biometric factor), to make sure the person is who they claim to be. Using biometrics makes the authorisation process very fast and convenient, and more secure, as opposed to the traditional way of having to re-enter their username and password. To change the rules of responsibility in the GRC process, two people are required to authenticate the change via this process – the ‘four-eyes’ principle.
The system monitors all activity and can alert management instantly if any anomalies in the process are discovered. In addition, all activities are logged to hold the appropriate people responsible.
The bioLock software was implemented by authorised realtime partner Linx/AS Africa. For more information contact Werner Simpson, Linx/AS Africa,
| Tel: | +27 11 543 5800 |
| Email: | malckey@technews.co.za |
| www: | www.technews.co.za |
| Articles: | More information and articles about Technews Publishing |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.