
Securing company data is becoming a more complex task in today’s hyper-connected, perimeter-less world, one that extends well beyond traditional forms of enterprise IT. Nowadays, the proliferation of public Platforms-as-a-Service – such as Microsoft Azure and Amazon Web Services (AWS) – and Internet of Things (IoT) devices are enabling non-IT users to create and link-up devic-es and services outside of the corporate network to bring more capabilities into the organisation, faster.

Think of smart building systems as an example: Wi-Fi-connected security cameras allow security response teams to proactively monitor security camera feeds without having to sit on the premises, or a mini-computer called a Raspberry Pi that automatically adjusts the office building’s air-conditioning based on the outside temperature. Corporate networks were not originally created to incorporate these devices, but the devices create, parse or report on corporate assets and data. You’re right if you think this is risky business.
Welcome to the world of the edge device: the any-platform, anywhere, internet-connected device that pulls data from and pushes data into your company’s network, all-the-time.
Let’s look at securing edges devices and the data they contain by going back to the basics of IT security, namely the CIA model (Confidentiality, Integrity and Availability).
Top three key issues and best practices
1. Confidentiality
The first building block of IT security, confidentiality, also exposes the first risk inherent to edge devices: lack of device and user identity authentication. Because these edge devices make use of open-source platforms or unsecured communication channels, such as 3G or 4G, neither the device or the user is identifying and authenticating itself against the security protocols put in place to protect the organisation’s data and other assets from unauthorised access.
Identity and access management is an important starting point to secure access to sensitive corporate data or business-critical systems. Companies can start with the following best practices to secure both the devices and their data’s confidentiality:
• How devices and users authenticate: Determine which cloud-based authentication platform you can easily integrate into your already-deployed user and device authentication layer, and create a bridge between the two. If you use Active Directory, Azure Active Directory Federation Services (ADFS) could be an option.
• When devices authenticate: Create a device enrolment platform that forces any edge device to be white-listed before it can access any corporate data, such as email or team sites, on the corporate network. Another layer of security can be added, such as multi-factor authentication, to link an authorised user to the device.
• Where devices and users authenticate: You can also look at using perimeter DMZ networks to create ‘safe zones’ in the organisation’s infrastructure to isolate edge devices from the internal network before they authenticate. How and when you do this depends on the purpose and risk profile of the device and the data to which it has access. Different devices have different vulnerabilities, and you need to manage each accordingly.
2. Integrity
Secondly, while the authorised edge device is connected to your corporate network, you want the assurance that no data transmits anywhere else than between the two trusted data sources: the edge device and your data centre. Security risks can be present in how users connect edge devices to the network, such as man-in-the-middle attacks: where data is intercepted, copied and possibly even changed by unauthorised parties.
Here companies can look at making use of their ‘traditional’ IT security knowledge, such as:
• The type of traffic: You want to allow secure traffic protocols into the network through secure ports, and block the rest where possible. Encrypted traffic, such as HTTPS, is a must-use when transmitting any type of sensitive data, such as Personally Identifiable Information (PII) or payment card data. You can use Deep Packet Inspection (DPI) technologies built into reputable firewalls to analyse HTTPS traffic.
• The type of application: Organisations can white-list specific, authorised applications to access and change data. App permissions and privacy settings are important here, apart from knowing that an application is legitimate (be wary of ‘fake’ security programmes for devices, especially on mobile devices). Most reputable security vendors cover application white-listing in their basic device security products.
• The type of device or data: Encrypting devices, such as smart cameras or USB drives, are important to ward off unwanted access and changes to the device’s settings, but it won’t protect the data streaming through the device if the device itself is breached by a determined, expert cybercriminal. Encryption on a data-level is best because it protects data, irrespective of the device on which it is stored or viewed. Data-level encryption is available through a few security vendors, such as Microsoft 365’s Right Management Services (RMS), which is part of its Enterprise Mobility + Security module.
3. Availability
We use different IoT devices in business to collect more data to analyse, to store the proliferating data points, and make the right data available to the right decision makers at the right time. Digital transformation in business – from a device point of view – can be business- transforming or bring the business to its knees if it is not risk-profiled correctly.
When it comes to IoT devices for smart environments, whether they’re industrial OT environments or commercial by nature, here are what organisations can look at to profile their risk and address it accordingly:
• Devices at point of source: Use IoT devices and applications that have been created with security in mind from the start. Layering security products or services on top of a device or application is not ideal, but we need to do it where security has not been embedded in the application’s original coding. IoT vendors, such as Libelium, create smart solutions with seven-factor authentication already embedded into the devices and their applications. They’re therefore secure by design and often multi-functional, which reduces the number of devices needed to do the job in the first place.
• Devices at point of storage: We often have the discussion with clients on on-premise vs. hybrid vs. cloud data centres and the return on investment (ROI) of each. High-availability platforms that enable staff to access data anytime, from anywhere, doesn’t have to break the bank. For example, if you configure your data centre correctly, especially your hybrid or public cloud data centre, users would be able to self-provision services that are inherently more secure.
Where does one start?
The above list of best practices is not comprehensive, which is why I understand that some people have infamously labelled IT security as a ‘black hole’. The good news is that securing edge devices and data can be done efficiently when you have your priorities straight. South Africa’s economy is also currently between a rock and a hard place, which means that spending money on the business has to be smart: know where your business risks overlap with security risks, approach security projects by understanding the problem first, and then tackle problems in phases based on their priority.
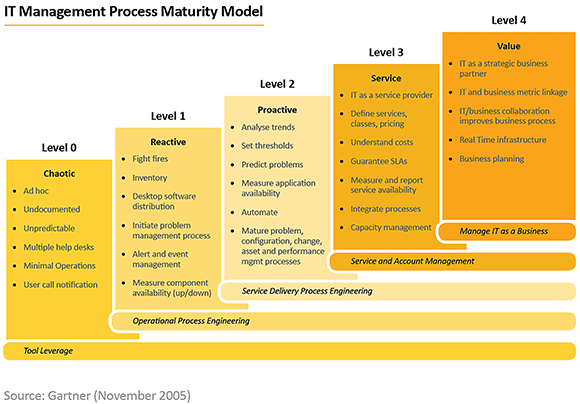
For companies in the beginning of their IT security maturity journey, we recommend an information security risk assessment (https://aves.co.za/services/it-security/risk-assessment/). Here we map the organisation’s knowledge of their people, process and technologies against the international ISO 27001:2013 standard on information security. Even if companies are not looking at becoming ISO 27001-compliant in the short term, it can help them identify and prioritise their risks using the standard as a guideline. It’s suitable for any sized organisation in any industry.
For the companies further along their IT security maturity journey, we recommend a vulnerability assessment (https://aves.co.za/services/vulnerability-management-services/) to identify security vulnerabilities in the network, across devices, to pinpoint the most critical operational risks of their IT infrastructure. We recommend you do this before ordering a penetration test (also called pen test) on the environment: understand the problem before you test your security solutions’ resilience against attacks. It’s also suitable for any sized organisation in any industry.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.