
In terms of interoperability, it is common knowledge that electronic security systems have not evolved at the same rate as information technology and telecommunication systems. With the advent of IP this has started to change, but at a far slower rate than expected. Even though an attempt at implementing standards is underway, it is driven mostly by manufacturers rather than independent third-party organisations.

According to Bernard Senekal, Naxian Systems director, interoperability is therefore very much the Achilles heel of the electronic security industry. “This ‘ransomware’ approach, where manufacturers lock clients into bespoke solutions and closed system architectures has created dissonance between the electronic security industry and the world of technology at large.
“Combine this with the fact that the electronic security industry has no real regulatory barriers to entry and you have a knock-on effect that translates directly into a reactive, antiquated method by which systems are supported and maintained.” This, he continues, is the case for small through to large enterprise systems, the result of which is the negative impact on the cost of maintaining systems by implementers as well as the creation of unnecessary risk and operational inefficiencies, due to system downtime for end users.
The secret, Senekal believes, is the provision of a safe passage between interoperability and electronic security systems. Naxian Systems’ IoT (Internet of Things) platform, Synapse, provides the bridge that allows a quick way to cross from this sinking island onto the technology mainland.
The challenge is that technologies that allow for predictive and preventative maintenance are not available to the mass market inside the security industry. Naxian is changing this with its smart services offer.
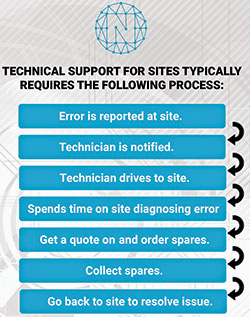
Senekal points out that technical support for sites typically requires the process outlined in Figure 1. The cost in productivity, operational efficiency and increased risk in the above scenario is based on the following:
• The time between when the incident occurs and when it is reported
• The time between when the incident is reported and the technician is able to visit the site
• The time taken to diagnose and determine the root cause of the problem
• The time to source and collect the necessary resources and return to site in order to resolve the issue and bring the system online again.

Naxian Systems’ Smart Services Platform (SSP) introduces a combination of Internet of Things (IoT), Artificial Intelligence (AI) and Deep Learning technologies to ensure the scenario outlined in Figure 2. Ultimately, this results in:
• The right technical resource, with the correct spares and full diagnostic being deployed to site,
• Inside the correct time frame,
• With the predictive ability to ensure that technical resources are notified of things that will go wrong, before they actually go wrong.
Monitoring and managing system and device health
So how exactly does it work? “First and foremost, this is a software solution that allows for any security and/or networkable device to be connected to a cyber secure and hosted/cloud environment from where Naxian’s Smart Services Centre collects the relevant system and device health data. The processing of the data occurs in the cloud while the output and results are managed securely inside the secure SAIDSA-approved control room environment. The platform is completely product- and discipline-agnostic,” says Senekal.
Operators who are proficient at dealing with electronic security and information technology systems manage the risk of the system and device health through automated monitoring and the issuance of responses back to allocated technical resources, who can respond to the issue with a complete diagnostic and problem resolution listing.
Naxian’s Everywhere application allows for users with mobile devices to receive events, acknowledge the receipt of these events and then have performance measured against SLAs or an acceptable response and resolutions set for the client or site. A technical support call cannot be flagged as ‘COMPLETE’ unless Naxian’s Artificial Intelligent agent, Annie, accepts the resolution of the technical issue that was reported.
Before a support ticket is allocated to a resource, Annie will survey the geolocation of the closest technical resources available to assist with the problem. Based on her understanding of the timeframe allowed to acknowledge, respond and resolve the incident, she will consider the profile and historic performance of the technical resources available. She will then allocate the best available resource to resolve the category and incident type for the specific system in question and provide route optimisation based on Google Map analytics for the resource to make his way to the site.
Reporting will indicate strengths and weaknesses of technical resources in order for skills development activities to be planned and customised for resources. Senekal says that the company is currently investigating an e-learning platform that will automatically suggest courses designed specifically for the needs of a group or individual resources.
Future Naxian Systems services will include:
• Video analytics as a service for:
- Retail
- Perimeter security
- Traffic management
- Logistics and supply chain environments.
• Process visualisation as a service (the integration of video surveillance and analytics into business process systems such as warehouse management, HR, ERP, CRM, scanning and RFID).
• Real-time incident backup into the cloud.
“In an industry where your relationship is as good as your last technical support call, we see this service as ground breaking, disruptive and a non-negotiable for any forward thinking electronic security company,” says Senekal.
For more information contact Naxian, +27 (0)87 820 0620, bernard@naxian.co.za, www.naxian.co.za

© Technews Publishing (Pty) Ltd. | All Rights Reserved.