

The 2019 KnowBe4 African Report across South Africa, Kenya, Nigeria, Ghana, Egypt, Morocco, Mauritius and Botswana has found that people living on the continent are not prepared for the cyber threat and 65% of respondents across all eight countries are concerned about cybercrime.
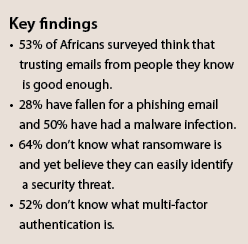
They are vulnerable, as they’re not aware of what they don’t know. From ransomware to phishing to malware and credential theft, users are not protecting themselves adequately because they mistakenly think they’re informed, ready and prepared. Around 55% believe that they would recognise a security incident if they saw one.
Of all the countries surveyed, Kenyans (75%) and South Africans (74%) were the most concerned about the risk of cybercrime and yet respondents were comfortable giving away their personal information as long as they understood what it was being used for (Kenyans 26,59% and South Africans 57%). It’s a worrying trend – many phishing scams will use any means necessary to tease out valuable nuggets of personal information and phone calls or emails from so-called ‘trusted sources’ are among the most common methods used.
The risk of not knowing what I don’t know
The problem is that most users are not aware of how cyber criminals operate and the tools that they use. More than half of respondents across all eight countries felt very confident that they would recognise a security incident or issue if they saw one, but a significant percentage have had a PC infection, and more than a quarter had fallen for a scam. In South Africa, 50% of respondents had their PCs infected, while in Kenya, Ghana and Egypt, this number rose to 67%.
The KnowBe4 survey found that even though nearly half of respondents across all eight countries felt that their organisations had trained them adequately, a quarter of them didn’t know what ransomware was. For South Africans, a worrying 31,5% thought that a cyber threat that encrypts files and demands payments was a Trojan virus and 26,9% of Kenyans agreed. Egypt and Morocco thought it was a drive-by download, while Ghana thought it was a botnet.
More than 50% of respondents are not aware of what multi-factor authentication is or the benefit thereof. Using stolen credentials was the third most common attack vector used in successful breaches and applying multi-factor authentication, which is combining your password with something that you own, such as a one-time-password app on your phone, reduces this risk significantly.
Phishing still number one attack vector
Email security is one of the biggest threats facing the average user, both at work and at home, and it is one of the most common communication methods – more than 70% of those surveyed use email to collaborate with friends and colleagues. Most people don’t realise what a risky email looks like or how their actions can result in their systems becoming infected.
While more than half of respondents in Botswana, Egypt, Kenya, Ghana, Morocco and Mauritius have enough security smarts to avoid clicking on links or opening attachments they don’t expect, a startling 46% still trusted emails from people they knew. In South Africa, those statistics are completely turned around – more than half of respondents (52%) trust emails from people they know, while only 49,5% don’t open attachments they have not expected.
Email remains one of the most successful forms of cyberattack today for this very reason. People are quick to click on links or attachments sent to them from people who they know, not realising that cyber criminals have potentially hacked or spoofed (impersonated) their friend’s, colleague’s or supplier’s systems to spread malware, or launch other forms of attacks. Cyber criminals can easily mimic contact lists or use email addresses that look as if they’ve come from trusted institutions, and a simple click can unleash a ransomware attack that can hold an entire company, government or home hostage.
According to Verizon’s 2019 Data Breach Report, email phishing is still the number one attack vector used in successful breaches; closely followed by malware infections and the use of stolen credentials – both of which are attack vectors commonly accomplished via phishing. Phishing and social engineering attacks are not just limited to email – they have spread to other communication channels such as WhatsApp and the phone. With WhatsApp use at more than 90% in Africa, this is a serious concern.
Phishing myths
Another myth around phishing scams is that they are badly written with terrible language and rude offers. While these still exist, they are no longer the norm. Cyber criminals have become incredibly sophisticated and prey on this lack of understanding. Across all eight countries, more than a quarter of respondents checked for bad grammar and spelling to determine whether or not an email was legitimate. Interestingly, more than a quarter had also clicked on a phishing email. It turns out that yes, Africa has been phished and will continue to fall prey to this insidious attack unless it recognises the need for training and a deeper understanding of security threats.
When looked at against the backdrop of how often they’ve been caught by a phishing email, it’s clear that users still don’t realise how easily they can fall prey to a well-designed email.
The biggest concern is that this lack of awareness around cybersecurity impacts a person’s life, identity and work. Humans are one of the most common causes of a business being held by ransomware or crippled by malware, data breaches or plain financial fraud. Their inadvertent clicking on an attachment, sharing personal information or carrying an infection into work on their mobile device can cause these types of issues.
People have the hots for public hotspots
The survey found that more than 90% of respondents used a smartphone and more than 70% used a laptop computer to connect to the Internet, using either data from their mobile network (more than 80%) or through their home network. However, more than a quarter of respondents connected their devices to the Internet using a free Wi-Fi connection in a public space. This is risky, as cyber criminals make use of public places to trick people into connecting to their malicious hotspot in order to connect to the person’s machine or to steal their information.
Urgent need for security awareness training
For organisations, it has become critical to train employees around security best practices and the various methodologies used by the cybercriminal. People need to stop thinking that phishing and ransomware only happen to other people or big businesses – everyone is vulnerable. One of the reasons why spam continues to rise in quantity is because it works often enough to be of value.
According to the September 2019 Cisco Talos Email and Web Reputation Centre report, the average spam volume for the year was 409,51 billion. That’s compared with the paltry 68,90 billion emails that are legitimate. Spam works because somebody always clicks on the link.
Training in cybersecurity threats, methodologies, entry points and vulnerabilities has become critical for the organisation. This not only helps to minimise the growing risk of human error that’s allowing threats to bypass their complex and powerful security systems, but helps to protect their employees.
The survey has highlighted the areas that are most vulnerable and where people need the most help in learning about cyber threats. Employee training is definitely one of the most important points – employees are not aware of how their use of free Wi-Fi networks can potentially infect the organisation, nor are they as aware of email and phishing threats as they believe. It’s also important to bust some of the most common security myths. Not all malicious emails are badly written, phishing is sophisticated and clever, and mobile devices can be infected. The most common platforms used by respondents to connect with friends and colleagues were WhatsApp (more than 90%) and email (more than 70%), and both of these platforms have been compromised. Educating users on how to strengthen their password practices by applying multi-factor authentication is another easy step to significantly reduce risks.
Education is key to ensuring that employees are aware of the risks, understand the threats and make more concerted efforts to protect themselves from infection.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.