
Thales’ 2016 Global Encryption Trends Study, independently conducted by the Ponemon Institute examines how the use of encryption has evolved over the past 11 years and the impact of this technology on the security posture of organisations. Interestingly, over this period there has been a complete reversal in the number of organisations with no encryption strategy (38% in 2006 and 15% in 2016) and those who deploy encryption technology across the board (15% in 2006 and 37% in 2016). (Source: www.thales-esecurity.com)
Another interesting finding is that 61% of respondents see compliance with privacy and data security requirements as the main driver to extensive encryption use within their company. While this is primarily based on the US and European markets, where protection of personal information is in the advanced stages, the impact of PoPI is set to gain ground in South Africa in the coming years. At least half of the respondents see protecting enterprise intellectual property as the main driver.

Barry East at Impro Technologies echoes these sentiments, adding that in order to understand why encryption technology has become increasingly popular, one needs to understand the challenges of the market. In addition, while all industries face similar challenges in this regard, there is no doubt that specific applications, such as the banking and financial services sector, present a generally higher level risk than other markets.
East says that encryption technology was initially slow to gain traction in the market. Tagging systems gradually became more secure but at that stage RFID cards had read-only capabilities. There has subsequently been an explosion of read-write based technologies where users can write information back on to the card. This has been widely accepted in Europe and the United States where the protection of privacy around storage of fingerprints on hackable databases is of major concern to corporations.
Encryption success factors
Critical to the success of any encryption technology are three factors: How is the information being captured, how is it being stored and how is it being used once it is captured? East points out that Joe Public has become more aware of the multiple risks apparent when information is accessible in the public forum. Hence the necessity for a more secure mode of handling sensitive personal information.
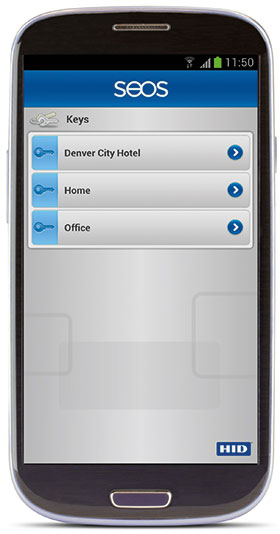
Impro is currently adopting parent company ASSA ABLOY’s SEOS credential technology to address these concerns. This application-based encryption methodology allows information to be modified on the fly across a broad range of media.
Leveraging the SSL standard adopted by financial institutions, SEOS is geared around maximised risk mitigation. Information gathered by users can be stored on a number of media, including a digital database available on smart mobile devices such as laptops, tablets and cell phones, on physical devices such as readers, or on smartcards. The information captured will then be used to confirm or deny access to either a device or a location.
Interestingly, the nature of the industry and encryption technology has now evolved outside that of serving just traditional access control applications. East says that there are apparent major benefits being derived from supplementary elements, such as those encountered in universities. Here, students use their student cards to not only access the facilities, but additionally check out library books, to log in to computers and download data in the IT department, and to buy food in the cafeteria.
Mobile expands functionality
So just how do users manage the control of this credential across multiple media? What about using mobile technologies to expedite these functions? East says that mobile technology is increasingly coming to the fore, with both Bluetooth and NFC capabilities allowing users to safely perform the functions traditionally assigned to RFID cards. In addition, VISA and Mastercard credit cards are joining the ranks of an increasing number of devices and tools installed with microchips to allow them to be used in multiple ways. A solid example of this technology in practice is the use of credit cards to provide access to London’s Tube system, instead of needing to use the common currency of an Oyster Card.
East says that an entire ecosystem of data capture through to the issuing of data across multiple media is arising to manage the encryption process during the capture and dissemination of data. The challenge has been in developing a technology that seamlessly switches on the technologies needed to provide maximised effect for these applications.
Impro, well known for its access control technologies, believes that SEOS is the optimum ecosystem for its products. Going forward, the company will systematically introduce SEOS as a standard across its entire access control based range. Adoption of this platform means that mobile devices can now be used by registered users to gain access into premises and to guarantee that the storage and management of this information is secure and centrally managed.
International standards
The SEOS protocol was derived from the best in class standards defined by the National Institute of Standards (NIST) and during the provisioning of digital keys to the selected mobile device, it establishes a mutually authenticated channel between the provisioning service and the mobile device to ensure the safe delivery of the key material. Similarly, when the credential is being used, a mutually authenticated channel is established between the mobile device and the relying party application.
Identity credentials are encrypted while in storage on the mobile device. In addition to encryption keys based on the underlying mobile operating system, the SEOS vault can also be implemented as an applet which executes in a SIM chip or Secure Elements for greater levels of protection. A cautionary note here, says East, is that the latter will introduce dependencies on the underlying hardware and the mobile network operator.
The encryption on cards is high end but due to the tangible benefits of the technology, there have already been a number of deployments into a various solutions in South Africa. “As soon as you realise how quickly your credential can be used across multiple media, you realise that you as an individual have control over these platforms using encryption technology. SEOS helps to ensure that these credentials remain encrypted until they are needed,” says East.
Impro’s Vikki Vink adds that in simplistic terms, the greatest benefit of an application-based encryption method such as SEOS is the enhanced security it offers and the ability to upgrade or update is radically quicker and easier than the traditional chip-based method.
“If a card is hacked, the hacker now has access to the cards using that chip. In order to stop the hack, you have to recall each unit and make a hardware change by changing the chip. With an application-based encryption method, should there be a problem, you only need to push an update to rectify the issue. This is where the future proofing is so critical. It means that it will be much easier in the future to protect against issues that we haven’t yet experienced. With the increased demand for convenience, this future proofing and the ability to quickly react to a possible problem, is crucial. With added convenience, risk often increases but by using SEOS technology, this risk is minimised,” Vink says.
For more information contact Impro Technologies, +27 (0)31 717 0700, vikkiv@impro.net, www.impro.net
| Tel: | +27 31 717 0700 |
| Email: | info@impro.net |
| www: | www.impro.net |
| Articles: | More information and articles about Impro Technologies |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.