

The ‘convergence trend’ taking place in the security industry brings with it a host of really interesting market developments.
Fuelled by a general awareness of information technology the market is driving product development with expectations in terms of information access and automated system management.
A typical example of this is integrated security systems where the demand is for singular point of information access and control and in particular, rules-based system control and trends analysis. Probably the most common requirement is that of integrated video surveillance, access control and alarm management.
This article looks at some of the special system features that can be achieved by integrating access control with video surveillance. While there are many alarm situations that can be detected and reported by both the video surveillance and access control systems, alarm management and the integration of alarm panels is a subject in its own right.
Consider an integrated system along the lines of that depicted in Figure 1 below. A digital video system, which may be either integrated (PC-based) digital video recorders or video-over-IP encoders and cameras, or even a composite blend of the two architectural types, is connected via LAN to an access control system server.
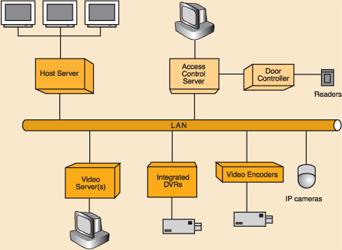
The underlying principle is simplicity in architecture, complexity in information exchange. Important aspects to the integration engineering are as follows:
* Each subsystem can independently carry out its basic function, either providing surveillance monitoring and video recording or controlling access to premises.
* Each subsystem can be interrogated, controlled and in particular configured at an applicable user interface.
* An additional server plays host to integrated system software capable of accessing information from the databases in each subsystem and controlling each subsystem, typically via an application programme interface (API).
* The host server also provides a highly interactive user interface, typically with multiple screens.
* Additional client stations can be added for large sites and for providing remote monitoring on alarm escalation by a security manager.
Integration software packages are available in varying degrees of power, lists of integrated brands and subsequent cost. Some higher-end video surveillance and access control system vendors offer integration with selected brands of the other system type, but a market has also emerged for vendors of so-called independent integration software packages. These are often marketed as enterprise management systems with extensive lists of drivers for equipment that can be integrated (and hefty price tags). Even in our simple integration example the host software should ideally be capable of:
* Allowing an operator to monitor, control and evaluate information for both systems from a single, multiscreen console.
* Displaying system resource information relative to a hierarchical site map with icons indicating position and views of cameras, door states and so on.
* Presenting information on events in such a way as to provide easy understanding of occurrences as well as detailed reporting functionality.
* Processing event triggers to allow for a customised response (rules-based engine) in a logical 'if-then' formula.
* Providing a trend analysis capability to graph long-term trends and to isolate and report on unusual activities.
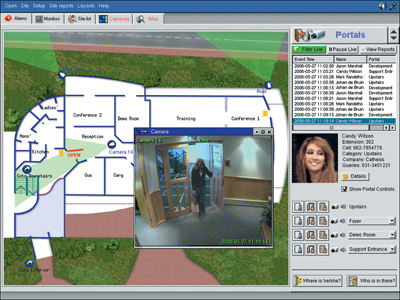
The screen capture of Figure 2 shows a typical example of information presentation. Some of the interesting facilities offered by this integration include:
* Automatic video recording of access events along with access token details and retrieval of historical video based on a search by token number or any other token holder information.
* Generation of alarms due to events such as use of black-listed tokens and forced doors with clear representation of entry point and nearest video camera view on site map.
* Detection of 'tailgating' using video object counting coupled with expectation in token acceptance.
* Trends analysis of entries to determine unusual situations such as excessive overtime, frequent access to areas where employee has no business.
* Tracking of visitors from zone to zone with contiguous video data based on token usage.
* Remote access control by operator based on visual verification of token holder.
These are just some of the more obvious facilities that a well-integrated system can provide - there will be more that can be created on a custom basis. As other systems are integrated, the list of interaction will grow, such as 'open all doors on fire detection system alarming' or 'switch on lights when building accessed after hours' - but that is the subject of a more in-depth look at building management.
Maximising the installation of integrated systems is the domain of the specialist systems integrator with knowledge gleaned from experience.
For more information contact Clive Putman, i to i technologies, +27 (0) 31 562 9535.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.