
The tools and processes used in modern system design and development are exponentially increasing the number of assets organisations must identify, manage and secure. This is an opportunity to rethink the formula for security testing so that it addresses the real risk and impact of an attack, while being regulation-compliant. In this article, we’ll break down the process involved, explaining how to harden your operations and improve resilience by aligning security spend with real risk.
Risk-based prioritisation is an alternative means to decide if and how to test assets. The approach contemplates which assets require scrutiny, based on specific, real-world threats, especially those that would threaten business continuity. As a result, security testing becomes more goal-oriented and shows tangible results.
Risk-based prioritisation in practice
Organisations that are conscious of shortcomings in their system and vulnerability management are likely to see the most tangible benefits. The three goals of the exercise are:
1. Gather context on the assets in your estate by answering specific questions about them, via stakeholder workshops or through hands-on exploration.
2. Apply a risk rating to each asset to help you prioritise them for testing.
3. Identify the best approach for testing based on that prioritisation.
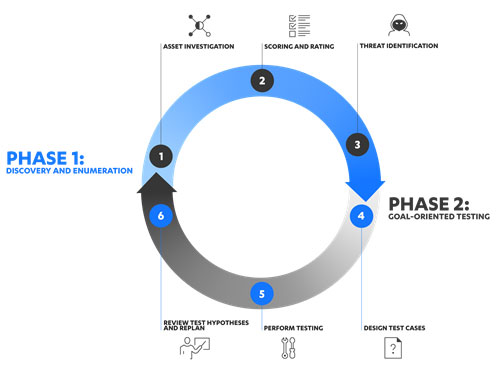
Phase 1: Discovery and enumeration
Asset investigation
The exercise begins by identifying a number of critically important assets in your estate, as well as the employees who act as their stakeholders. A critically important asset can be understood as any asset that, if impacted in a cyber-attack, would significantly disrupt business continuity. There are two routes to assess each asset or assets — via a workshop or hands-on exploration.
Route 1: Workshop. The aim of a workshop is to understand each asset, the context it operates in and how an attacker may target it. This is done through discussion and iteration. Observations are documented so they can be used to assign an importance rating and a plan for testing each asset.
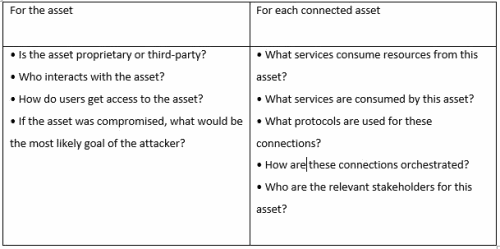
Route 2: Hands-on exploration. A hands-on approach requires available resources in your technical team to experiment with apps or infrastructure, scope the same information covered in the workshops and ask additional questions if necessary. It’s an effective solution for teams unable to collaborate in person, i.e., if they are operating remotely, or where asset stakeholders are unavailable or uncooperative.
Scoring and rating
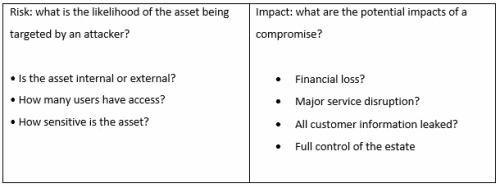
Once all assets have been documented, they are each scored and rated according to the risk and potential impact they pose.
The scoring system is defined by the risk and impact factors specific to your organisation and should include 'effect if compromised' and 'likelihood of being targeted'.
More metrics can be added as per the needs and interests of your organisation. Banks, for example, would likely emphasise loss of financial or client data. For telecommunications providers, it may be service disruption and control of their operational technology (OT) environment. Essentially, the risk matrix needs to synchronise with your internal risk register.
This risk assignment is most effective if it can respond to the business’s needs dynamically. Even if stakeholders’ opinions of an asset’s importance contradict the levels proposed by the risk matrix, these should still be fed into the process.
Based on the results from the scoring exercise, an importance rating from critical to low can be assigned to each asset. With the assets listed in order of risk, security tests may now be tactically scoped. The list can be mapped to strategic security and business goals for the buy-in of other stakeholders, as well as to show the increasing maturity/resilience of assets over time.
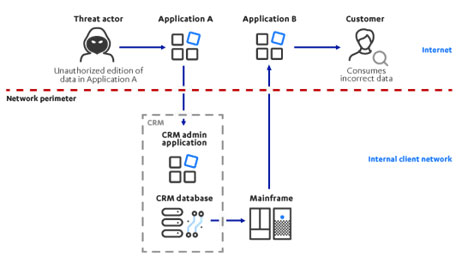
Threat identification
The information gathered from workshops/hands-on exploration and rating exercises can be used to create models of your organisation’s environment. These provide the security team with a visual reference showing how assets are connected, i.e., how the risk of one asset affects the others around it.
Phase 2: Goal-oriented testing
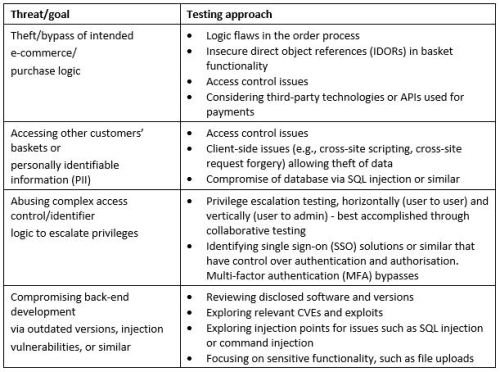
Discovery and enumeration complete, you can now start to design tests around how your assets may be targeted by threat actors harbouring specific malicious goals.
Step 1 of the exercise is to build a test case for each asset, starting with the most critical. Each case forms the basis of a test to uncover potential threats/goals (why an attacker would target an asset), such as ‘We can bypass MFA to steal PII from customers’. The ultimate objective is to define the most contextually relevant way to test assets against each goal.
Review test hypotheses and replan
A test case proven incorrect is evidence of controls working effectively, which demonstrates successful work performed by development and security teams. Contrasting the often negative, defect-focused approach of standard pen-testing, it recognises where things are working, so the same measures may be applied elsewhere. It also quantifies prevention budget spent wisely.
These incorrect test cases are one output of risk-prioritised testing and can be used as the starting point for other testing. What this testing is and where it’s focused will be unique to your organisation. Fundamentally though, risk-prioritisation is the foundation needed to deliver a testing programme that is efficient and effective overall by instilling the risk/threat mindset.
Long-term gains
A risk-prioritised approach to security testing enables organisations to focus on the assets most in need of attention. Over a longer period, it does even more to make your security testing work harder. These long-term gains include:
1. Focus objectively on the threats that matter most. Reviewed from an attacker’s perspective, high-risk assets are prioritised and subjected to more testing than assets that pose little risk. Testing can then focus on key attacker goals for each of those assets rather than just performing generic pen-testing and achieving generic results. Resources and time can be scoped for maximum investment.
2. Overcome the static nature of point-in-time testing. Delivered iteratively, prioritisation takes care of assets that would otherwise go untouched for months between engagements and be exposed to threats in that time. By exploring your assets iteratively, reviewing findings and investigating further, there’s a greater chance emerging vulnerabilities will be flagged and assets get tested before they can be exploited.
3. Put past testing to use. You can optimise your risk-prioritised testing over time by consuming information from previous security assessments and threat analysis exercises. This data may be used to tailor and adjust future tests so you don’t duplicate the effort, thus adding another layer of efficiency and improving resilience.
Summary
Risk-based prioritisation reveals your most critical assets and the top risks they face. This enables you to focus on prevention in these areas specifically. You will know which assets matter most, which threats are of greatest concern, and have evidence of your ability to prevent them. You can then start to consider the detection of attempts to utilise those key threats, increasing your overall confidence in those assets.
This works towards operational resilience – organisations can move away from traditional approaches that no longer suit the scale and complexity of their environments. Build a resilient approach to security testing and you’ve got solid foundations for making further intelligent, targeted investments elsewhere.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.