

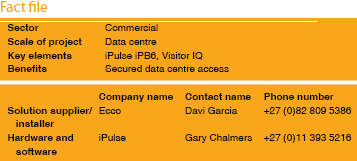
Ecco biometric solution takes the pain out of visitor access at mission- critical Teraco data centres.
Founded in 2007, Teraco is South Africa’s first provider of vendor neutral data centres, with a focus on building and operating its facilities in Johannesburg, Cape Town and Durban to global best practice. Teraco data centres give customers a technically superior, physically more secure and lower cost environment for their information systems. Strictly enforced access control and uncompromised security is guaranteed.
To maintain its strict security policy, Teraco has adopted the following system design principles:
* Comprehensive perimeter and building security, with ‘zones within zones’ for multiple levels of security.
* Pre-authorisation required for data centre access according to Teraco Access Policy.
* Two-tiered identification system: Biometrically via a fingerprint, visual identification against a photo on a named user list.
* Comprehensive audit logs on all entries.
* Additional bespoke access policies can be implemented for private cage customers.
Based on its reputation in the market, Teraco contracted iPulse platinum partner – Ecco – to handle its access requirements. Ecco deployed the iPulse iPB6 reader for access control at the entrance to the main building. Chosen for its intelligence and flexibility, the iPB6 can determine whether a person is allowed access at that specific date and time, or even how many times they are allowed to pass through a door.
A major advantage of the system is that there is no need for a controller to do the decision-making for it. The iPB6 was also chosen above its competitors because of the ease of installation and scalability. In addition, as a pure IP-based system, the iPB6 simplifies the expansion of an existing system.
“Ecco has made a strategic decision to use iPulse Systems products as its exclusive fingerprint technology for access control, based on the key factors of ease of use, unparalleled integration, interoperability with other systems, exceptional management software, cost effective pricing and, above all, reliability,” said Davi Garcia, CEO of Ecco.
Biometric identification at all the doors to each zone and rack leaves an unquestionable paper trail which allows Teraco to track the exact times that a visitor was at a specific location. In this way, video footage of that person’s every move can be recalled with ease and this fast identification negates delays in even the highest traffic areas.
Teraco recently installed the iPulse VisitorIQ software at its Isando facility to manage visitors to the premises.
“Generally speaking, security and convenience do not really get along that well. The tighter the security, the more time-consuming it becomes, the more fuss and hassle it leads to. Access points choke up as customers wait to have their identities confirmed. VisitorIQ has made managing our clients’ access to our facilities an absolute pleasure,” said Gys Geyser, operations manager at Teraco.
Visitor IQ is a web-based visitor registration and management application that allows visitors to pre-register before they even reach the building. After the administrator has granted proper authorisation, the visitor’s details are entered into the system. On arrival at the specified facility the visitor will self-enrol at the enrolment kiosk to confirm his personal details and, in the event of a first-time visit, capture his fingerprints and photograph. This process is completed in under 60 seconds and the visitor is allowed access through specific, pre-determined doors and/or issued with access tokens which are programmed to be either time-based or to allow a limited number of entries.
Once a visitor’s details have been added to the database, the next visit is even easier. Identification via the visitor’s ID number recalls their details, sends their personal data to the applicable readers and access to all required areas is granted within seconds. There is no need to re-register or to manually allocate the visitor’s details. This is advantageous to Teraco as it is simple, easy, efficient and extremely secure.
For more information contact iPulse, 0860 IPULSE (478573), [email protected], www.ipulse.co.za
| Tel: | 0860 478 573 |
| Email: | [email protected] |
| www: | www.ipulse.systems |
| Articles: | More information and articles about iPulse Systems |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.