
The outpour of video-based scams on Facebook has probably set us all wondering how much effort scammers are forced to invest in their not so honourable exploits. Is there a scammer sweatshop packed with tiny slaves digging up the latest tricks in scam propagation techniques? Or does launching a scam wave simply mean pushing a big red button that reads SCAM AWAY?
Knowing scammers’ propensity for easy gains, I took a closer look at some of the suspicious apps recently detected by Bitdefender Safego only to find that their wildfire pattern of propagation is mostly due to the use of a classic technique used in malware and spam dissemination: domain name adjustment. Cannot teach an old dog new tricks? With Facebook scams, these words of wisdom get a twist: it is actually not worth trying to.
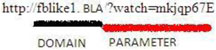
For those of you who are not very familiar with the structure of a domain name, here is an illustration of the two main concepts: the domain and the parameter.
Now let us see how the domain name adjustment technique applies to Facebook scams.
1. Same domain + random strings
http://fblike1.bla/?watch=mkjqp67E
http://fblike1.bla/?watch=tI8j4osB
http://fblike1.bla/?watch=shDcEp1r
http://fblike1.bla/?watch=xnF5slCz
http://fblike1.bla/?watch=6vddD91s
In this case, you can see that the scammers started from the fblike1.bla domain and generated a random string of precisely eight figures or letters in order to create each unique page. The addition of the ‘watch’ particle in the URL parameter is intended to lure users to access the page.

2. Slightly varying domain + random strings
http://fblike3.bla/?watch=sIzfC7Dx
http://fblike3.bla/?watch=q5FzyjDu
http://fblike10.bla/?watch=EqI3etxh
http://fblike10.bla/?watch=oefdghwm
Using just one domain will not take you too far, and that is because of a minor detail such as blacklisting. In this particular case, the scammers started from fblike and gradually added figures to it. The fact that we do not see ‘fblike2’ or ‘fblike4’ in here is just because these domains are on hold for the current attacks. However, be sure that they will be used in the near future.
Just as in the previously described set of examples, ‘watch’ is followed by a randomly generated string of precisely eight figures or letters.

3. Completely different domains
http://www.gevid34.bla/index3.php
http://www.deuadfge.bla/index3.php
http://www.lozldager.bla/index3.php
http://www.vidzdelol.bla/index3.php
http://www.loldelol.bla/index3.php
http://www.videz24.bla/index3.php
This set of URLs illustrates how the scammers switch to generating completely different domains to serve their purpose. While they used key words such as ‘vid’ (from video) and ‘lol’ in order to increase the attractiveness of these domains, they kept the latter part of the URL the same, which undermines the propagation efforts by making detection easier.

5. Ultimate randomisation
http://is8roadfh.vo692n.bla/index.php?id=203755
http://9mf0roadfh.5bf26a.bla/index.php?id=63385
http://z0p8roadfh.tw5alg.bla/index.php?id=265250
http://ihw2roadfh.axw8zd.bla/index.php?id=273788
These are more complex examples. Each URL contains three different strings that are computer generated.
1. A string of 9 or 10 letters or figures, which is the sub-domain.
2. A string of 6 letters or figures, which is the actual domain.
3. A string of 5 or 6 figures, which is the URL parameter.
This variety of the domain name adjustment method can be used to generate a huge number of URLs. If we were to make an estimate of the total number of possible domain combinations, we would end up with a staggering 2 176 782 336. (six times each letter and figure).

http://z0p8roadfh.bpq20t.bla/index.php
http://proninadfh.5tdgh5.bla/index.php
In a less sophisticated form of the ultimate randomisation variety (illustrated in the two examples above), the parameter stays the same, which decreases the number of possible URLs.
So, what does all of this mean? URL blacklisting is becoming less and less efficient as scammers manage to generate a huge number of domains for each scam wave. It is precisely because of this that Bitdefender Safego, for instance, uses heuristic scanning in order to provide more accurate detection.
This article is based on the technical information provided courtesy of Tudor Florescu, Bitdefender Online Threats analyst.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.