

Cameras, door controllers, and other physical security devices and systems are smarter and more powerful than ever before. As part of both public and private networks, they are increasingly interconnected. This facilitates their management, speeds up communications, and increases collaboration. Most importantly, they help security professionals keep people and organisations safe.
But this growing connectivity doesn’t only carry benefits. Emerging cyber threats, hazards, and criminal activity introduce new vulnerabilities and risks.
A poorly secured camera, unencrypted communications between a server and client application, or out-of-date firmware can all be exploited by cybercriminals. The result is clear: security systems can no longer focus solely on physical threats.
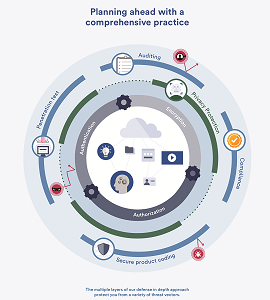
That’s why we believe that it is critical to have a security strategy to protect your system against both physical and cyber threats. Our solutions give you the tools you need to build a secure and compliant system. Because no single approach is enough, they include multiple layers of defence, such as encryption, multi-factor authentication, and authorisation. From devices to data storage on premise or in the cloud, we help you face new threats and keep your data and operations safe.
The growing risks of an interconnected world
Cybercriminals can cause massive disruption to the activities of both organisations and governments. In 2017, a major ransomware attack, known as WannaCry, affected people and organisations around the globe. It targeted systems running common, but outdated software. As a result, more than
230 000 computers in 15 countries were locked. To regain access to their data, organisations and users had to pay a large sum to the perpetrators. In many hospitals, medical records became encrypted, disrupting operations and threatening patient lives.
Emboldened cybercriminals have also increased the scope of their attacks, targeting private security cameras to access live video. While some of these attacks exploit simple vulnerabilities, such as default manufacturer passwords, others are more sophisticated and complex. Whether at work or at home, preventing strangers from accessing your cameras is no longer a simple affair.
With greater connectivity of systems over the Internet, a vulnerable device can become a gateway to your organisation’s data and sensitive information. Now, when you protect your physical security system, you are also working to safeguard all of the other systems and the information that is connected to the network. To achieve this, you need a new approach: a defence-in-depth strategy.
Developing a defence-in-depth strategy
As with any interconnected entity, security systems can be targeted. Hacking a security system can take any number of forms, including brute-force, packet-sniffing, and man-in-the-middle attacks. In some cases, cybercriminals are able to listen in and alter communications, even while users believe their system is secure. This variety of attack strategies requires an equal variety of defence layers.
At Genetec, we provide secure, audited and compliant solutions that help you protect privacy without compromising security. We help you incorporate multiple and varied lines of defence, otherwise known as a defence-in-depth cybersecurity strategy, to face common and emerging threats, and secure your environment. Data captured by our unified security system for management, analysis, and storage, is protected by strong encryption, authentication, and authorisation methods.
We work hand-in-hand with international associations to ensure that our solutions meet industry standards and adhere to the latest cybersecurity best practices. Penetration tests and audits are routinely conducted on our products to provide a complete assessment of the integrity of our solutions.
Make the information available to the right people
When it comes to protecting data, threats aren’t just coming from the outside. With more integration and collaboration between each part of our security systems, the paths to accessing sensitive data have multiplied.
That’s why you need to control who can see your data, and what they can do with it. The first step is to use strong authentication methods to prevent undesired access to your system. This keeps your video and data from getting into the wrong hands.
Once authenticated, the next step is to use authorisation to manage who can access what part of your security system. This allows you to restrict the scope of activity within the system by giving access rights to groups or individuals for resources, data, or applications, and by defining what users can do with these resources.
Keep out prying eyes
We help protect your data from malicious attacks in multiple ways. When we talk about the ‘security-of-security’, we’re talking about securing all aspects of your physical security system – including communications, servers, and data.
Video and data viewed and stored within our system, as well as communications with Genetec hardware, are fully encrypted. We also secure communications between our software and edge devices, and to the cloud. This way, even if an unauthorised person gained access, they wouldn’t be able to make sense of the data without the encryption key.
Protect everyone’s privacy
Looking after individuals and equipment often requires collecting personal data and monitoring public spaces. To meet regulations and public expectations, access to personally-identifiable data and footage needs to be controlled. By following a privacy-by-design approach, we make sure that you don’t have to choose between protecting the privacy of individuals and their physical security. Our products let you manage the access to sensitive data and allow you to protect the identity of anyone captured on video.
We ensure you have complete control over your data so that you can adjust your protection methods and processes to meet regulations such as the European General Data Protection Regulation (GDPR), and more importantly, build trust with your customers.
The human element
As important as technology is in protecting your organisation against cybercriminal activity, there is another factor at play: your people. The strongest encryption cannot defend your system against weak or compromised passwords. That’s why it’s important to implement the right processes and put proper training programmes in place. You need to educate employees on the IT best practices, and potential social engineering techniques they may face. For example, starting with simple tips on password creation, and ways to identify phishing emails from legitimate communications, will help mitigate the cyber risks.
As a provider of security, operations, and business intelligence solutions, we help you protect your organisation. We work tirelessly to inform you of new threats and help you close down vulnerabilities. We continue to work with our customers and partners to deliver solutions that provide the best protection now, and in the future.
Visit the Genetec Trust Centre to learn about our approach, and how we help secure your system, at genetec.com/trust
For more information contact Brent Cary, Genetec, bcary@genetec.com, www.genetec.com
Article supplied by Genetec. The original article can be found at https://resources.genetec.com/cybersecurity-2/security-of-security-brochure
| Email: | qroberts@genetec.com |
| www: | www.genetec.com |
| Articles: | More information and articles about Genetec |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.