
The malware charts for the first quarter of the year sees malware related to software piracy ranking high, as outlined by the BitDefender antimalware intelligence data. The Autorun function of removable devices still remains the number one vulnerability exploited by cybercriminals; and illegal advertising holds on to an ‘honourable’ and steady fourth place in the Q1 2011 e-threat top.
Malware distribution for January - March 2011:
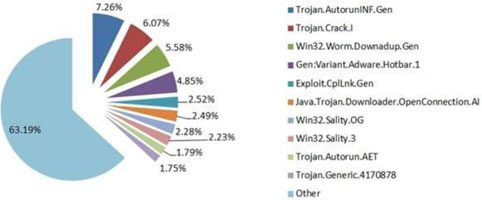
On the highest position in the e-threat distribution chart at the end of Q1, 2011 BitDefender spots Trojan.AutorunINF.Gen that accounts for a percentage of 7,26 from the total amount of detections worldwide. This makes the autorun function of the removable devices vulnerable to malware attacks of all kinds. The constant presence of the worm in BitDefender’s top 5 malware reveals that users are still reluctant to installing security updates from the operating system vendor.
Trojan.Crack.I accounting for a percentage of 6,07 points ranks second after only a few months of existence. It should be mentioned that this application generates unauthorised registration keys in order to defeat the commercial protection of shareware software products. It may also try to collect details about further applications that run on the compromised computer (name, version, registration keys etc,) and send them to a remote attacker who would subsequently sell these licenses as OEM Software.
Win32.Worm.Downadup.Gen ranks third with 5,58% from the total number of infections registered worldwide this first quarter of 2011. There are countries like the United Kingdom where this malware saw a significant drop in detection, but there are other regions where it still dominates the malware charts (like Romania and Spain). This worm’s agenda is well-known by now: amongst others, it prevents users from accessing both Windows Update and security vendors’ web pages, while also downloading rogue AVs on the compromised computers.
Gen:Variant.Adware.Hotbar.1 accounts for 4,85% of the total amount of malware which places it fourth in this year’s quarterly malware distribution chart. Gen:Variant.Adware.Hotbar.1 forces pop-up messages on users’ PC screens, while also initiating new browser windows usually located on the right side of the desktop. This family of malware is also capable of browser hijacking, which means that most of the search queries will be routed to various ad campaigns which boost the attacker’s advertising revenue. This adware tool can be used to gather data on the surfers’ habits in order to serve targeted ads or shopping suggestions.
The fifth place in this quarterly malware top goes to Exploit.CplLnk.Gen - a detection specific to lnk files (shortcut files) that makes use of a vulnerability in the Windows OSes to execute arbitrary code. This exploit has seen a significant boost these past few weeks and it is expected to spread even further. It is also one of the four zero-day exploits that have been intensively used by the Stuxnet worm to compromise local security.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.