
You’ve likely seen a list of top 10 passwords that get reused time and time again – ‘password’ is a usual suspect – but what about phone PIN numbers? How unique are the PIN codes that we choose to stop cybercriminals from getting into our phones and their eyes onto our most precious accounts, asks Carey van Vlaanderen, CEO at ESET South Africa.

People tend to lock their phones with a code, but what if someone knew that code or could possibly work it out? Maybe they could guess it from frequently used PIN numbers? Would they then be able to read your emails, send a WhatsApp or view your Amazon basket?
Recent research from the SANS Institute found what the top 20 most common mobile phone PIN codes were (not in order):
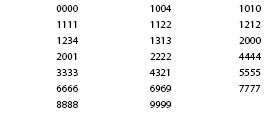
They found that an astonishing 26% of all phones are cracked using these codes. There is a good chance that if your phone is stolen or lost, criminals could get into your phone within their first few attempts – even without knowing anything about you.
So why do people – including Kanye West – continue to use simple codes? Well, it might be best to answer this question first: When did you last change the PIN code to unlock your phone?
Most people have now had a smartphone complete with a lock on it for around a decade and it must be said that in 2007, when the first Apple iPhone came out, we were more interested in its features than discussing attack vectors. Fingerprint readers were a few years off in 2007 and so when we had to enter the code up to 50, maybe even 100 times a day to unlock it, you can start to see why people wanted to get into their phones quickly and easily.
The problem is, even with the introduction of longer codes, Face ID or Touch ID, people rarely change their PINs and settled with a code they use on every device – even though we now rarely unlock our phones with a PIN.
Another method people use to remember PIN codes is to use numbers that mean something to them. However, a threat actor relies on people who tend to have an ‘it won’t happen to me’ attitude, so what if the person wanting to get into your phone knows a little about you? When phones have a 4-digit code, people will often use a year; when a 6-digit code is recommended, people often enter a memorable date to unlock their phone.
This is an extremely dangerous way to secure your most cherished device and allows any cybercriminal with some open-source research skills to trial possible codes to unlock your phone.
What about Face ID or Touch ID? Won’t this fully protect us from attackers? Well, the short answer is no. Many people think that once they have a fingerprint reader or facial recognition on their device that they won’t need to be so hot on PIN code security. Remember that there is still a default code to get into your phone and a hacker can work out this code far more easily than cutting off your finger or replicating your face to open your device.
How to stay safe
The best countermeasure is to start using a long unique alphanumeric code to unlock your phone; then, as this can be time consuming to unlock your device, turn on Touch ID or Face ID to speed up entry.
It might also be a good idea to mention that you should also be aware of your surroundings and who might be watching your movements. Far too frequently on public transport we see people enter PIN codes, passwords, or even on the phone shouting out credit card details including the three-digit CVV number on the back.
Finally, after backing up your device, you should add a further layer of security by turning on ‘Find My iPhone’ for iOS or ‘Find My Device’ on Android, which will allow you to wipe your phone remotely should it ever get stolen (anti-theft and remote-wipe features are also included in reputable mobile security solutions). Even though you may never see that device again, at least the criminals won’t be able to get into your device and look through your personal data and information.
For more information contact ESET-SA, +27 21 659 2000, [email protected], www.eset.co.za

© Technews Publishing (Pty) Ltd. | All Rights Reserved.