
The coronavirus has had a devastating effect on businesses and other organisations that rely on individuals working in a physical facility. For many, the ability to reopen and bring people back into their buildings has been a pressing need. As stay-at-home orders and business-closing orders begin to be lifted around the world, these organisations are investigating the best ways to safely bring people back to work.
One of the key factors that emerged in the drive to maintain the safety of the employee population during the pandemic, and possibly continuing in the future, is health monitoring. While a number of new apps have been introduced to encourage self-reporting, many employers have determined this still falls short of ensuring the health and safety of their employees. These organisations have begun to look for technology tools to screen personnel as they enter facilities.
At the same time, access control continues to be an important need for all facilities that need to ensure that only authorised individuals are able to pass through an entry point. With new threats to health and safety, touchless access control solutions have swiftly gained traction as they help to mitigate the spread of germs and viruses. Among these, facial recognition has become dominant for its high degree of accuracy.
In this landscape, thermal cameras have become a popular solution to provide a biometric access control solution using facial recognition, with the added ability to detect elevated temperatures.
Thermal cameras work by detecting heat radiating from the subject. When placed at an entry point, facial recognition devices with thermal cameras can rapidly scan entrants to control access, also identifying persons with elevated skin temperature. Alerting and notification capabilities communicate this vital information to human resources or other authorities who can then take appropriate actions to protect the rest of the employees on site.
Sensor technologies for thermal cameras
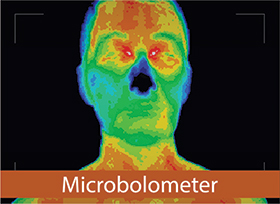
There are two types of sensor technologies that are currently being widely used in thermal imaging applications. These are microbolometers and thermopiles, and there are significant differences between the two, which affect their ability to deliver optimal temperature-taking performance.
Thermal cameras with both thermopile and microbolometer sensors measure temperature by detecting an object’s infrared energy. The more infrared energy that is being emitted, the higher the temperature will register.
But thermal cameras which use thermopile sensors produce low-resolution images with only one thousand or up to a few thousand pixels. These sensors have disadvantages: subjects must stand still, and screening time is fairly slow.
In contrast, a thermal camera with microbolometer sensors produces high-resolution images with more than 10 000 pixels. This enables microbolometer-type cameras to measure temperature more precisely than their thermopile counterparts. Microbolometer sensors also capture information much more quickly and accurately from a range of positions, so subjects do not need to stand still to be measured. This enables swift measurement of people as they walk past the camera.

Ten tips for optimising thermal camera performance
1. Place the camera in a protected area. There should be as little wind or other air movement as possible, no direct sunlight and no other significant source of heat nearby.
2. Avoid areas where the camera’s imager could catch reflections from windows, metallic devices or other reflective surfaces.
3. If the camera will be used in an outdoor environment, protect it with a shielding device such as a screen or tent. Use the device in the recommended ambient temperature for best performance.
4. Maintain moderate distances between the individuals moving past the camera.
5. Screen individuals one at a time.
6. Ensure that no one being screened has just participated in any activity that elevates temperature, such as exercise or bathing. Give the subject 30 minutes of rest after such activity for accurate measurement.
7. Wipe any sweat or moisture off the skin area that’s being measured to avoid evaporation from lowering their temperature.
8. Require each individual being screened to remove any obstructions to their forehead (such as hair bangs or a hat) for highest accuracy.
9. Ensure each individual faces the camera with their entire face in the image area.
10. Provide a secondary screening with a medical device for anyone who demonstrates an elevated skin temperature.
| Tel: | +27 11 784 3952 |
| Email: | info@neametrics.com |
| www: | www.neametrics.com |
| Articles: | More information and articles about neaMetrics |
| Tel: | +27 11 784 3952 |
| Email: | enquiry@suprema.co.za |
| www: | www.suprema.co.za |
| Articles: | More information and articles about Suprema |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.