
Working on electrical installations can be dangerous as those that are not properly connected or maintained pose a serious risk to both people and property, and can lead to injuries or even death. For this reason, DEHN Africa has adopted five safety rules according to the German standard series DIN VDE 0105 to help prevent electrical accidents.
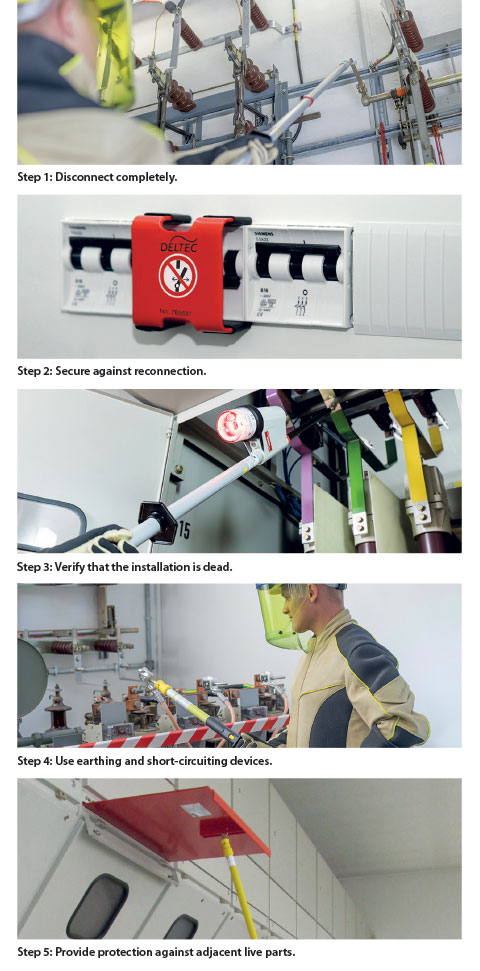
Step 1: Disconnect completely
When working on an electrical installation, it is best to ensure that it is disconnected from live parts on all poles.
Step 2: Secure against reconnection
To prevent an accidental reconnection of an installation where work is in progress, you need to replace the unscrewed fuses in the low-voltage system with lockable lockout devices, or ensure that all breakers on the off position are locked and adequate warnings are placed.
Step 3: Verify that the installation is dead
To verify that the installation is dead, you can use suitable test equipment such as a voltage detector to verify on all poles that the installation is dead. You also need to check the correct function of the voltage detector prior to using it.
Step 4: Use earthing and short-circuiting devices
After verification, connect the cables and the earthing system with short-circuit-proof earthing and short-circuiting devices. It is also important to ensure that the relevant parts must be earthed before they are short-circuited. Only after a successful application of the earthing and short-circuiting devices can the installation be considered dead and safe to work on.
Step 5: Provide protection against adjacent live parts
According to the five safety rules, adjacent parts are located in the vicinity zone. If parts of an electrical installation in the vicinity zone of the work location cannot be disconnected, additional precautions must be taken before work is resumed. In this case, it is essential to use insulating protective shutters or covering material as protection against any accidental contact.
For more information contact DEHN Protection South Africa, +27 (0)11 704 1487, alexis.barwise@dehn-africa.com, www.dehn-africa.com.

© Technews Publishing (Pty) Ltd. | All Rights Reserved.