
The 'big name' cybercrime series continues with an alleged Office 2010 Beta version used as bait.
Just a week after the alert on the fake Windows 7 compatibility checker, another interesting e-mail came into Inbox. The subject? 'See Office 2010 Beta in action'.
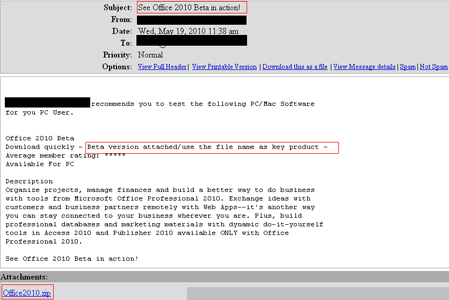
This enticing title accompanies a message which reveals to the user what is new in this Office version. Rated by members with five stars (out of five, of course), this Beta version appears too hot not to be tested. It is like … a must. To save the users’ time and get them down to this ardent matter as soon as possible, the promised beta version is attached to the message as a zip file. Quite suspicious, is it not?
When extracting it, the attachment reveals me an exe file baptised under a baffling string of letters and figures, much in the style of a product key. This name is actually the product key users must input in order to activate the beta product.
However, a detailed file check exposes the fake beta as malware.
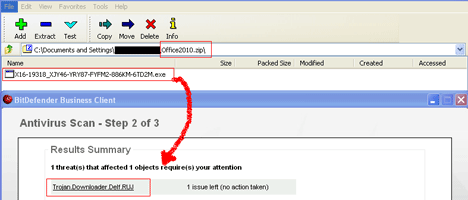
Identified by BitDefender as Trojan.Downloader.Delf.RUJ, this piece of malware affects the Windows platform. It is designed to infiltrate the user’s computer and open a conduit by which large amounts of adware and spyware can be piped into the affected system, therefore generating loads of popup adverts. Once installed, the Trojan creates a copy of itself into the

© Technews Publishing (Pty) Ltd. | All Rights Reserved.