
According to Kaspersky Lab’s report ‘Information security threats in the first quarter of 2010’, Adobe products are currently the primary target for hackers and virus writers worldwide due to their prevalence and multiplatform capabilities. Furthermore, users of Adobe products are often unaware of the potential threat they are incurring by opening PDF files of unknown origin.
Among the many varieties of exploit that were detected, the Exploit.Win32.Pdfka family with 42,97% was by far the most popular. This exploit takes advantages of vulnerabilities in Adobe Reader and Adobe Acrobat.
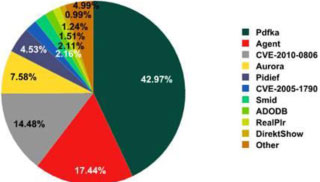
The Top 10 exploit families detected on the Internet
When added together, two families of exploits targeting Adobe products, Exploit.Win32.Pdfka and Exploit.Win32.Pidief, account for a total of 47,5%, or nearly half of all detected exploits. These exploits are PDF documents containing Javascript scenarios that, without the user’s knowledge or consent, download and launch other pieces of malware direct from the Internet.
The report highlights the fact that many users of Adobe products have not installed the patches designed to remove the software’s vulnerabilities and therefore remain susceptible to attack. Among the top 10 most prevalent software vulnerabilities detected on users’ computers over the first three months of 2010, three were found in Adobe products, six were found in Microsoft products, and one was found in a Sun product. The three vulnerabilities targeting Adobe’s programs were found on 23,37%, 17,87%, and 15,27% of the computers examined, with the first and last being critical vulnerabilities that allow remote hackers to take full control of a system.
One of the vulnerabilities in Adobe’s products that became public knowledge over three years ago has had a patch available for all that time, which just goes to show that many users are still not updating their software. In order to resolve this problem, on 13 April Adobe launched an automated update service that runs in the background. Developers are hoping that this will help to reduce the number of unpatched applications that are so appealing to the cybercriminals.
The full quarterly report, titled Information security threats in the first quarter of 2010, can be found at www.securelist.com

© Technews Publishing (Pty) Ltd. | All Rights Reserved.