
ShrinkStop offers a secure goods custody transfer solution for receiving and distribution centres.
ShrinkStop is a joint venture between ProLoCon, which does the Windows software development, PLCs and automation, system integration and user training; Multivid, responsible for the video cameras and peripherals, digital video processing, digital picture storage and remote retrieval via network; and Interbelt which provides the materials handling solutions, conveyor systems, diverters, cages and project management.
Using a combination of software, labelling, conveyor and video archiving systems, ShrinkStop provides a complete solution for shrinkage.
With billions of rands being lost each year through shrinkage, manufacturers, distribution centres and retailers require a system that will allow them to accurately track the receiving and despatch of stock and assist traceability in the supply chain.
Software developer ProLoCon has created ShrinkStop to address this need.
'Smart' weighing allows the administrator to pre-set tolerances per item. Working in conjunction with either an in-motion check-weigher or a static scale, items can be weighed, accepted or rejected and then placed into storage or quarantine. Incorporating a scale in the receiving procedure means that empty or 're-packed' boxes can be identified and rejected.
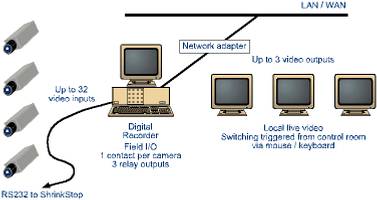
ShrinkStop connects to bar code scanners/printers; static scales; high-speed in-motion scales; conveyor system; and security video systems.
The system can operate with any scale or check-weigher that provides an RS232 interface.
Extensive reporting features allow administrators to accurately track stock items as well as track items that have been moved to 'quarantine'.
ShrinkStop incorporates powerful import, export and data validation wizards to facilitate secure data transfer of item master file, orders pending and goods movements to and from host systems such as SAP, JD Edwards and Syspro.
For an administrator, ShrinkStop, provides the ability to link to a specific purchase order number, sales order number and automatically print a goods received or despatch note. A secure audit trail is generated.
For more information contact Andrew Ashton, ProLoCon, 011 465 7861/2, [email protected] or Charles Volschenk, Multivid, 011 894 7127, [email protected]

© Technews Publishing (Pty) Ltd. | All Rights Reserved.