
Phishing is known to be the weapon of choice for all cybercriminals that are after login credentials. However, a new attack tool – Facebook Hacker - has drawn attention to the criminals in need of passwords and usernames that are not theirs. This do-it-yourself kit helps the wrongdoer steal login credentials from whoever was targeted without the user even having to type in any of these details.
The kit is intuitive, thus extremely easy to configure, just like any do-it yourself hack tool designed with the 'skiddie' in mind. There are only two fields that need filling in: a disposable e-mail and a password that will eventually constitute the location where the stolen information is to be delivered to.
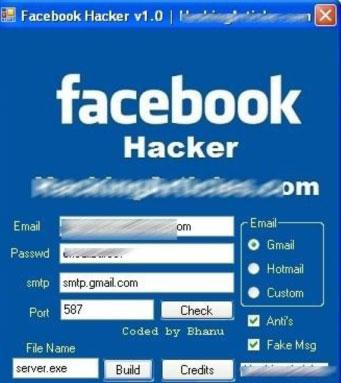
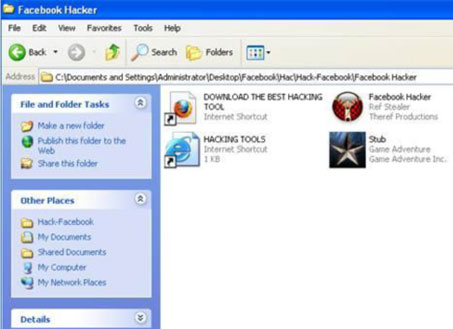
After clicking the 'build' button, a server.exe file is created and deposited into the facebook Hacker folder along with the initial files. This server.exe file is to be sent to the intended victims.
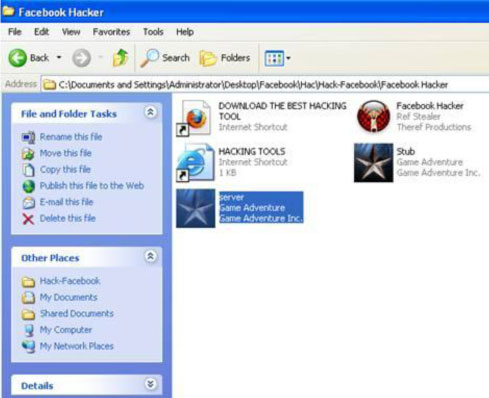
Once run, the malicious tool will snatch the victim’s Facebook account credentials, along with all the usernames and passwords that we carelessly ask the browser to remember for us. Facebook Hacker also targets the Internet browser and Instant Messaging clients to pick up the user’s 'remembered' identification data.
In order to successfully collect passwords, the malicious binary includes applications able to squeeze data out of the most popular browsers on the market, as well as of almost all instant messaging clients available. To add insult to injury, the application also enumerates all dialup/VPN entries on the computer and displays their logon details: user name, password, and domain.
To avoid detection, the facebook Hacker will also look for all the processes related to a security suite and kill them upon detection. It is important to mention that it is accessorised with a hard-coded list of processes associated with AV solutions that are to be checked and stopped, if found.
Last but not at all the least, the piece of malware looks for network monitoring applications and terminates them. This is a safety measure that will prevent curious users from seeing their passwords leave the system.
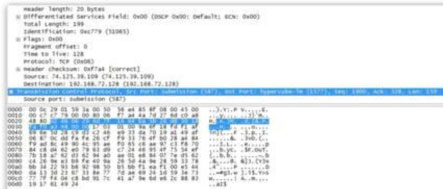
As can be seen, the author took a lot of time to think of various elements that could interfere with the smooth operation of this tool and to eliminate them one by one.
All product and company names mentioned herein are for identification purposes only and are the property and may be trademarks of their respective owners.

BitDefender identifies this threat as Trojan.Generic.3576478. In order to stay safe, please ensure that you are running a frequently updated antivirus utility. Also, remember not to run files you may receive as attachments or via IM, or at least, to scan them beforehand.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.