

Places in the Internet where cybercriminals converge to sell and buy different products and services exist. Instead of creating their own attack tools from scratch, they can instead purchase what they need from peers who offer competitive prices. Like any other market, the laws of supply and demand dictate prices and feature offerings. But what’s more interesting to note is that recently, prices have been going down.
Over the years, Trend Micro has been keeping tabs on major developments in the cybercriminal underground. Constant monitoring of cybercriminal activities for years has allowed it to gather intelligence to characterise the more advanced markets seen so far and come up with comprehensive lists of offerings in them.
In the Russian cybercriminal underground market’s case, the huge demand for credit card credentials drives prices up. Then again, incidents such as the massive breaches involving popular retailers a few months ago, which increased the supply of such credentials, drive prices down.
Unlike legitimate business-people, however, cybercriminals need to keep their identities secret and, as much as possible, hide all traces of their “business” transactions. Factors like this make real-time transactions almost impossible to do in the underground market. That said, business dealings in cybercriminal underground markets are much slower than in the legitimate business world.
Extracted from its latest report, Trend Micro offers some insight into the Russian cyber underground.
Quick facts
* Established in 2004, the Russian underground market was the first to offer crimeware to cybercriminals.
* Russian underground forums are growing. The most popular ones like verified.su and ploy.org have at least 20 000 unique members to date.
* To ensure their safety in underground forums, buyers and sellers use escrows, third parties who test the sellers’ products and services, and check the buyers’ ability to pay. In return for their services, they get 2-15% of the sales price.
* The prices of products and services available in the Russian underground have gone down over the years due to automation.
* Boutique or specialised offerings remain expensive because of the skill and knowledge required in their development. These offerings characterise the Russian underground market.
* Traffic-related products and services are the most-sought-after goods in the Russian cybercriminal underground market and so fetch the highest prices.
Russian underground offerings
Products
1. Credit card credentials (per card) – see Table 1.

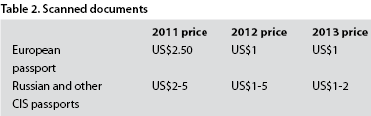
2. Scanned documents – see Table 2.
3. Trojans
* Disguised as legitimate programs or apps, can be used as spyware designed to steal user data, or key loggers that track victims’ keystrokes.
* Stolen data like ICQ passwords, contact lists, confidential documents, and bank account numbers can be used or sold for other malicious purposes.
* ZeuS and SpyEye – 2011 price: US$120 and US$500, respectively; 2013 price: FREE.
* Phoenix Trojan – 2011 price: US$500; 2013 price: US$0-35.
4. Exploit kits
* Insert code to vulnerable programs then download and execute malicious code – 2011 price: US$700-1,000; 2013 price: FREE.
* Exploits bundles – special scripts that combine several exploits; often encrypted to avoid detection. There are two kinds:
1. Intelligent – determines a victim’s browser and OS version then downloads the appropriate exploits.
2. Unintelligent – downloads all exploits in a bundle regardless of the victim’s browser version.
* Cross-site scripting (XSS) exploit – uses vulnerable servers to force a browser to execute malicious scripts when a victim visits an infected website. XSS attacks expose a victim’s data, making him prone to identity theft and data loss. There are two kinds of XSS exploits:
1. Active – automatically executes malicious code.
2. Passive – requires a victim’s participation, usually through social engineering.
5. Rootkits
* Hide any evidence (e.g., processes) of a malicious software’s presence in a computer.
6. Traffic
* The stream of visitors to a website; an increase in traffic increases a site’s SEO ranking.
* Business traffic from Australia, the United States, the United Kingdom, Germany, and Italy are most in demand.
* As of 2013, 1000 installations are sold for US$50-130 in the United States, US$40-170 in Europe, and US$90-200 in Asia.
7. Crypters
* Conceal infected files or malware from security software using crypter stubs, which decrypt encrypted pieces of malicious code.
* Static crypters – decrypt a file and only produce one specific output file; sold with add-ons; 2011 price: US$30-80; 2013 price: US$10-30.
* Polymorphic crypters – decrypt a file and produce several output files; 2011 price: US$100; 2013 price: US$65.
Services:
8. Dedicated-server-hosting services
* A dedicated server is one that can be rented for various dedicated purposes like acting as a C&C server or a drop zone for malicious files.
* Comprise the most in-demand products in the Russian underground.
* Low- to high-end server hosting – 2011 price: US$160-450; 2013 price: US$50-190.
9. Proxy-server-hosting services
* A proxy server is an intermediate computer that serves as proxy or mediator between a computer and the Internet. It is used to keep a hacker’s anonymity.
10. VPN-server-hosting services
* Encrypt all incoming and outgoing traffic to and from a computer.
* Average price – 2011: US$22; 2013: US$15.
11. Pay-per-install services
* Pay-per-install is a business model where customers pay the service provider to distribute their malicious files through hosting sites.
* PPI services are often offered based on the target country.
12. Denial-of-service (DoS) attack services
* Using specially crafted bots or botnets, DoS attacks paralyse websites or computers: 1-hour DDoS attack – 2011 price: US$4-10; 2013 price: US$2-60. 24-hour DDoS attack – 2011 price: US$30-70; 2013 price: US$13-200.
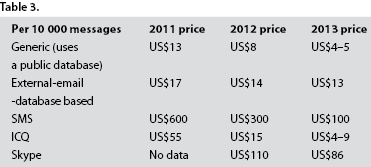
13. Spamming services
* Allow mass distribution of messages via email, instant-messaging (IM), social networks, or SMS.
* Spam can either be themed, which have a specific target audience, or unthemed, which don’t. See Table 3.
14. Flooding services
* Flooding is a routing technique used for DoS attacks to bring down a network service: Email (per 10 000 messages) – 2011 price: US$30; 2013 price: US$2.
15. Malware checking against security software services:
* Allow cybercriminals to check if their malicious files are detected by popular security products.
* Scan4You.net is one of the more popular anti-malware-checking service providers: 2011 price: US$50; 2013 price: US$30.
16. Social-engineering and account-hacking services:
* Account-hacking services are heavily advertised in the Russian underground. The most common targets are email and social media accounts.
* Brute-forcing services involve guessing someone’s password using automated programs, the most popular of which are Brutus and Hydra.
* Account hacking via social engineering services involve cybercriminals guessing the answer to an account’s secret question. See Table 4.

For more information, download the research paper: http://www.trendmicro.com/cloud-content/us/pdfs/security-intelligence/white-papers/wp-russian-underground-revisited.pdf

© Technews Publishing (Pty) Ltd. | All Rights Reserved.