

BAA adds functionality to British Airport Authority airport systems in response to changing legislation.
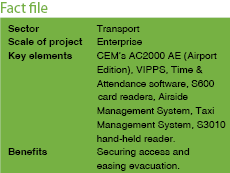
BAA is a leading airport company at the heart of the world’s transport network. Each year, the company serves 128 million passengers, and 67% of the UK total, at its seven UK airports: Heathrow, Gatwick, Stansted, Southampton, Glasgow, Edinburgh and Aberdeen. More international travellers use Heathrow than any other airport on the planet, making it the world’s busiest international airport.
BAA has used CEM’s AC2000 AE (Airport Edition) system to control access at its UK airports for over 15 years. Today, the seven airports combined have more than 3500 card readers installed and over 240 000 active cardholders with the systems handling more than 4,5 million card swipes per month.
For over 10 years, the three London airports – Heathrow, Gatwick and Stansted – have been networked, allowing their valid cardholders to go from one airport to another. This equates to a linked system with more than 3000 readers, handling 218 000 active cardholders, making it the largest airport system in the world. This link was successfully extended to include all seven BAA airports.
Simplified access control
From its initial installation, CEM has worked with BAA to develop the system in response to each airport’s needs and to offer more than simply an access control solution. Over the years, functionality has been added to each system in response to changing legislation in the aviation industry and as the airports grow. Today, the system provides an integrated business solution that is continuously designed to help BAA run its airports more efficiently.
From using VIPPS (visual imaging pass production system) to control the issue and invoicing of operational access control cards, to configuring readers to assist in the movement and segregation of passengers, CEM has provided BAA with a dedicated airport security management system.
The CEM readers allow doors to operate in a variety of modes as required in the airport environment. Other than simply providing individual staff access, specified readers are configured at each of the BAA airports to permit passengers to enter a controlled area and to allow airline staff to easily segregate arriving and departing passengers.
At Heathrow, the system sends broadcast data to the readers and monitor units. For instance, if a quiet evacuation of an area is required, the system is programmed to unlock a number of doors. This means in the event of an emergency threat, the area can be evacuated without having to trigger the fire alarm system to open doors.
At Stansted airport, the card system holds details of card usage at every control point. Card transaction data includes the card number, date and time used, directional status (in or out) and the transaction outcome. This transaction data, besides producing tracing information, is also passed on to an external payroll system or used with the CEM Time and Attendance module for calculation of working hours. The system can even trace cardholders as the cards are used. Once a cardholder is added to the trace list, the system displays a window showing the card reader at which the card is being used next.
More than physical access
At Glasgow, CEM S600 card readers are used to enable or disable check-in desks or baggage belts. Before a check-in desk can be used, the operator must swipe a card. If valid, power is provided to the desk and belt. The system opens the flight information system, which displays the active check-in locations for various flights. The data can also be used to invoice airlines for the use of shared check-in desks.
A major application at Gatwick is a loading bridge monitoring system. Sometimes referred to as an air jetty, it is designed to reduce maintenance costs and increase the control of a loading bridge. There had been concern that it was difficult to track the use and status of air bridges. To address this, the AC2000 AE system links a loading bridge to a CEM S600 card reader. Before the bridge can be used, a valid swipe must be made on the reader.
CEM also helps BAA control access of vehicles. The Airside Management System is in use at Heathrow to gather meaningful technical information about vehicles in use at the secure airside area, while Gatwick and Stansted use readers to control and manage access of vehicles and passengers to their carparks.
Additionally, CEM developed the Taxi Management System to ensure the fair allocation of taxis at Edinburgh airport. Authorised drivers swipe at a CEM reader to indicate their arrival, while booking software in the taxi office designates an assignment and sends notification to the driver and passenger via a screen at the taxi rank. This system successfully assists in managing passengers at busy periods.
Card cloning concerns
Card cloning refers to the copying of an access control card or fob in order to compromise electronic door security on an access control system. Sometimes referred to as ‘card spoofing’, a device is introduced to either duplicate a card or impersonate it.
Handheld card cloning machines are now readily available on the market. The card cloning machines can copy most RFID cards in use.
To prevent information from being stolen or compromised CEM recommends the following:
1. Use high-security smartcards with industry approved authentication and encryption, such as DESfire, PicoPass and iClass.
2. Use readers capable of two or three factor authentication.
a. Use card and PIN verification or 2 factor authentication.
b. Use card and biometric verification or 2 factor authentication.
c. Use card, PIN and biometric verification 3 factor authentication.
For more information contact Tyco Security Products, +27 (0)82 566 5274, [email protected], www.tycoacvs.com

© Technews Publishing (Pty) Ltd. | All Rights Reserved.