
Built upon more than 15 years of experience enabling biometric solutions, the Fulcrum Biometrics Framework (FbF) products are a suite of tools that simplify the inclusion of biometrics into any new or existing mobile, desktop, or web-based application.
With FbF tools, you have everything you need to biometrically link a physical person to their records in your database or application. By choosing to work with the FbF tools instead of low-level SDKs, your time can be spent focused on perfecting your application or solution’s features, rather than becoming an expert in implementing biometrics.
The benefits of FbF include:
• Spend hours – not months – integrating biometrics into your systems or applications.
• Use any, or multiple, biometric modalities (iris, finger, face, vein, voice, etc. ) best suited to your security requirements and application’s needs.
• Scale to any size population – from a small office, to a large enterprise and all the way up to a national database.
• Save thousands of Rands in engineering costs and time spent focusing on non-core activities.
• Now you can meet your customers’ expectations within real-world deadlines and satisfy the concerns of auditors and regulators, by increasing the speed, accuracy and reliability of validating individual identities in your environment.
FbF bioServer
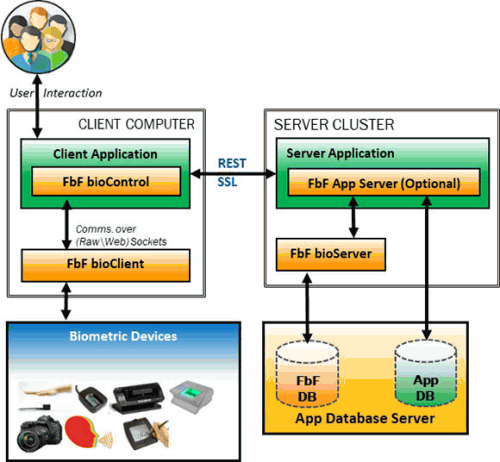
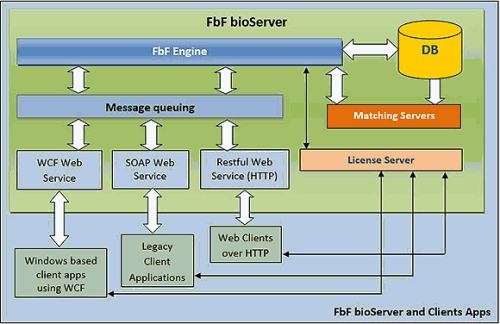
The FbF bioServer reduces the complexity and cost of implementing biometric identification in your project – expediting time to market with a reliable, robust and scalable solution.
The FbF multi-biometric technology ensures high reliability (accuracy) and high performance (speed) of biometric identification regardless of the size of the dataset. Even when matching against large, national scale datasets, the FbF bioServer can scale to meet demand. In small- and medium-sized projects, FbF also provides a highly cost-effective solution. The FbF bioServer excels at both ends of the spectrum; it can be scaled from tens of thousands of identifications per second to hundreds of millions of identifications per second through a combination of software and hardware acceleration in a form factor that supports single server and server cluster configurations.
Key features of the FbF bioServer include:
• Ability to segment out groups.
• No need to interfere or integrate with existing databases.
• Windows Embedded 7 Server.
• SQL Server database engine.
• Easily scales from thousands to millions of people.
• Standard web service interface.
• Advanced WCF service interface.
• FbF messaging architecture.
• Supports clustering.
Client-side device management and messaging
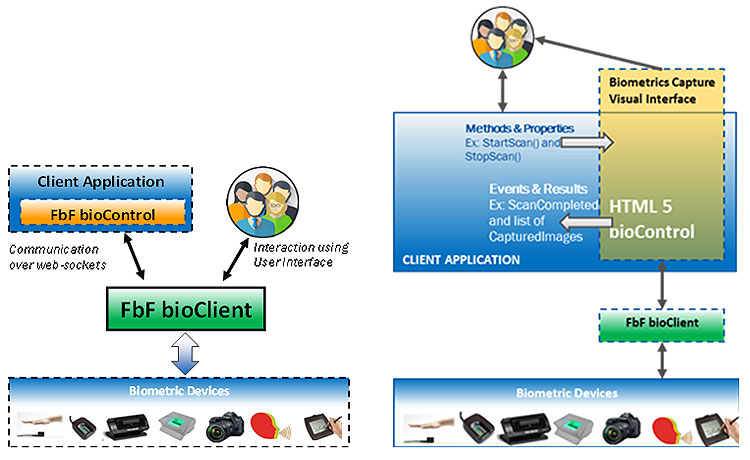
The FbF bioClient is a ready-to-deploy client-side application that overcomes the challenges involved with the integration of a biometric application with a variety of biometric sensors and the demand for web-based, distributed applications by providing an abstraction layer between biometric hardware and the business logic present in web applications. This is accomplished through the use of a proprietary messaging architecture that is securely communicated through a standard TCP/IP connection. FbF bioClient is optimised to use the web-based user interface for biometric systems.
Key features include:
• Runs in the background (always-on application).
• Automatic device detection.
• ClickOnce deployment.
• Allows for event driven biometrics.
• Publish/subscribe biometric model.
• FbF messaging architecture.
• Easiest way to integrate client-side biometric components.
• Eliminates messy hardware integrations.
FbF bioControls
A reusable control library specially designed and developed for handling biometric applications.
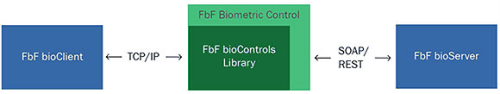
Integrating biometric enrolment, verification and identification capabilities in your new or existing application becomes a simple and painless exercise thanks to the FbF bioControls. The bioControls essentially link your application, the bioClient and the bioServer together. Available as a set of drag and drop components, you use the bioControls in your development tools. They are the only piece of FbF code ‘embedded’ into your software.
Whether developing a web-based application, a traditional software application or something in between, the bioControls come in several flavours to suit your requirements – .Net, Silverlight, HTML, or WPF. FbF bioControls eliminate the need for writing complicated code to communicate with the biometric capture hardware and the biometric matching engine. Key features include:
• Distributed as libraries/packages that can be dragged and dropped into the compatible projects.
• Dedicated version for different programming environments: .NET, HTML5, PHP, JAVA (Web) and WPF.
• Capable of two-way communication:
o With bioClient for biometric device related operations.
o With bioServer for enrolment and identification related operations.
• The programmer can perform complex biometric operation just by setting control properties and calling control methods. Examples are:
o Segment and Extract: Automatically capture a 4-finger scan, segment 4 individual fingers and extract template in one go.
o Identify and Enrol: Identify the provided template and enrol if not already found on the server.
• Provides properties and methods to perform biometric operation such as:
o Segmentation, template extraction and format conversion.
o Get results in multiple image format.
o In-built capability to display live stream, final image and layover graphics.
o Provides ability to save images and template that can be used by the application for its internal business logic.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.