
Peer-to-peer communications enables Cardax FT controllers to communicate with each other for the purposes of monitoring, back up and control. This achieves efficient and flexible system design and, most importantly, upholds site security without the need for a centralised communications server.
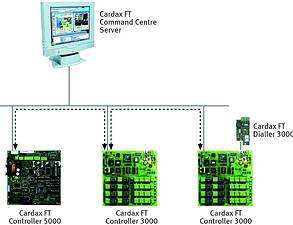
Cardax FT controllers can directly communicate with other Cardax FT controllers (3000 or 5000), over a LAN/WAN using TCP/IP, without the Cardax FT Command Centre. Distributed intelligence means the controllers will operate independently of the head-end server, preserving the security and access control of the site should the site experience network communications problems.
Peer-to-peer communications is a significant feature that provides extensive flexibility and efficient system configuration and allows for a global link of inputs and outputs. Inputs on one controller can be monitored and acted on by another controller.
For example, a single Cardax FT Remote Arming Terminal resident on one Cardax FT controller 3000 can be configured to control and monitor events and the security status of other alarm zones on any Cardax FT controller. The Cardax FT Remote Arming Terminal can control up to 30 alarm zones and 100 inputs located on any other controller controller residing in the system. This kind of efficient system design clearly has an impact on the cost of installation and simplicity of site design
For alarm monitoring, a Cardax FT Dialler resident on a Cardax FT controller can be configured to transmit events originating from other Cardax FT controllers to a remote alarm monitoring station.
Peer-to-peer communications is one important feature incorporated in Cardax FT - the level of encryption is another consideration for system integrity, as is card data encryption.
For more information contact Gallagher Security Management Systems, 011 397 2986, [email protected], www.gallaghersms.com
| Tel: | +27 11 971 4200 |
| Email: | [email protected] |
| www: | www.gallagher.com |
| Articles: | More information and articles about Gallagher |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.