
The physical security element is controlled by the security department while the logical security is controlled by the IT department. Both utilise databases of people and information about where and when they are allowed to access system resources.
Today they can operate in conjunction with each other by deploying a common credential, such as a smartcard at the personnel level and unified single user interface at the system administrator level.
The smartcard is a logical point for the convergence primarily because it is a shared real estate item that has a contact smartcard used for logical security systems and a contactless smartcard used for physical security systems. The fact that this is a common carrier for physical and logical security credentials is driving the two departments to work together out of necessity.
This is the single biggest factor that is driving physical and logical integration. It is forcing both organisations to understand how the card and its data are managed and maintained. It is forcing the two organisations to work together on policies for encoding, printing and distribution.
Corporate security policies are naturally evolving, such that logical and physical security systems will share and utilise the same infrastructures. Physical security systems are utilising corporate computing resources such as network backbone, anti-virus software, firewalls and data centre servers to provide a stable platform for the physical security system. The logical security systems are utilising the corporate access card to leverage biometric deployments and cashless vending systems and secure login as a way to strengthen the security of their computing infrastructure.
With the utilisation of shared resources, it is a natural progression that the security policies will extend between the two systems. It does no good for a cardholder to be deactivated from using his/her badge for accessing a building when the certificates on the badge are still active for accessing the corporate network.
Today, these two infrastructures loosely communicate between each other. As the natural downsizing and consolidation of security functions occur, the management and monitoring of these systems will move to a single user interface. The security system of the future needs to have the ability to manage several sets of disparate data. An integrated framework is needed to support these two systems.
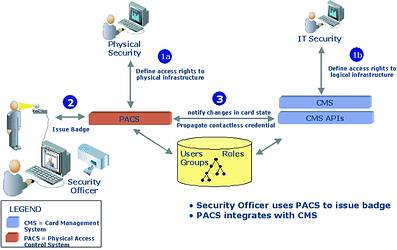
To address segregation of responsibilities (physical and logical security fiefdoms), the roles and responsibilities of the end users must be separated such that the same application can be used to manage the systems, but the data can be viewed and managed independently if needed.
As one is implementing business policies it is imperative that consideration is given to the deployment realities before implementation. The software and the card tokens are simply the tools used to implement the processes and business practices of the organisation. Whilst policies and practices can be updated based on the capabilities provided by these new tools, the starting point must be to have the existing rules clearly defined for all stakeholders at the outset.
In order to identify and clarify these rules it is important to run through a pre-deployment checklist, which should at least ask the following questions:
The credential
* Who determines the topology, layout and colour schemes of the card?
* Who determines the level of interoperability required?
* Who determines the level and types of encryption required?
* Who performs background checks or security clearances?
* Who controls assignment of a credential number for new users, contractors, interagency or department transfers?
* Who determines non-standard functionality?
Access permissions
* Who assigns physical access permissions?
* Who assigns logical access permissions?
* Who administers physical access permissions?
* Who administers logical access permissions?
The database
* Which system will be the 'Master' database?
* Who secures and houses the Master database?
* Who controls the 'Hot List' of deactivated/invalidated credentials?
* Who establishes communication between the Master database and physical access control system?
* What is the frequency of updates?
* What type of data feed is used between the Master database and physical access control system?
Before implementation of the system it is vital that the IT department is fully engaged so as to establish network infrastructure requirements such as VLANs, assignment of dedicated IP addresses and DHCP ranges etc.
Let the application drive the technology
In conclusion it is vital to the success of the project that the goals are fully defined at the outset, having done this it is then possible to pick the appropriate technologies to meet them. Do not fall into the trap of focusing on the 'kitchen sink' approach for smartcard systems, rather pick essential elements and build upon them. Identify the needs both today and in the future and reconcile them with both your budget and projected savings.
For more information contact Phil Mailes, Lenel, 0944 148 381 5234, [email protected], www.lenel.com

© Technews Publishing (Pty) Ltd. | All Rights Reserved.