
PayPal, eBay, HSBC top-phished institutions; China and Russia hosting majority of malware - predictions for malware activity over the second half of the year
BitDefender has released a report that found the first half of 2010 saw a rise of worms exploiting various Web 2.0 platforms. The report examined data from January through June 2010 and found social networks and Web 2.0 services have become one of the most valuable channels of malware dissemination during the last six months, while phishers focused on impersonating PayPal and eBay, and pharmacy spam volume now makes up two-thirds of all spam.
Spam and phishing trends in first half of 2010
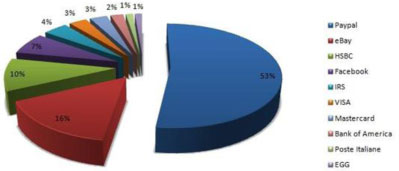
Financial institutions were cyber-criminals’ preferred targets, constituting more than 70% of global phishing messages. Social networks also came under heavy fire, as user profiles are a rich source of personal information and compromised accounts may be effectively used in spear phishing attacks. For the first half of 2010, phishers focused on impersonating PayPal and eBay. The HSBC Bank ranks third, while Poste Italiene and EGG conclude the list of the most abused online identities.
The FIFA World Cup and the massive floods in Guatemala were two of the many events used for Black-Hat SEO optimisation to improve the ranking of various malware-serving websites in the first half of 2010. The period also saw spam messages grow to 86% of the total e-mail, driven by pharmacy spam, which reached new heights - jumping from 51 to 66% of all spam.
The spam breakdown by type for the first half of 2010 is:
* Medicine Spam – 66%
* Replica products – 7%
* Loans and insurance – 5%
* Bundled malware – 3,5%
* Casino and gambling – 3,5%
Malware threats in review
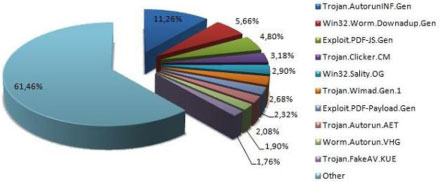
Exploiting Windows’ Autorun feature - Trojan.AutorunINF.Gen ranked first in the study, with more than 11% of the total number of infections, while MBR worms have made a comeback with upgraded viral mechanisms. Late January saw the emergence of Win32.Worm.Zimuse.A, a deadly combination of virus, rootkit and worm. Upon infection, the worm would start counting down the days. 40 days from the infection, it would overwrite the hard disk drive’s Master Boot Record, thus rendering the OS unable to boot. China and the Russian Federation led the world in malware hosting, with 31 and 22% respectively.
Vulnerabilities, exploits and breeches
Critical zero-day exploits on popular software such as the Internet Explorer browser from Microsoft or Adobe Reader, Adobe Flash Player and even Adobe Photoshop CS 4 have also played a key role in the malware landscape for the first half of 2010. Some of the Internet Explorer exploits have even been used to attack major companies such as Google, Adobe and Rackspace.
E-threat predictions
BitDefender experts warn, while the first six months of 2010 have been dominated by conventional e-threats such as Trojans and worms, various exploits pointing at third-party applications have rapidly gained ground, both in count and in terms of impact. As seen in the case of Exploit.Comele.A, zero-day vulnerabilities may be used for purposes that are beyond identity theft or compromising banking accounts, but instead act as fully-fledged weapons used in cyber-warfare and top-level industrial espionage.
“With Facebook surpassing 400 million users, most of the malware authors will focus on the social networking platform to deliver their newest payloads. Some of these attacks will focus on social engineering tricks (such as launching various malware offensives from compromised computers), while others will try to exploit different vulnerabilities or features already implemented across the platform,” said Catalin Cosoi, head of the BitDefender Online Threats Lab.
BitDefender experts also believe personal information leaks will also dramatically contribute to the success of various attacks, especially when data harvested from social networks is corroborated with personal blogs, career history and other relevant data. Third-party applications are also expected to play an important role in social networking abuses.
“The introduction of HTML5, the upcoming major revision of the HTML standard, will add extra levels of interaction between the user and the webpage and will probably change the face of the Web as we know it. The new technology is highly likely to be exploited by malware authors to compromise the browser security,” added Cosoi.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.