
Social networking is so good even for illegitimate marketing campaigns.
How would you like to get one of the much-anticipated iPad gizmos in exchange for simply filling up a mere survey? Well, the offer sounds pretty good – in fact, it sounds too good to be true and that is what it is.
The scheme is massively advertised on a Facebook Events page where about 2500 people signed up for the event and – probably – fell victim to the phishing attack. The idea behind it is extremely simple: you sign up for 'reviewing' an iPad device, get the product and a questionnaire you need to fill in and return to the company. Needless to say that you get to keep the reviewed item without any commitment on your side.

Concealed by a short URL, the target phishing page initially asks for some pretty reasonable info such as the first name and the e-mail address, and culminates with requiring a full set of details, including the full name, home address and phone numbers, as shown below. In order to make the whole deal look legit, the attackers have thrown in logos belonging to high-profile media outlets, although the mentioned institutions have no clue about this initiative.

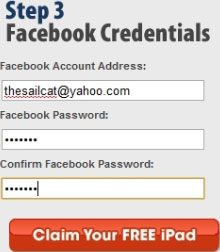
After all the data has been collected, the attacker asks the user to undergo a last security check and provide their Facebook username and password. Please note that our experiment is carried in a contained environment and we do not encourage you to type in your account credentials on any website except for the genuine one.
To add insult to injury and to maximise the damage, the unwary user whose account has just been phished would be required to download and install an adware application (a browser toolbar) that hijacks the browser’s start page and swaps the default search engine, among others.
Needless to mention that, after filling in the personal details, getting phished and installing the toolbar you will never get the iPad, nor will you hear from the attackers again.
The scheme is based on a common practice amongst product creators, namely sending sample units for reviewing.
However, it is not everybody who can receive a testing unit, as the offer is mostly pointed at opinion influencers, high-profile bloggers and – most of all – specialised review websites. Even that way, journalism ethics urge that the reviewer returns the tested unit to the provider after the process has completed. Now, repeat after me: if something looks too good to be true, than it probably is and you will end up hurting yourself.
Facebook has been notified and the Events page has been taken down.
In order to stay safe, BitDefender recommends you to follow the security tips below:
* Do not enter your personal data and do not download or save files from sources you do not know; use only the producer’s official website.
* Install and activate a reliable security solution .
* Update your antimalware, firewall and spam filter as frequently as possible, with the latest virus definitions and suspicious application/file signatures.
* Scan your system frequently.
For more information contact Aline Anton, senior PR and marketing coordinator, EMEA & APAC Business Unit, BitDefender, [email protected], www.bitdefender.com

© Technews Publishing (Pty) Ltd. | All Rights Reserved.