
CCTV systems are only as good as the lightning and surge protection system.
Lightning is one of the most spectacular metereological phenomena and the most common severe weather event to affect people. According to international research there are roughly 2000 thunderstorms in progress around the world at any one time, producing 30 to 100 cloud to ground flashes every second, equating to five million flashes per day.
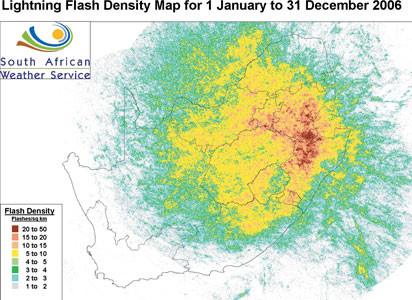
South Africa is a lightning prone country with one of the highest lightning ground flash densities in the world. Lightning related death statistics are nearly four times higher in South Africa than the global average. In a recent study published in Annales Geophysicae, it is shown that the Witwatersrand and the Drakensberg areas experience the highest level and intensity of lightning. This is further substantiated by the SA Weather Services who recently introduced a lightning surveillance system. In its overview for 2006 (see map) it clearly shows that although Gauteng, the Drakensberg area and Northern Natal are worse off, the rest of the country is not spared.
We cannot take the lightning problem lightly, particularly when it comes to the efficient operation of protection and surveillance systems. These systems are as reliable as the surge and lightning protection systems that protect them.
In recent years the method of lightning and surge protections has changed drastically, so much so that suppliers are more confident that their systems work effectively. The most important aspect is to approach protection from an holistic point of view. It is simply no good just fitting a protection device at the camera and somewhere along the line on the main supply.
Main sources of surges
We have to deal with two main sources of surges. The first and probably the most common sources are mains-borne surges. Switching of large industrial loads connected to the power supply grid causes these surges. As the loads are switched on, the voltage is 'pulled down' for a fraction of a second. The supply authorities automatically compensate for the additional load, which results in a short duration over-voltage before the supply stabilises once more. The result is a surge. Whilst these surges are for all intents and purposes relatively low level they can be of significant duration, and the energy component is therefore enough to cause damage to sensitive electronics.
When electronic equipment is regularly subjected to these low level-switching surges the equipment will exhibit signs of premature ageing as the components are regularly forced to work outside of specified parameters.
The methodology employed in protecting against these surges is to install surge protection on the main incoming power. Since the surges enter the installation through the power lines it is only necessary to install protection at this point to prevent damage from this source. This will however not protect against the major source of surges - lightning.
To fully understand how to protect against these potentially catastrophic transients it is essential to review how lightning surges enter into the system. There are four ways in which massive amounts of energy in a lightning strike enter into an electronic system:
Direct coupling - lightning strikes the power line.
Inductive coupling - EMF induces secondary currents into cabling.
Capacitive coupling - capacitive effects of steel roofs and cabling.
Galvanic coupling - potential difference effect.
For our discussion on the protection of CCTV systems I will dwell a little on galvanic coupling.
Galvanic coupling
The term galvanic coupling has an interesting history: in 1783, according to popular version of the story, Galvani dissected a frog at a table where he had been conducting experiments with static electricity, Galvani's assistant touched an exposed sciatic nerve of the frog with a metal scalpel, which had picked up a charge. At that moment, they saw sparks in an electricity machine and the dead frog's leg kick as if in life. The observation made Galvani the first investigator to appreciate the relationship between electricity and animation - or life. He is typically credited with the discovery of bioelectricity.
Galvani coined the term animal electricity to describe whatever it was that activated the muscles of his specimens. Along with contemporaries, he regarded their activation as being generated by an electrical fluid that is carried to the muscles by the nerves. The phenomenon was dubbed 'galvanism', after Galvani, on the suggestion of his peer and sometime intellectual adversary Alessandro Volta.
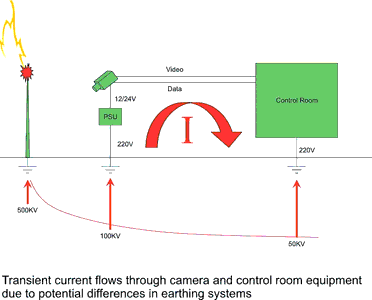
Consider what happens when lightning strikes the ground or an object that is connected to ground. If one could measure the potential in the ground at the instant that lightning strikes, the potential where the lightning enters the ground is in the order of several hundreds of thousands of volts. Further from the point of entry the potential will drop off until at some distance from the point of impact the potential drops to 0 V.
Consider the two points. They are like the terminals of a 500 kV battery (if there was such a battery). Connecting a conductor across the imaginary terminals that have a very much lower resistance than the ground path, the larger current will flow through the conductor. Using ohms law with two resistors in parallel, the resistor with the lowest ohm value will carry the larger proportion of the current.
It is this principle that causes so many deaths amongst people and livestock around the world every year. A golfer on the course near a lightning strike provides a lower resistance path between his two legs that are a little distance apart and is thus subjected to a high current flow through his body.
The further away we move from the point of strike, the lower the voltage. If we, however, earth equipment near the point of strike and again other equipment some distance away and the two earthed sites are connected through data lines, there will be a difference in potential that will be equalised through the lowest point of resistance, which will be through the equipment thus causing severe damage.
In modern electronics almost everything is networked in some way or other. All basic networks have one thing in common. They have two or more electronic circuits that are earthed through a power connection and then interconnected with copper cables.
Surge protection
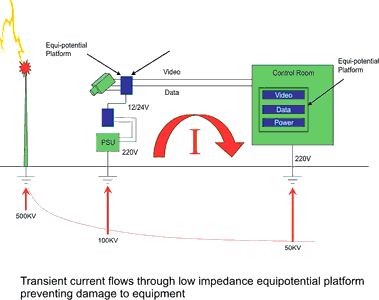
Introducing surge protection on the power inputs of the devices in a network it is immediately apparent that while they may remove some of the energy the low impedance path of the network remains unprotected.
Through extensive research we have developed a range of video protection patch panels which when fitted in a rack with one of the plug protected strips or combination strips provides complete system protection.
It is in all instances important that the power and video inputs are protected and the two protection devices are bonded together to an electrical earth.
Lightning and surge protection is today an exact science. We have the systems and the tools. It remains, however, important to take all factors of an installation into consideration and design the protection system to achieve maximum efficiency and reliability.
Warren Botten is the OEM sales manager at Clearline.
For more information contact Clearline, +27 (0)11 848 1100, [email protected], www.clearline.co.za

© Technews Publishing (Pty) Ltd. | All Rights Reserved.