
Powell Tronics helps provide complete assurance for high-risk security client.
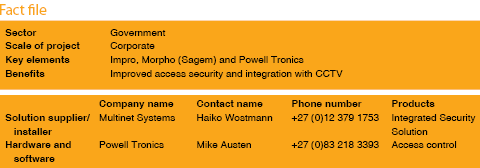
Powell Tronics recently supplied access and identity management equipment for Multi-Net’s contract to install a complete building safety and security system at a newly revamped government building in Gauteng.
The Impro, Morpho and Powell Tronics branded products supplied by Powell Tronics, for a 25-door access control system on all building wings and fire doors, had to integrate with the CCTV, the fire system and the PA system.
Because Multi-Net has a wide reference base in terms of installation experience, Powell Tronics’ input was limited to providing products and assisting on the integration process. Haiko Wöstmann, project manager at Multi-Net, explained that the company has worked with Powell Tronics in the past on smaller projects and had decided to include them on this large-scale contract due to the suitability and reliability of their product range.
The project plan was fast tracked, but due to delays incurred because of technical specification changes from the client, the installation was deferred for a couple of weeks. “Nevertheless, we still successfully turned the entire project around in eight weeks,” said Wöstmann.
Powell Tronics was given a three-week lead-time to source and deliver to Multi-Net. “We improvised for the external access points by providing Morpho indoor biometric readers on a temporary basis until the outdoor readers arrived,” Powell Tronics regional manager Mike Austen explained. The MorphoAccess outdoor readers have been developed specifically for outdoor applications and include ruggedised/weather-resistant housing.
Since not all personnel and visitors are permitted to enter the high-risk areas within the building, it was necessary to provide different security levels for the various entry points into the building, so the Impro IXP400 ECii system controller was configured to accommodate this factor. “The system incorporates Impro Touch for unlocking MorphoAccess readers and Impro Vision to unlock the Bosch CCTV interface,” Austen said. “Full integration into the other safety and security systems within the building provides the building’s high-profile occupants with assurance of complete protection.”
Adding another level of security assurance are the RFID cards issued to both personnel and visitors to the building.
Other products supplied
Impro equipment
* IXP400 – ECii System controller. Each controller can control 3000 doors, accommodate 300 000 tag holders and buffer 1 000 000 transactions.
* Impro Access module and engine.
* Impro Touch – Unlock for MorphoAccess readers.
* Impro Vision – Unlock for Bosch CCTV interface.
* Drop box with mechanism, reader and door controller.
* 16 channel input and 16 channel output terminals for door monitoring.
* ImproNet utilities to unlock workstations to access reports and to take on visitors.
* iTRT – second generation intelligent door controller.
Powell Tronics equipment
* P-Tron magnetic locks and brackets.
* P-Tron break glass units.
* P-Tron push buttons.
* P-Tron door loops.
* P-Tron keyed override switches.
Morpho equipment
* MSO300 (Everif) – Take on reader with embedded verification dongle.
* OMA520+ – Outdoor reader with Mifare card reader.
* MA520+ – Indoor reader with Mifare card reader 1:3000 people.
* MA120+ – Indoor reader with Mifare card reader 1:500 people.
“Powell Tronics supplied all required access equipment on time and within budget, allowing us to hand over a complete building security system to a satisfied customer who can now rest assured that no invalidated access to the building will be permitted by this sophisticated system,” Wöstmann concluded.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.