
New variant of Palevo blasts unprotected systems via fake photo gallery links.
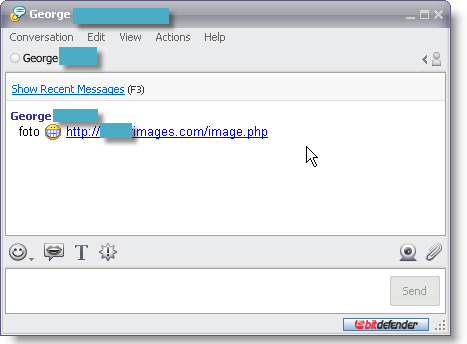
The latest offspring of the Palevo family has begun spreading these days via a massive wave of automatically generated IM spam. The unsolicited message incites the recipients to click a link accompanied by a grinning smiley face, which purportedly leads them to an image or photo gallery.
Instead of opening the alleged image collection, the users are tricked into saving what seems to be a .JPG file, which is, in effect, an executable concealing the malicious payload – Worm.P2P.Palevo.DP.
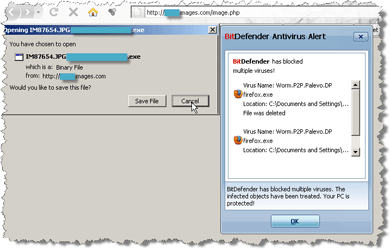
Having an unprotected system infected with Palevo.DP is a synonym for mayhem. First and foremost, the worm creates several hidden files in the Windows folder: mds.sys, mdt.sys, winbrd.jpg, infocard.exe and modifies some registry keys to point towards these files in order annihilate the OS' firewall.
As its siblings, Palevo.DP holds a backdoor component, which allows remote attackers to seize control over the compromised computer and do whatever they want with it – from installing additional malware and swiping files to launching spam campaigns and malware offensive on other systems.
Palevo family is also able to intercept passwords and other sensitive data entered in Mozilla Firefox and Microsoft Internet Explorer Web browsers, which makes it extremely risky to users relying on e-banking or on-line shopping services.
The spreading mechanism also comprises the infection of network shares and removable USB storage devices, where it creates autorun.inf files pointing to its copy. When the removable disk or memory stick is inserted into machines with the Autorun feature enabled or unprotected by a security solution with on-access scanning capability, the system is automatically infected.
Palevo worms also affect users of the P2P sharing platforms, such as Ares, BearShare, iMesh, Shareza, Kazaa, DC++, eMule and LimeWire, by adding their code to the shared files.
“We recommend users to be extremely cautious and not to click any suspicious links they receive via IM clients before checking with their senders the validity of the Web sites towards which these links point. This Palevo offensive is highly aggressive and during the very beginning of the outbreak we have witnessed rates of infection which easily exceeded 500% growth per hour for countries like Romania, Mongolia or Indonesia”, said Catalin Cosoi, BitDefender senior researcher.
For additional information about e-threats and tools for defending your data and systems check www.malwarecity.com
For more information contact Alina Anton, senior PR & marketing coordinator, EMEA & APAC Business Unit, BitDefender, +40 212 063 470, [email protected], www.bitdefender.com

© Technews Publishing (Pty) Ltd. | All Rights Reserved.