

Cable theft is one of the most common crimes in South Africa, costing service providers as well as consumers and business users millions in terms of lost productivity, unnecessary bills and extreme levels of stress.
When an underground cable is stolen, whether a telecommunications or electricity cable, everyone suffers. Stealing even a small section of electrical cable, for example, leaves businesses and homes in the dark for hours while the service provider needs to dig up pavements and/or roads, replace the cable and reconnect it.
To date there have been numerous products and solutions designed to combat cable theft, but their success has not always lived up to expectations. Bidvest Protea Coin has changed the game with a new solution that takes advantage of the latest technology to warn service providers, municipal councils and whoever needs to know, that a cable in a specific location is under threat, before any damage can be done.
Early Warning IoT Solution
Bidvest Protea Coin’s Early Warning IoT Solution has already been installed by a municipality in Gauteng and is proving successful at keeping electrical cables underground and functioning.
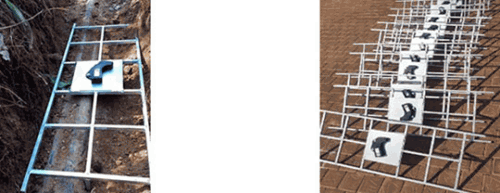
The solution is a low-cost, low-power IoT device that includes a three-axis accelerometer. The devices are buried on a platform about 300 mm above the cable being protected, and are connected wirelessly to the Sigfox network. Sigfox is a low-power IoT wireless network that covers over 90% of South Africa’s populated areas. IoT devices are able to send signals over the network in small data packets.
When the Early Warning IoT Solution detects digging or similar movement in its vicinity, it sends an alarm signal to Bidvest Protea Coin’s control room, providing the identity of the device and the location of the breach. The operators are then able to dispatch security response teams and prevent the theft. Because of the sensitivity of the device, the alarm is raised before criminals reach the cable and can cause any damage.
In the municipal installation Bidvest Protea Coin used as a pilot site, thefts have already been prevented by the early warning system. Since the thefts to date have occurred at night, the perpetrators were able to escape once they saw the security vehicles approaching. However, all they managed to accomplish was leaving a hole in the ground and the electricity supply was not affected.
As an ultra-low-power device, the batteries will keep the devices running for about five years. Furthermore, the solution not only allows an alert to be sent to a control room, but also to individual cellphones if required.
The devices are ruggedised to ensure they operate reliably in almost any environment, and they also use BLE (Bluetooth Low Energy) to communicate with other nearby devices. The intelligent software within the devices enables them to distinguish between threats such as digging and movement that may occur as a result of traffic or people.
Benefits of the Early Warning IoT Solution
• Improve service delivery.
• Early warning to reduce risk of theft.
• Reduce downtime.
• Reduce CAPEX and OPEX on maintaining infrastructure.
• Improve repair times.
The pilot project was connected to the Listener platform in Bidvest Protea Coin’s control room, but the company can integrate the solutions into any platform via APIs (application programming interfaces). To keep costs to the customer down, Bidvest Protea Coin sells the solutions as a service, integrated with its other security services which provide a full solution for a standard monthly fee.
| Tel: | +27 12 665 8000 |
| Email: | info@proteacoin.co.za |
| www: | www.proteacoin.co.za |
| Articles: | More information and articles about Bidvest Protea Coin |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.