
Deterring and stopping criminal intrusion requires a manifold multi-tiered approach which begins with the boundary, represented by a wall or electric fence. In terms of the latter, technology and regulations have advanced and end-users need to be aware of what is deemed an acceptable installation.
The traditional electric fence technology available includes an energiser that is connected to the wires on the fence. Supplementary advanced perimeter intrusion detection systems (PIDS) include fibre detection, acoustic detection, taut wire detection and motion (seismic) sensors.
Electric fences now include high-voltage pulse detection systems or low-voltage ‘low-feel’ or ‘no-feel’ detection systems. With regard to all these systems, it is advisable to look for both the SABS approval mark and SANS specifications relating to 10222-3 for electric fencing. This in essence, will determine how many joules an energiser should emit, the quality levels and the duplication of components to ensure failsafe operation in the event of failure of a specific component.
Maurice Williamson at Stafix says that an electric fence can be multi-zoned and multi-sectored. The latter means that there will be more than one energiser on the fence line powering more zones and then these zones are sub-divided into many sectors. The more zones and sectors a fence has, the better the security level will be because this will reduce reaction time for the guard monitoring company since they can target their response more accurately.
The monitored electric fences can then be linked to a product such as JVA Perimeter Patrol which can monitor, record and report back numerous fence line conditions such as fence line voltages, amperages, faults, and reaction times.
Users must ensure that the electric fence product chosen has a COC (Certificate of Compliance) certifying that it complies with SANS 60335/76 and this certificate must be issued by an internationally recognised test laboratory (in South Africa, Test Africa is the only company certified to carry out these tests) and furthermore the product must have an LOA (Letter of Authority) issued by the National Regulator for Compulsory Standards. These latter two are requirements legislated for in the Department of Labour Health and Occupational Safety Act of 1993.

Communications and quality count
According to David Mossop at Gallagher, the period of warranty offered by manufacturers is a great indicator of the quality of the system, with five years being the ideal. In addition, he says, the physical appearance of components gives an insight into the overall quality of the rest of the product.
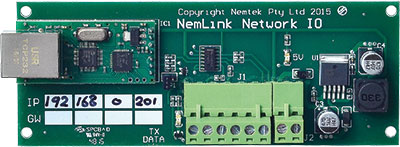
Garreth Osborne of Nemtek adds that it is advisable to consider networkable solutions, this can be achieved by using the Nemtek Nemlink card which provides an Ethernet interface for the Druid two-zone energisers and Druid FG controller to be distributed over TCP/IP Ethernet networks. The key here is a focus on simplicity of installation, operation and maintenance.
“The Nemtek taut wire system measures tension changes in a particular direction on an electrified or non-electrified fence, and will set off an alarm if the wires are cut or if there is an attempt to part the wires in order to gain entry. The combination of a taut wire and monitored electric fencing system provides a high level of security, from both a detection and a deterrent angle,” he adds.
According to Puffer Hartzenberg of Elf Rentals, a trend that is becoming more common is the adoption of the all-live-wire configuration, whereby every single wire strand carries an electric current and has cut protection, rather than the alternating live wire/neutral wire systems of old. He believes that no matter the system used, it is imperative that the technology is locally and freely available, thereby ensuring support and maintenance of systems.
References count
Mossop is adamant that the first step in the deployment of any electric fencing system should be the appointment of a consultant who will determine risks then advise on solutions through the best choice of technology and supplier, as well as provide suggestions on an appropriate installer. By chatting to manufacturers and other residential estates for installer recommendations, one can save a lot of time and heartache in the long run.
It is important to note that, under new regulations, only an installer who is certified as an Electric Fence Installer (to ensure compliance in terms of SANS 10222-3) may provide an installation certificate. The certified installer is required to work through seven units standards set out by SAQA to prove his competency and a RPL (recognition of prior learning) process is required.

Therefore, if you appoint Joe Bloggs to install your electric fence and he is not certified, should a person be injured by the electric fence, then there would be a liability claim against the estate since they did not acquire a COC. A certified installer can, however, check and sign off an installation undertaken by the unlicensed Joe Bloggs, but the installer then accepts liability for the installation and its compliance.
Certification is essential
It is advised that one asks an installer to produce an official letter headed: ‘Occupational Health and Safety Act (Act 85 of 1993) Electrical Machinery Regulation 14: Issuing of Certificate of Registration’. This document will also contain the installer’s name, ID number, and his registration number. These particulars can then be verified with the Department of Labour.

The fence COC certifies that the fence has been erected in accordance with the specifications set out in the SANS 10222/3 standards applicable at the time the fence was erected. Any fence erected after December 2012 must comply with SANS 10222/3 2016 Edition 5.
A fence COC, once issued, is valid indefinitely as long as no additions or modifications are made to the fence. However, should the owner of a property with an electric security fence wish to sell his property, the COC must be less than two years old. If older they will need to have the fence recertified.
“It is important to note that an estate must have a COC for their electric fence, which is the property of the body corporate or whoever owns the estate. However, should a homeowner have erected their own electric security fence within the estate then they are individually responsible for producing a COC, which is less than two years old,” says Williamson.
Good working order
It is agreed that the longer the warranty period on electric fence components, the better the equipment is deemed to be. Similarly, instituting both a service level agreement (SLA) and a maintenance agreement will provide the estate with the assurance that the system will remain operable irrespective of attempts at intrusion and the ambient environmental conditions. The more comprehensive and detailed these contracts, the more likely it is that the installer is competent and experienced.
Preventative maintenance should be the order of the day to enable installers to schedule the cleaning of the fence, removal of any vegetation interfering with the fence, checking of component wear and corrosion, together with periodic replacement of these components.
An SLA should include what the installer can be expected to do in a failure event in terms of stockholding of critical spares and their response times in terms of the specific geographical areas in which the estate and installer are located.
The inclusion of a checklist in the maintenance agreement or contract is another indication of a good installer. This contract should cover things such as call-out conditions (charge rates for non-warranty call-outs, number of free call-outs, etc.) and provisions for monthly and annual servicing (tensioning of wires, tightening of line clamps, and checking of fence line hygiene).
Any reputable manufacturer should have a service department capable of servicing any fault encountered with their system.
Conclusion
In Hartzenberg’s words, when selecting an electric fence installer, the requirement can be succinctly put in only three words: “Word of mouth”. The installer should be contactable and have excellent references. He should hold certification as a registered Electric Fence Installer and he should be installing products which have been selected to suit the environment and which are characterised by durability, reliability and longevity. Finally, maintenance of electric fences remains a critical element in the ongoing operability of the system, ensuring that it will remain working when it is truly needed.
Certifications for fences
• The Occupational Health and Safety Act (Act 85 of 1993) – Electrical Machinery Regulations 2011 Schedule 12 Electric Fences.
• The South African National Standard – SANS 60335 Part 2-76 2006. Particular requirements for electric fence energisers. These standards apply mainly to the manufacturers of electric fence energisers and if the energiser has a Certificate of Compliance these regulations are satisfied.
• South African National Standard – SANS 10222-3:2016 Edition 5. (These are the standards applicable to the security electric fence itself and are the specifications the installer should adhere to in order to issue a Certificate of Compliance for the fence.)
| Tel: | +27 11 543 5800 |
| Email: | malckey@technews.co.za |
| www: | www.technews.co.za |
| Articles: | More information and articles about Technews Publishing |

© Technews Publishing (Pty) Ltd. | All Rights Reserved.