
ESET Southern Africa has announced the launch of the 7th edition of its flagship online security products, ESET Smart Security and ESET NOD32 Antivirus.
As the number of social media threats continue to grow exponentially in South Africa, profile cloning and hacking is now an everyday reality, making the need for social media security no longer a ‘nice to have’ but a necessity. Web users now expect to be able to browse their social network(s) of choice in safety, irrespective of platform or device.

Carey van Vlaanderen, CEO at ESET Southern Africa commented “As our use of the Web, mobile and social platforms continues to grow, cybercriminals are capitalising on the opportunity to spread undetectable malware that puts personal information and online identities at risk. Our technology has been built to allow Web users to enjoy the benefits of exploring the Web freely, with the added peace of mind that hidden malware can be easily detected and dealt with before it becomes a threat.”
New features such as the Social Media Scanner and the Exploit Blocker allows for consumers to protect not just themselves from potential threats, but also their friends and followers when using popular social media sites and apps such as Facebook and Twitter.
New security features include:
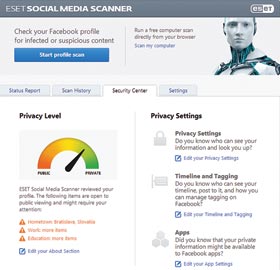
* Social Media Scanner: this app extends your security to Facebook and Twitter. On Facebook, it protects your timeline, messages and newsfeed as well as your friends’ timelines. On Twitter, it protects your prole and posts from those you are following.
* Exploit Blocker adds another layer of protection against new and undiscovered malware to get one step closer to attackers. Exploit Blocker monitors the behaviour of processes, watching for suspicious activity typically associated with exploits. Once triggered, the threat is analysed and if considered suspicious the threat will be immediately blocked.
* Advanced Memory Scanner works alongside the Exploit Blocker to help protect against malware actively trying to evade detection. The scanner detects malware or viruses that would otherwise go undetected by the other security technologies on your PC or mobile device.
* Vulnerability Shield acts as an extension of the Personal Firewall in ESET Smart Security, it operates on the network level and protects against misuse of known vulnerabilities in the network.
Both ESET NOD32 Antivirus and ESET Smart Security are officially certified for Windows 8 and Windows 8.1. To download the new version 7 products and to find out more on the new technology and core features, visit ESET NOD32 Antivirus and ESET Smart Security product pages, www.eset.co.za

© Technews Publishing (Pty) Ltd. | All Rights Reserved.