
South Africa is renowned for an abundance of mineral resources, accounting for a significant proportion of both world production and reserves. South African mining companies dominate many sectors in the global industry. In 2010, this sector contributed 18% of GDP (8% direct, 10% indirect and induced).
South Africa is in fact the world’s biggest producer of platinum and one of the leading producers of gold, base metals and coal. The country’s diamond industry is the fourth largest in the world, with only Botswana, Canada and Russia producing more diamonds each year. The country produces 10% of the world’s gold, and has 40% of the world’s known resources. In a recent survey, South Africa was listed as the world’s fifth largest mining sector measured by real GDP.
With this wealth comes the problem inherent to any high-value market – theft of resources. Hi-Tech Security Solutions spoke to a mining house and three security solutions providers about the trends in security within the sector.
A number of risk factors impacts on the profitability of the sector, not least of which are issues with perimeter control, illegal underground mining and theft. It is alleged that (according to the ISS) up to 10% of all gold that is mined in South Africa is stolen before it can generate a profit for the mining houses.
From the outside in
Gold Fields is one of South Africa’s top six mining houses and ranks as the country’s second largest gold producer. Nash Lutchman, group manager protection services for the Gold Fields Group, said that the mining sector’s biggest threat is from the large number of syndicates who target this high-end portion of the market.
“These syndicates are divided into two very clear groups – the smaller, opportunistic unorganised criminal element that is happy to make a living on the scraps. However, the more potent and scary threat comes from those syndicates that are more sophisticated, more organised, generously funded and which have very well developed plans of action in place to maximise their illegal gain,” said Lutchman.
According to Lutchman, the large syndicates provide the capital for infiltrating the mining operations and coercing or compromising the mine employees to work in collaboration with them.
“There are other factors to mine security, but the far reaching tentacles of organised crime syndicates into our operations through employees, contractors and the like rates as our highest concern and therefore commands the majority of our time and energy. Security control measures are therefore mapped around the risks faced and we have, inter alia, instituted task teams within the Protection Services Department to tackle specific threats.”
The threat against the mining industry, according to Lutchman is not restricted to prime product, but includes the theft of copper. “It is widely reported that this is an area where billions of Rands worth of stolen copper is being shipped overseas via the back door to willing buyers. In addition, the theft of explosives from commercial users has increased over the past few years, with a great percentage of it used by the syndicates to commit other crime such as attacks on ATMs.
“We have also seen an increase in the theft of office equipment destined for the second-hand market through so-called legitimate computer stores. This is mirrored in the theft and sale of high-end capital equipment which is sold for a fraction of its true value to unscrupulous buyers on the black market,” he added. “The challenges experienced by the SA Police Service to regulate the Second Hand Goods Act, exacerbates the situation.
“Apart from the physical deterring and detection of theft of assets, one of the biggest challenges we face is the identification of employees who have been compromised by the syndicates. We have a very comprehensive screening process in place and all our employees have received training in the identification of possible threats to our security. We have implemented a whistle-blower hotline and a confidential e-mail facility, administered by Deloitte & Touche and we are pleased to report that a high percentage of all alleged criminal incidents are validated crimes, but collusion and apathy amongst employees to name-and-shame deviant colleagues remain a concern,” said Lutchman.
He explained that there are two defined areas of operation within a mine – the shafts from which ore is extracted and the process plants where the ore is refined. “Both areas are high risk and although we have a common security framework in place, the control measures applied to each environment does vary.
“On a very elementary level, one needs to consider that a mine may have many shafts which are spread over a large geographical footprint. To simply place a perimeter fence around this entire area is not feasible. Add to this the fact that in some instances, major roadways actually intersect the mine property, then it becomes clear that other security measures need to be implemented for success,” Lutchman said.
Where perimeter security is uncompromisingly important though is at the processing facilities. “The perimeter security comprises several layers of physical security, guarding and patrols; all of which are accompanied by several fit-for-purpose technological protection applications,” Lutchman explained.
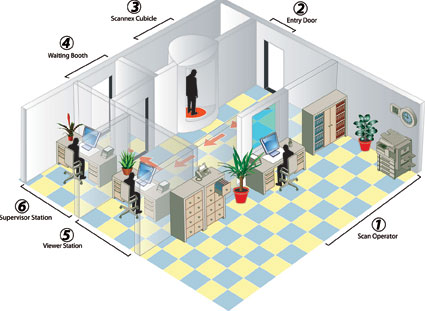
Gordon Crundwell, security operations manager for Gold Fields Protection Services, added that the biggest challenge with perimeter security is the number of false alarms received. “This occurs for a number of reasons and we spend a lot of effort in managing our false alarms to acceptable levels. We operate on what is termed a flasking methodology of access control. In essence, this means that we have a single point of entry and exit at the plant where employees are subjected to, in some instances, biometric access control technology such as fingerprint and facial recognition. In addition, employees as well as any visitors to our facilities, may be subjected to searches, including being scanned by advanced metal detection systems, to ensure that contraband does not enter the premises and unaccounted-for gold does not leave the premises.”
Crundwell said that previously biometric access control systems were difficult to implement at the mineshafts due to the sheer volumes of personnel, on various shifts, within the area. “However, we are instituting a system that to date is producing favourable results. Once again, we rely on facial recognition for compliance and regulation, to ensure that every person who entered the shaft leaves it at the end of the shift. The system is therefore not just intended for security purposes, but also has a human safety element incorporated.
“We can boast that Gold Fields is leading the field in terms of biometric facial recognition access control systems in a mining scenario,” said Lutchman. “This has not been without its trials and tribulations but today we have a superior system that contributes significantly to our overall effort in preventing unauthorised persons from infiltrating our plants and shafts for nefarious reasons. The system utilises live facial recognition in place of the more commonly used picture comparison software. All of our plants run on this system and 40% of our shafts have already been converted to the system, with the remainder being rolled out shortly.”
Crundwell explained that Gold Fields has three tiers within its CCTV environment. Tier 1 consists of on-site live remote viewing, coupled with radio and telecommunications. Tier 2 consists of a centralised control room with the ability to conduct live remote surveillance across any GFL operation in the West Wits area, as well as providing for review and dedicated surveillance functions.
Lutchman added that the Gold Fields emergency response and medical services may in future also be administered from the centralised control room. Tier 3 involves aggressive surveillance of key problem areas and is developed internally within Gold Fields Protection Services while external contractors handle the maintenance of the systems.
“In all our security efforts we acknowledge that even the best technology available to us is of little use if the people element is lacking,” said Lutchman. “Therefore, we insist firstly on systematic screening of all personnel, whether in Protection Services or in general employment. This is supplemented by adequate training in the intricacies of mine security. We regularly bring security human factors specialist Dr Craig Donald on site to determine best fit, with specific regard to protection services electronic surveillance personnel, and to ensure that these employees receive the requisite training.
“Protection Services offers an exclusive holistic and comprehensive security service exclusive to the Gold Fields Group which is structured around frontline protection investigation, information management and security awareness,” said Lutchman. “We are very cognisant of the fact that we do not operate in isolation so we ensure that we keep open channels of communication with industry and the relevant authorities. Since the higher-end syndicates operate outside our mandate we rely to a great extent on intervention from these third parties to assist us in dovetailing our own security initiatives,” Lutchman concluded.
Body talk
In an effort to reduce and eventually eliminate the theft of diamonds from its mining and processing operations, De Beers developed a low dosage X-Ray body scanner some 15 years ago.
Nico van Zyl, marketing manager at DebTech, pointed out that despite contention to the contrary, the Scannex system is safe enough for a person to be scanned up to 200 times per annum. “The recommended maximum dosage for exposure to radiation in non-radiation workers is 1 millisievert while our system produces only 6 microsievert per scan. Each scan is actually the equivalent in radiation exposure to a 2-hour transatlantic flight.”
Initially only available to De Beers facilities, the product has now been commercialised and markets are being pursued in Europe, the Middle East and the USA. “In addition to the diamond mining application, the Scannex can also be applied in gold and platinum mines; airports; the military; prisons and border control,” Van Zyl said.
He pointed out that advantages of the system are the detection of minute particles both on and inside the body; fast processing times (typically 10 seconds per scan) of high volumes of people; and high levels of availability and reliability. Up to four viewers can be connected to the scanner to quickly expedite the required personnel volumes. “Human intervention is essential since we found in our R&D that automation results in too many uncertain detections being recorded and it tends to make the viewers less vigilant.”
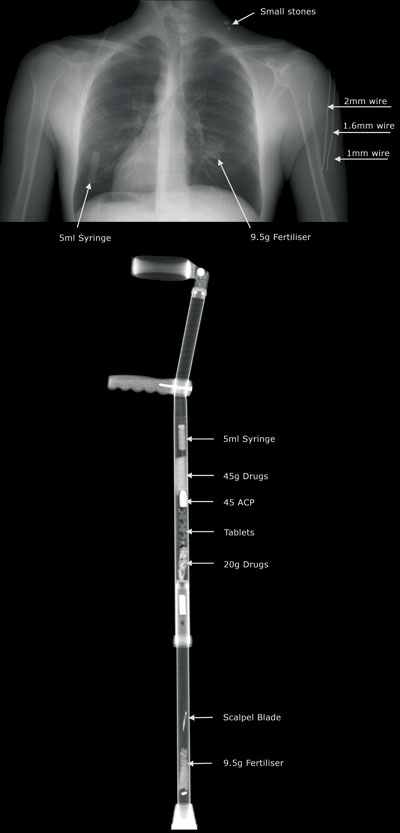
The Scannex is programmed not to display soft tissue but rather to enhance hidden non-bodily items. Images can be viewed as normal digital images, unsharp masked with sharpened edges or in 3D mode with zoom capability. Viewers receive comprehensive training on the human anatomy so they are able to accurately detect foreign bodies within the human body. The training course, developed in conjunction with a local university, equips viewing personnel to make informed decisions regarding suspicious concealed material.
Similarly, the Goldfinger is ideal for use in any application where one needs to detect precious metals and coins. This high-sensitivity, analytical precious metal detection system was first developed in 1994 where the detection of small particles of gold was required throughout the mining industry.
Unlike the Scannex, this is a fully automated system that does not use X-Rays as the mode of detection. “We have eliminated people from the process and a computer, running a sophisticated analytical program, takes over the responsibly for detection of metal particles,” said Bill Young, inventor of the Goldfinger system.
The Goldfinger is able to detect and analyse very small particles based on their shape rather than size. “The principle of operation is that the person walks through the magnetic field within the doorway and the system will detect the presence of metals on his/her body. In order to obtain a benchmark for each person, they are required to walk through the scanner up to four times in order for the interpolation of low and high readings into an average, which forms the baseline for future reference. Any deviation from this baseline will alert the system and security personnel can take action at this stage,” Young explained.
The Goldfinger is equally at home both locally and cross border, with a total of 32 systems installed worldwide, including most of the major mining houses in South Africa. Recent developments include a scanner where a prone person is conveyed through a tunnel and a linear system scans the person as they pass through the magnetic field.
Diamonds are forever
Francois Malan, a director at Camsecure, said that his company has recently completed the technical design, installation and commissioning of a complete surveillance and detection system at a new diamond mine.
“The mine’s management realised at the outset that because of the high yield values inherent at the mine, security would be of primary importance and would remain a key focal area indefinitely for the lifespan of the mine,” said Malan. “As such, they decided that no expense was to be spared and we have secured industry-leading HDTV cameras for production areas and thermal cameras to protect the perimeter of the mine.
“We have also installed solar panels and wireless communication to ensure 100% uptime and availability. In addition, because of the satellite links, we can remotely monitor the installation from Johannesburg and make the necessary adjustments to fine focus the camera lenses.”
The project started two years ago during the worst economic instability the world has seen in many decades. “Despite this factor, the mine’s owners were optimistic that the mine would be a huge success and we pressed ahead with limited infrastructure and no power. By sourcing only the best equipment and contractors for its security requirements, the mine has already eliminated the major theft by employees and outsiders,” said Malan.
The emphasis has been primarily on quality but utilising its experience in the field, Camsecure has provided the mine with H264 video compression, which results in efficient video transmission of high quality images at low bandwidth. This HDTV surveillance system supported by Milestone Systems sends multiple streams to the control room for high quality recording, video analytics and for bandwidth efficient remote monitoring.
The system has been designed with double redundancy so even if the recording system goes offline, onboard camera recording means that footage can be downloaded directly from the cameras.
Full body X-Ray scanners, supplement the surveillance system. “These scanners form an integral part of the whole security portfolio and are the last line of defence against theft,” said Malan.
Due to its remote location, the entire project has been characterised by the need for minimum maintenance and human intervention. “The result is a satellite feed which allows any potential problems to be addressed immediately and maintenance to be facilitated for minimal downtime,” Malan concluded.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.