
Controlsoft has launched new versions of the system controllers most commonly used in KeyMaster Lite and KeyMaster Pro access control systems. In addition to metal enclosures and improved robustness, the new controllers offer installers greater flexibility in configuring access control systems.

Originally developed for the North American market, Controlsoft's latest KeyMaster controllers are all approved by the FCC (US Federal Communications Commission). Controlsoft is also in the process of finalising UL certification.
The first of the new controllers to become available is the AC-3114, an eight-door offline system controller for KeyMaster Lite systems. The AC-3114 is equipped with eight digital inputs, eight relay outputs and an RS485 interface that can support up to 16 devices, including readers, door controllers and I/O controllers. Communication with the Key-Master Lite PC is through a standard RS232 serial interface, which also allows remote connectivity via dial-up modem or an Ethernet/RS232 bridge. A maximum of 32 doors can be set up by using an AC-3114 with AC-3151 door controllers, which provide two Wiegand reader ports, four digital inputs and two relay outputs. The AC-3114 is supplied with a lockable metal enclosure, the latest KeyMaster Lite access control software and a serial cable that connects the controller directly to a PC.
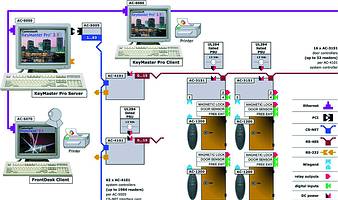
During August Controlsoft South Africa also released the AC-4101, a 32-door online/offline system controller compatible with both KeyMaster Lite and KeyMaster Pro, Controlsoft's flagship building security solution. In addition to the standard RS-232 serial interface, the AC-4101 provides a high-speed CS-NET port that supports data transfer at rates of 2,5 Mbps. The CS-NET interface allows KeyMaster Pro systems to control up to 62 networked system controllers simultaneously. Like the AC-3114, the AC-4101 can control up to 16 RS-485 devices. Each AC-4101 can support up to 32 Wiegand readers via AC-3151 door controllers. Using this architecture, a KeyMaster Pro system can theoretically support almost 2000 card readers, as illustrated in the diagram.
For more information: Controlsoft, 011 463 1102.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.